
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
[Update] August 8, 2024: “BlackSuit Ransomware Extorts Over $500 Million in Ransom Demands”
BlackSuit ransomware is a rebranded version of the notorious Royal ransomware, which emerged due to heightened law enforcement actions against the original group. This rebranding signifies a strategic shift aimed at evading detection and continuing their cybercriminal activities under a new guise. The Royal ransomware, now BlackSuit, has a notorious history of targeting high-profile sectors and demanding substantial ransoms.
BlackSuit’s logo
BlackSuit first emerged in May 2023 and appears to be closely linked to the Royal ransomware gang, which itself originated from the remnants of the infamous Conti group.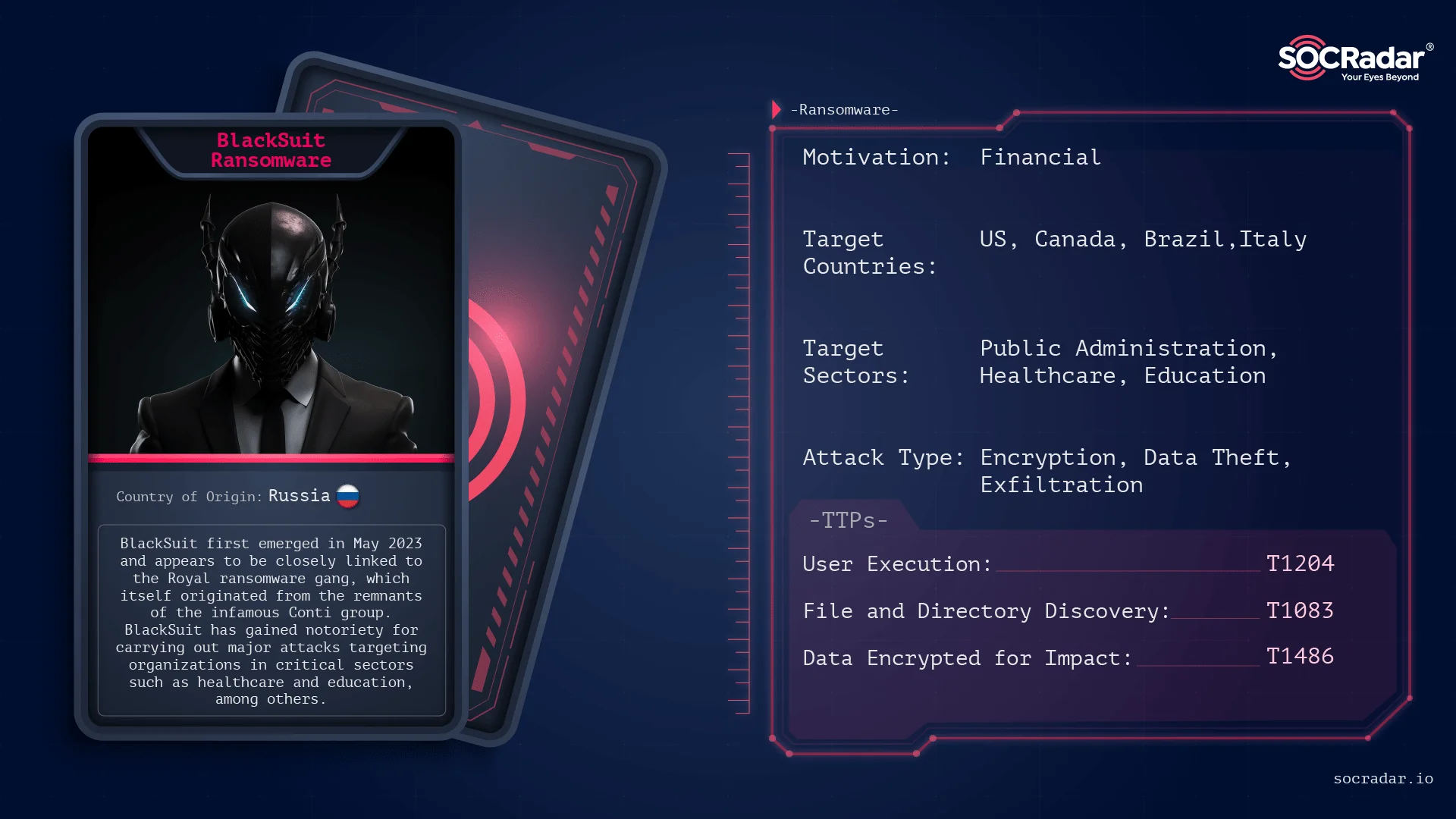
Threat Actor Card for BlackSuit Ransomware
In November of 2023, CISA and the FBI updated their joint Cybersecurity Advisory (CSA) on Royal Ransomware under the #StopRansomware initiative, highlighting its impact on critical sectors like manufacturing, communications, healthcare, and education. Since September 2022, Royal Ransomware has targeted over 350 victims globally, demanding ransoms exceeding $275 million.
For more information about the Royal Ransomware, check our relevant blog post.
Later, the advisory warned of a potential rebranding to BlackSuit Ransomware, noting similar coding characteristics. The update included detailed Tactics, Techniques, and Procedures (TTPs) and Indicators of Compromise (IoCs) identified by the FBI.
BlackSuit ransomware employs various techniques to infiltrate victims’ systems. One common method is through phishing emails, where attackers send deceptive messages designed to trick recipients into clicking on malicious links or downloading infected attachments. These emails often appear legitimate, making it easier for attackers to lure their targets.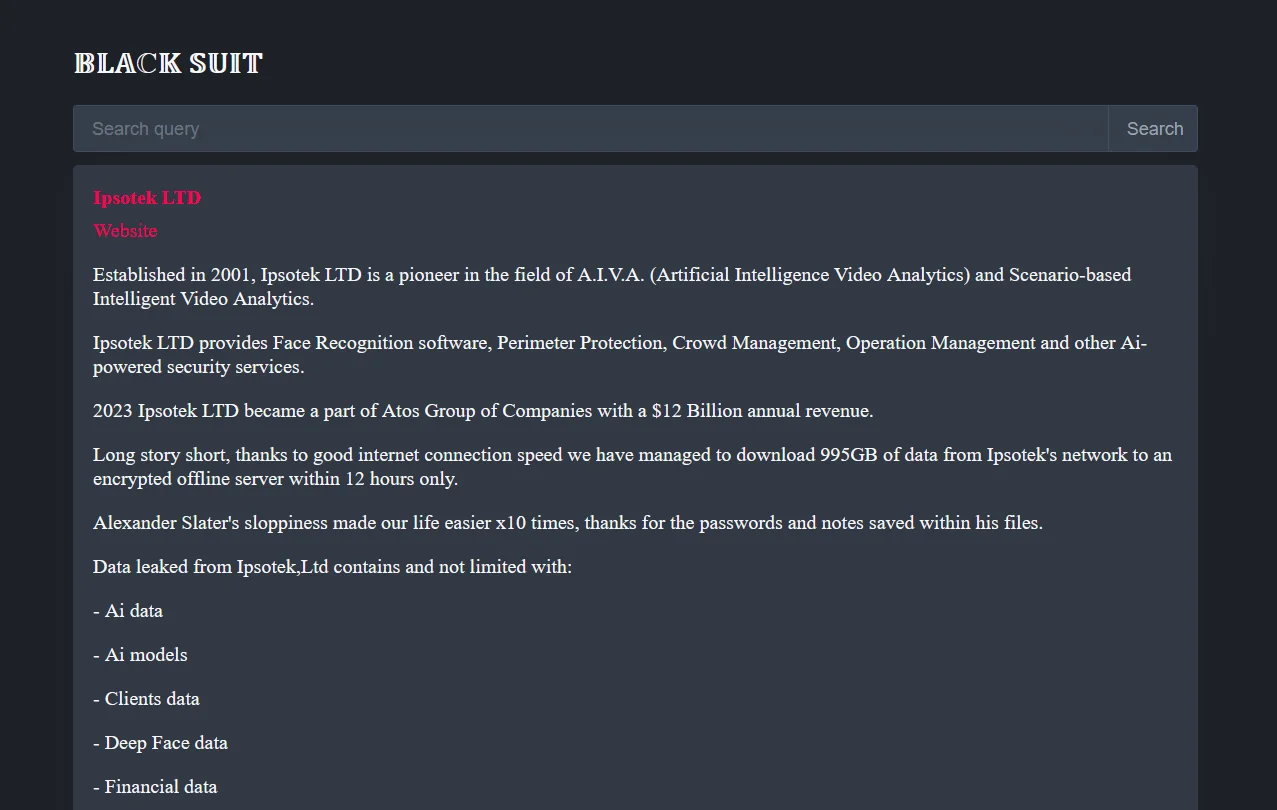
BlackSuit’s data leak site
Additionally, BlackSuit exploits known vulnerabilities in software and systems to gain unauthorized access. This method leverages flaws in outdated or unpatched software, allowing the ransomware to bypass security defenses. Exploiting these vulnerabilities is a critical component of BlackSuit’s infiltration strategy, as it targets weaknesses in widely-used applications and systems.
BlackSuit also uses legitimate tools for malicious purposes. Tools such as Chisel and Cloudflared are employed for network tunneling, enabling the attackers to bypass firewalls and other network security measures. These tools create secure communication channels that are difficult for traditional security systems to detect. Furthermore, BlackSuit utilizes AnyDesk and MobaXterm for establishing and maintaining remote access to compromised systems. These legitimate remote access tools are repurposed to provide the attackers with persistent access, allowing them to control and monitor infected systems over extended periods.
BlackSuit ransomware targets a diverse range of industries, often focusing on sectors where disruptions can have severe consequences.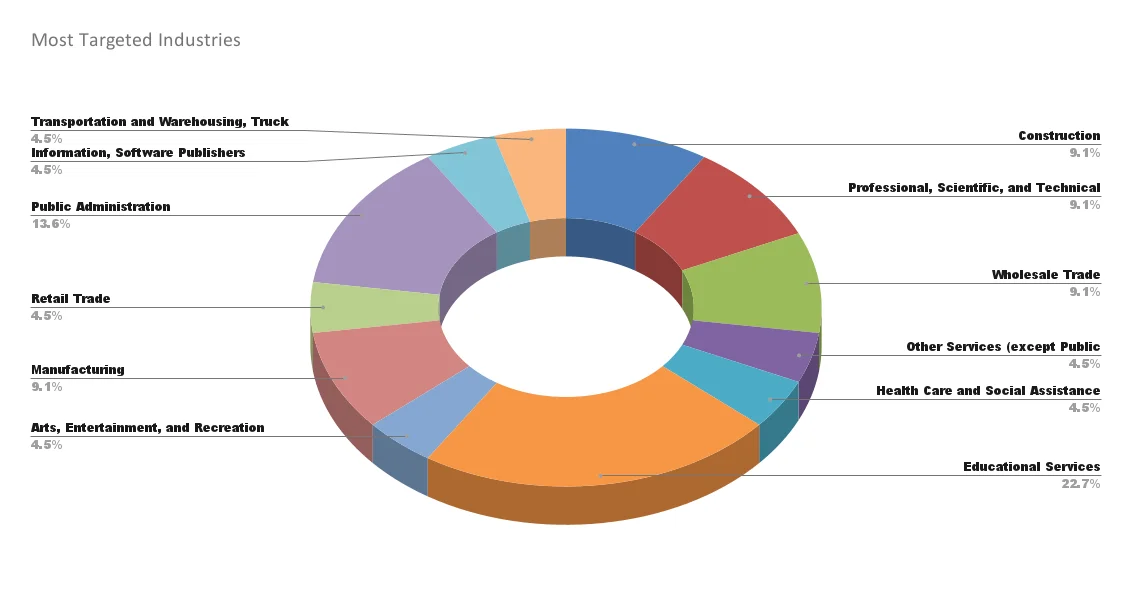
Most Targeted Industries
Notable targets include:
Healthcare: Hospitals and medical facilities are prime targets due to the critical nature of their operations and the sensitivity of their data. Disruptions in healthcare can have life-threatening consequences, making these institutions more likely to pay ransoms to restore operations quickly. Education, which ranks first, may have similar characteristics, although it is not as sensitive as healthcare.
Critical Infrastructure: This includes sectors like energy, water, and transportation, which are essential for public safety and economic stability. Attacks on these sectors can cause widespread disruptions, impacting large populations and creating significant pressure to resolve the incident swiftly.
Large Enterprises: Businesses with substantial financial resources are often targeted because they have the means to pay significant ransoms. These enterprises also store vast amounts of sensitive data, making them attractive targets for data exfiltration and subsequent extortion.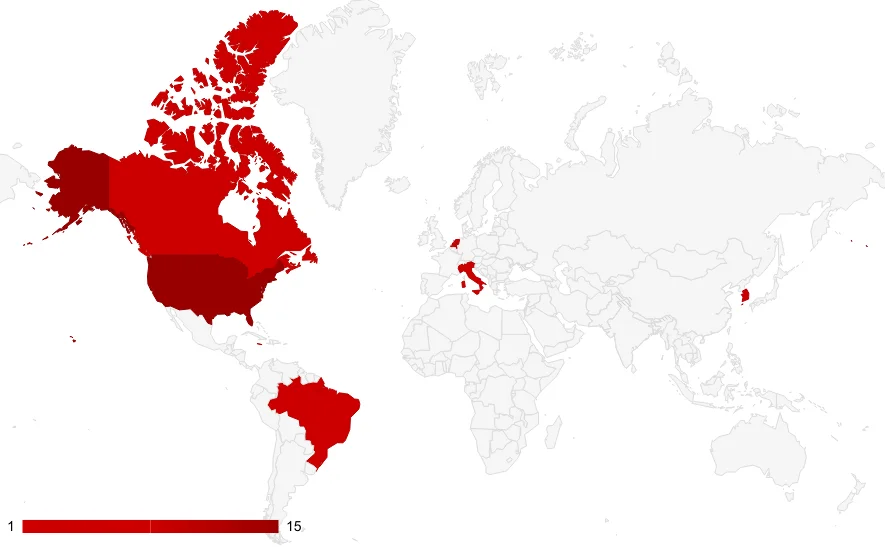
BlackSuit targets the US most
Ransom demands from BlackSuit are typically substantial, reflecting the high stakes of their chosen targets. The group employs a dual extortion tactic: they exfiltrate sensitive data before encrypting files, threatening to leak the data if the ransom is not paid. This approach adds pressure on the victims to comply with the ransom demands to prevent both operational disruptions and data breaches. The ransomware encrypts files using strong encryption algorithms, rendering the data inaccessible without the decryption key provided by the attackers upon payment.
In the analyses carried out in 2023, it was revealed that BlackSuit ransomware retained much of the original codebase from Royal ransomware, demonstrating over 90% code similarity. This indicated that BlackSuit inherits many of Royal’s technical attributes.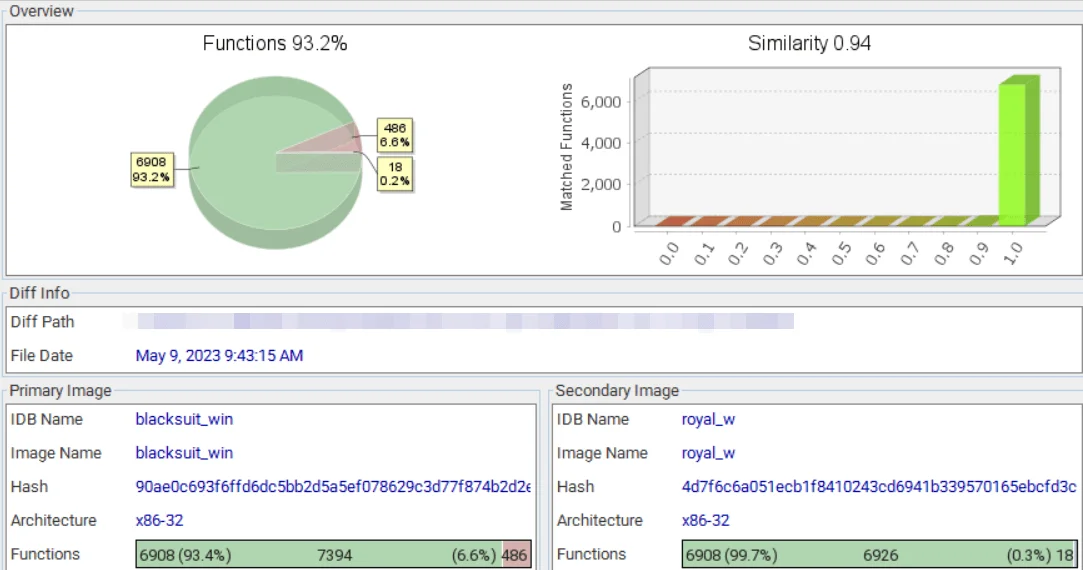
Similarity of the BlackSuit with Royal (Trend Micro)
Encryption Methods: BlackSuit utilizes robust encryption algorithms to lock files, making decryption extremely difficult without the attacker-provided key. BlackSuit ransomware payloads, designed for both Windows and Linux systems, employ OpenSSL’s AES implementation for data encryption. The encryption is designed to be efficient and fast, ensuring that a significant portion of the victim’s data is rendered inaccessible quickly, thereby increasing the pressure to pay the ransom.
Credential Theft: To escalate privileges and move laterally within the victim’s network, BlackSuit uses tools such as Mimikatz. This tool allows the attackers to harvest credentials from memory, enabling them to gain access to additional systems and accounts within the network. By obtaining high-level credentials, BlackSuit can bypass security measures and spread its reach more broadly within an organization.
Persistence Mechanisms: BlackSuit maintains its presence on compromised systems through the use of legitimate remote access tools like AnyDesk and MobaXterm. These tools allow the attackers to establish and maintain remote control over the infected systems. This persistence ensures that the attackers can monitor the systems, execute further commands, and potentially reinfect the network if initial remediation efforts are not thorough.
Network Tunneling: To bypass traditional security measures like firewalls, BlackSuit employs network tunneling tools such as Chisel and Cloudflared. These tools enable the creation of secure communication channels that are difficult to detect, allowing the attackers to move data in and out of the network undetected. This capability is particularly useful for exfiltrating sensitive data before encryption, which is a critical component of their dual extortion strategy.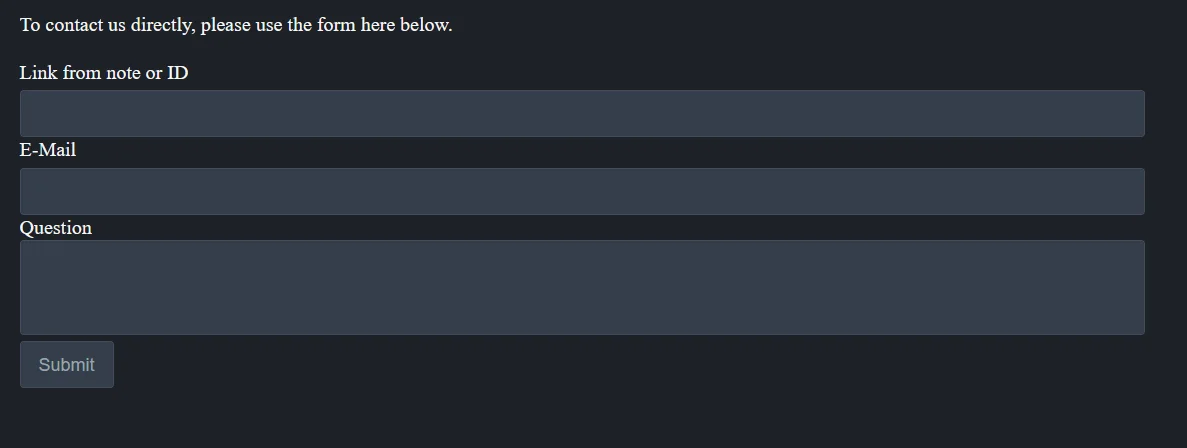
Contact us section of the data leak site
BlackSuit’s ability to exploit known vulnerabilities in software and systems, combined with its use of sophisticated tools and techniques, makes it a formidable threat. Its lineage from the Royal ransomware ensures that it inherits a proven and effective ransomware platform, enhanced with new tactics to evade detection and increase its impact. This comprehensive approach to ransomware deployment highlights the importance of robust cybersecurity measures and proactive threat hunting to detect and mitigate such advanced threats.
For more detailed information, please consult the advisory on CISA’s website here.
Implement secure-by-design and -default principles in software development to limit the impact of ransomware techniques, such as backdoor vulnerabilities into remote software systems. Incorporate practices suggested by CISA’s Secure by Design webpage and joint guide.
Password Security
Remote Access Security
System and Network Security
Access Controls and Privilege Management
Data Backup and Recovery
By implementing these mitigations, organizations can significantly reduce the risk of BlackSuit ransomware attacks and enhance their overall cybersecurity posture.
The FBI has revealed that the BlackSuit ransomware group has made over $500 million in ransom demands. This significant figure highlights the growing threat posed by BlackSuit, which has been targeting organizations across various sectors. The group continues to employ sophisticated tactics to infiltrate networks, exfiltrate sensitive data, and coerce victims into paying large sums. This new information underscores the importance of bolstering cybersecurity defenses to mitigate the risks associated with such a prolific ransomware threat.
Understanding their methods and implementing robust mitigation strategies are crucial steps for organizations to strengthen their defenses and reduce the risk of falling victim to ransomware attacks. Remaining vigilant and proactive in cybersecurity efforts is essential in combating ransomware groups like BlackSuit.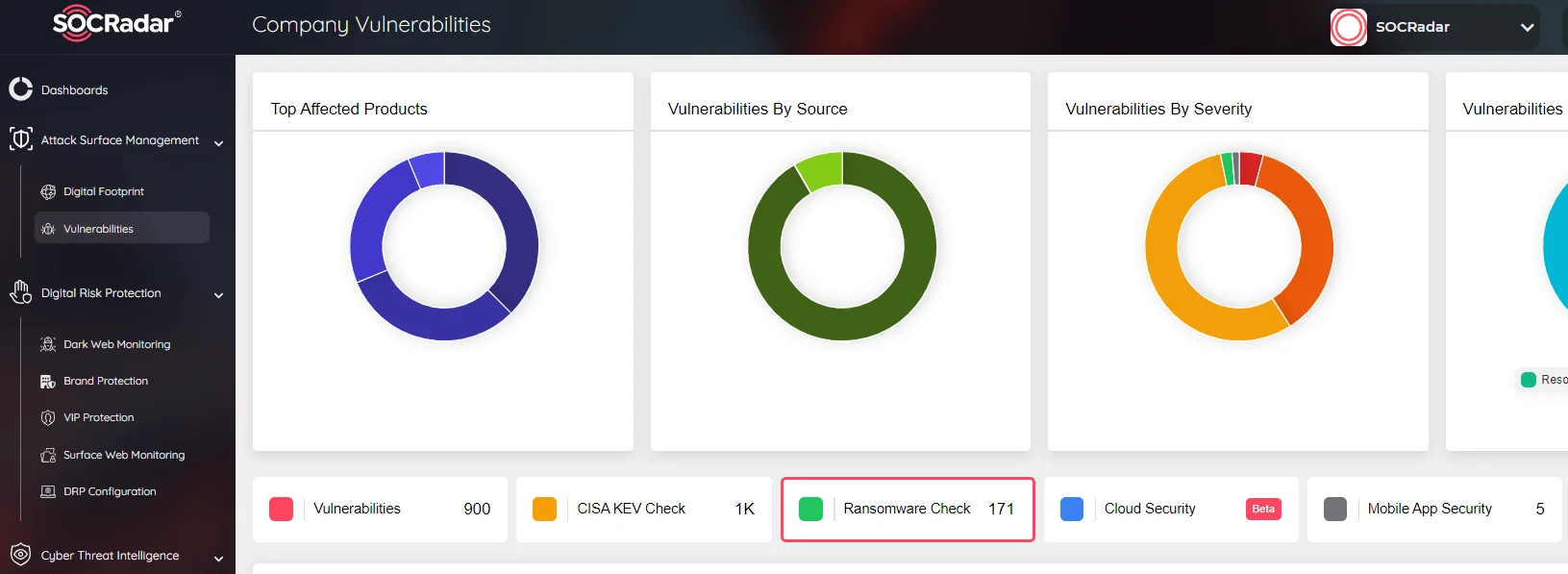
SOCRadar Attack Surface Management has Ransomware Check function
We can assist you in developing a proactive security posture. SOCRadar enhances your organization’s security stance against ransomware threats through proactive threat monitoring and intelligence solutions. By utilizing our platform, you can actively search for threat actors, comprehend their tactics and vulnerabilities, and implement preemptive measures to safeguard your assets.
SOCRadar’s Attack Surface Management module includes a Ransomware Check function. This feature offers ongoing monitoring of potential attack vectors, providing timely alerts for suspicious activities. This proactive approach facilitates swift responses to threats, strengthening your overall cybersecurity defenses. Integrating SOCRadar into your cybersecurity framework adds an additional layer of protection against ransomware and various cybersecurity threats.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
