Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
Avaddon, a notorious Ransomware-as-a-Service (RaaS) that emerged in early 2019 was known for its double-extortion tactics. It not only encrypted victims’ files but also threatened to release stolen data publicly. Avaddon’s modus operandi involved targeting a diverse range of sectors, including healthcare, government, financial services, legal, hospitality, education, and retail. Interestingly, while Avaddon was active, some of its affiliates focused on individual targets rather than large corporations. The ransomware had built-in mechanisms to avoid attacks in certain countries of the former Soviet Union, mainly those still aligned with Russia.
However, in 2021, Avaddon ceased its operations, and decryption keys were released to all its victims. This cessation marked the end of one threat but paved the way for another. NoEscape Ransomware surfaced in June 2023, and its tactics and operations bore a striking resemblance to Avaddon. The similarities between the two are not just coincidental.
The cybercriminal landscape is ever-evolving, and as one threat diminishes, another rises, often building upon the strategies and tactics of its predecessors. This article delves into the targets and latest activities of NoEscape Ransomware.
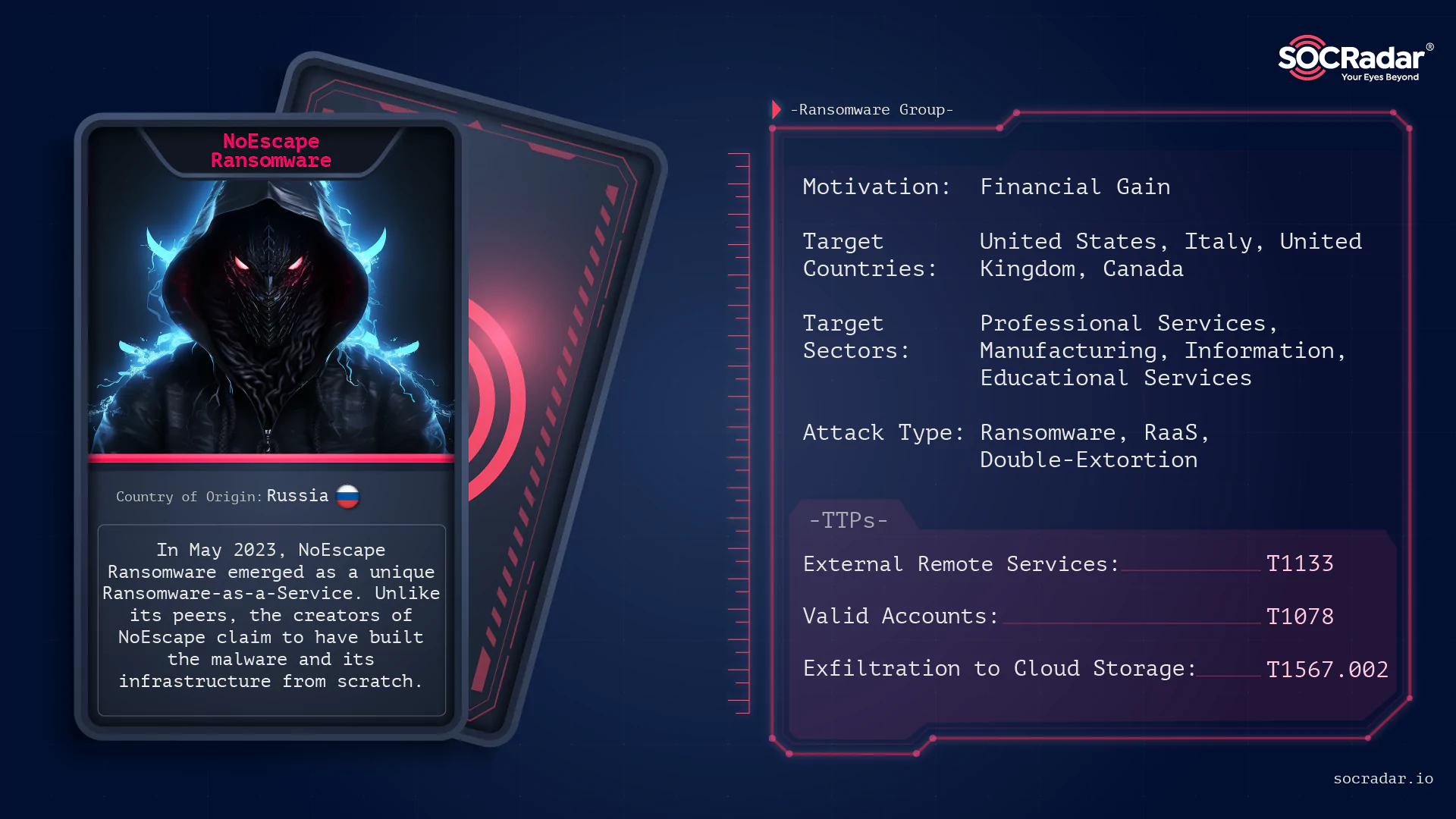
NoEscape Ransomware surfaced in May of 2023, distinguishing itself as a Ransomware-as-a-Service (RaaS). Unlike many of its contemporaries, the developers of NoEscape assert that they have constructed the malware and its associated infrastructure entirely from the ground up, deliberately avoiding the use of source code or leaks from other established ransomware families.
Presently, NoEscape RaaS operators furnish affiliates with a comprehensive platform that facilitates the creation and management of payloads tailored for both Windows and Linux operating systems. Furthermore, NoEscape is recognized for its multi-extortion tactics, maintaining a TOR-based blog to publicly list its victims and display the exfiltrated data of those who resist meeting their demands.
NoEscape ransomware operates as a Ransomware-as-a-Service (RaaS), which means it provides a platform for affiliates to build and manage ransomware payloads. These payloads are designed for both Windows and Linux systems. The ransomware’s operation is based on a shared-profit model. For instance, any ransom collected over $3 million USD results in a 90/10 split in favor of the affiliates. The percentage changes with lower ransom amounts, such as an 80/20 split for a one million dollar payout.
In terms of its technical capabilities, NoEscape ransomware supports multiple encryption modes, including full, fast, or strong. It leverages encryption algorithms like RSA and ChaCHA20 for file encryption. The ransomware has features like process termination, safe-mode operation, spreading and encryption over SMB or DFS, and the use of the Windows Restart Manager to bypass any processes that might block the encryption process. A unique feature is the shared encryption, which allows a single encryption key to be used across all infected files in a network, facilitating efficient encryption and quick decryption if the ransom is paid. Victims of the ransomware find notes titled “HOW_TO_RECOVER_FILES.TXT” in each folder with encrypted files.
Encrypted files are appended with a ten-character identifying extension, such as “.CCBDFHCHFD” or “.CBCJDHIHBB”.
There are separate variants of NoEscape for Linux and Windows, we gathered two samples from open source that were developed for Microsoft Windows.
The hash values of our samples are in order:
When we check the properties of our samples, we see that they are developed with C++:
Looking at the entropy values and pack statuses of Sample A and Sample B:
We continued our analysis on Sample B because it was not packed, but we also observed the behavior of Sample A.
When we checked the DLLs contained in Sample B, KERNEL32.dll, SHELL32.dll, and CRYPT32.dll caught our attention, and we decided to look at the imported APIs:
We observed that Sample B used the EtwEventWrite API, part of the Event Tracing for Windows (ETW) framework. This discovery has led to speculation that the malware might generate ETW events to avoid detection, as these events can mask malicious activities among genuine system processes. By doing so, the malware could secretly exfiltrate data through ETW events, potentially mislead security experts with deceptive events, and reduce its detectable footprint on the system. Using the EtwEventWrite API presents a significant challenge for cybersecurity defense mechanisms.
The IP addresses that NoEscape Ransomware’s Sample B connects to during operation (not necessarily malicious IPs) are shown in the image below:
Several key points highlight the connection between Avaddon and NoEscape:
In conclusion, while NoEscape presents itself as a new threat, its roots can be traced back to the Avaddon ransomware gang.
Looking at NoEscape’s TOR page, we can see that there is a logo with a lock icon (meaningful) and victim announcements list at the entrance:
In the Archive tab, it is seen that there are leaked data and company details listed:
Leak data sharing is partial and there is a continuous countdown cycle in every claim page:
In the Contact Us section, there is a download link for access via TOX and a form where you can fill in your information for NoEscape to contact you:
If you are a victim of NoEscape, the TOR address in the ransom note takes you to a platform where you can enter the victim ID (personal ID) assigned to you for negotiate the ransom:
When observing the NoEscape’s attacks, it can be inferred that it mostly targets the organizations operating in the Professional Services, Manufacturing, and Information (mostly in Telecommunications) fields.
Looking at the countries where the organizations affected by NoEscape Ransomware are located, it can be inferred that it is mostly active in North America, Europe,and Southeast Asia.
When the country distributions are analyzed, we conclude that the United States (about 25%), Italy (11%), United Kingdom (11%), and Canada (about 7%) are targeted more than other countries, respectively.
Infinity Construction Company:
Iina Ba, Inc:
NoEscape Ransomware has rapidly emerged as a formidable threat in the cybersecurity landscape. Its evolution and tactics signify the adaptability and resilience of modern ransomware groups. While it is believed to be a rebrand of the Avaddon ransomware gang, NoEscape has carved its niche with unique features and aggressive extortion methods. The ransomware primarily targets Windows and Linux machines and has even shown compatibility with VMware ESXi. Its encryption methods, combined with its double extortion tactics, make it a significant concern for businesses and individuals alike.
The recent activities, including the imitation by other threat actors, highlight the prominence and influence of NoEscape in the cybercriminal community. However, with proactive cybersecurity measures, regular backups, and awareness, individuals and organizations can mitigate the risks posed by such ransomware.
To safeguard against NoEscape Ransomware and similar threats, consider the following security recommendations:
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
