Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
A new plant has grown in the desert of cyber threats, wielding its thorns to pierce through organizations and individuals alike. The Cactus Ransomware Group, a name recently whispered with curiosity across the cybersecurity realm, has emerged from the shadows, sowing seeds of chaos and disruption in its wake. With a prickly demeanor, this threat actor has meticulously crafted its ransomware to not only encrypt but also entangle itself within the fabric of digital security, evading detection with a finesse that demands a closer look.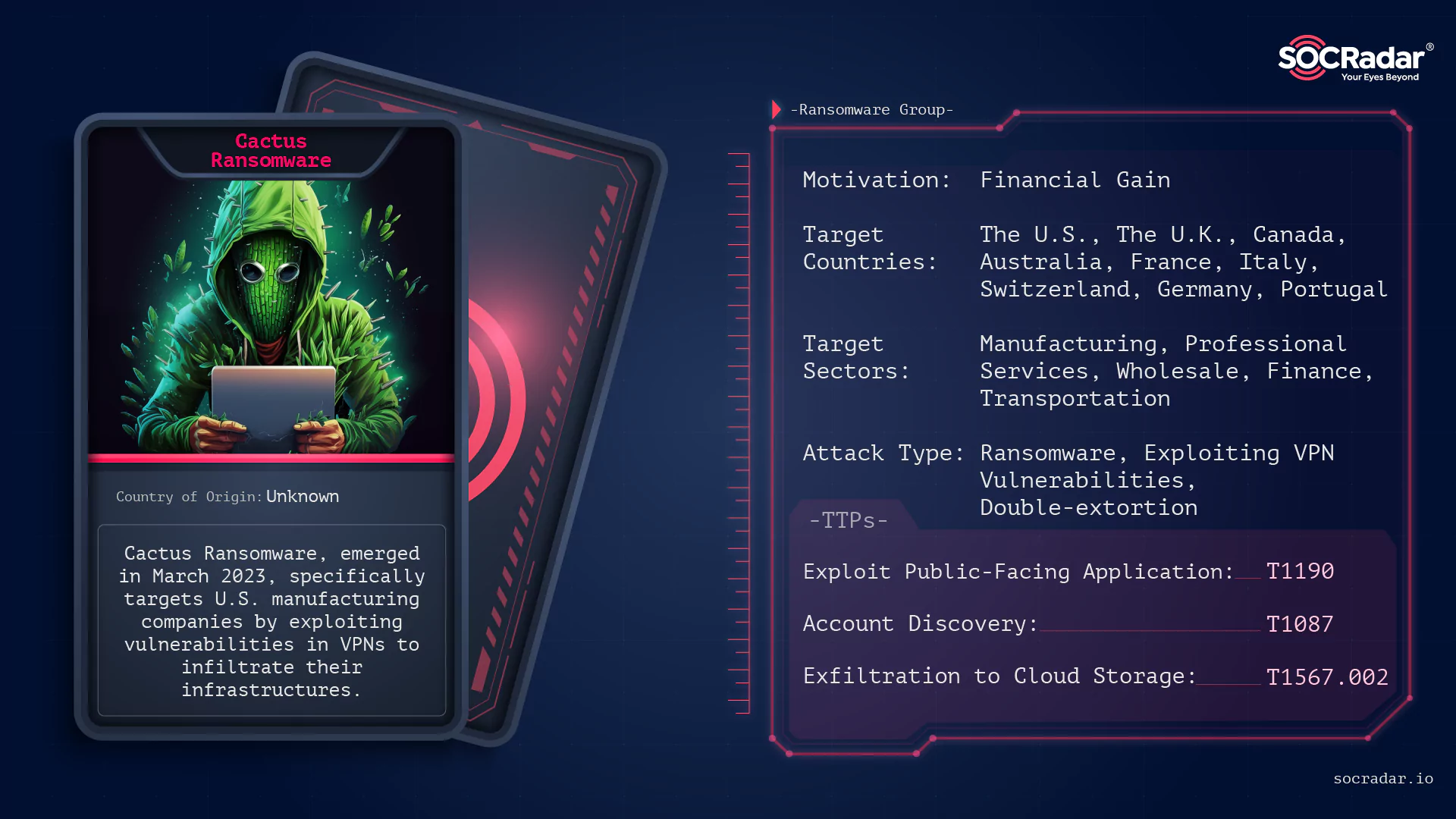
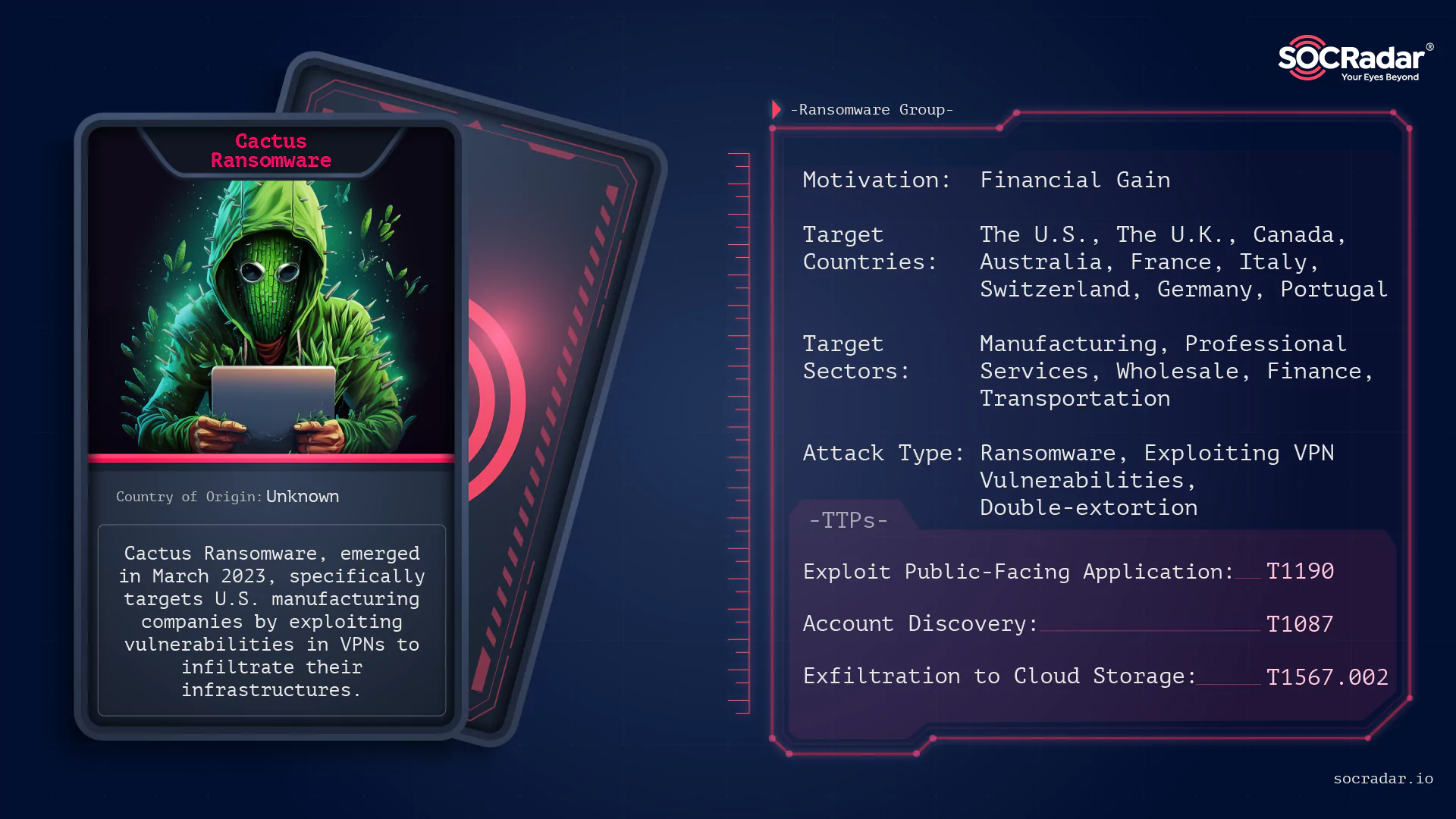
Threat actor card of Cactus Ransomware
Much like its namesake in the natural world, the Cactus Ransomware does not merely sit idly; it poses a latent threat, waiting for the opportune moment to strike. Employing a unique encryption technique that encrypts the ransomware binary itself, Cactus ensures its malicious endeavors go unnoticed by antivirus solutions, allowing it to propagate and establish a stronghold within the compromised system.
In this exploration, we delve into the intricate layers of Cactus Ransomware, unraveling its mechanisms, targets, and the prickly path it treads upon in the vast landscape of cyber espionage and malicious activities. Through our analysis, we aim to shed light on the dark corners where Cactus Ransomware blossoms, providing insights and recommendations to safely navigate through its thorny presence.
The Cactus Ransomware Group, first identified in March 2023, has rapidly spread its spines across the digital domain, exploiting vulnerabilities, particularly within VPNs, to gain unauthorized access and establish a foothold within compromised infrastructures. The group has demonstrated a sophisticated understanding of evasion techniques, employing a dynamic approach to encryption and utilizing many tools and techniques to ensure its malicious payload is delivered effectively and covertly.
Fig. 1. Illustration of Cactus Ransomware, generated using DALL-E 3
Cactus does not just stop at encryption. The threat actor ensures its presence is deeply rooted within the compromised system, employing a complex infection chain and utilizing multiple layers of obfuscation to conceal its activities. From using UPX packing and leveraging encryption algorithms like OpenSSL, AES OCB, and ChaCha20_Poly1305 to organizing restart executions and enumerating network shares, Cactus demonstrates a multifaceted approach to its attacks, ensuring that its activities are not only successful but also remain surrounded in secretiveness.
The group has demonstrated an ability to hit stealthily, ensuring its malicious attempts remain concealed beneath a cover of sophistication and complexity. Here are the phases cactus ransomware follows when it is operating:
The Initial Access
Cactus Ransomware exploits vulnerabilities in VPN devices, paving a secret path into the target’s infrastructure. The initial access is indicated by the exploitation of VPN vulnerabilities, followed by the creation of an SSH backdoor, which not only facilitates unauthorized access but also ensures a persistent presence within the compromised network.
The Infection Chain
The infection chain of Cactus is a complicated journey through multiple layers of obfuscation and evasion. Employing a batch script to execute the ransomware sample using 7-Zip, Cactus encrypts itself, evading detection mechanisms and embedding itself within the system. The attack chain is multifaceted, involving a series of steps that include exploiting VPN vulnerabilities, utilizing remote access tools like Splashtop or AnyDesk, managing operations with SuperOps RMM software, simulating attacks with Cobalt Strike, establishing encrypted communication channels with Chisel, and exfiltrating credentials.
Encryption Phase
Once embedded, Cactus Ransomware follows a path of encryption. The ransomware employs AES-256-GCM and RSA-4096 encryption algorithms, ensuring the victim’s files are securely encrypted, amplifying the attack’s impact. The ransom note, named “cAcTuS.readme.txt“, is then released, planting seeds of panic and urgency within the victim.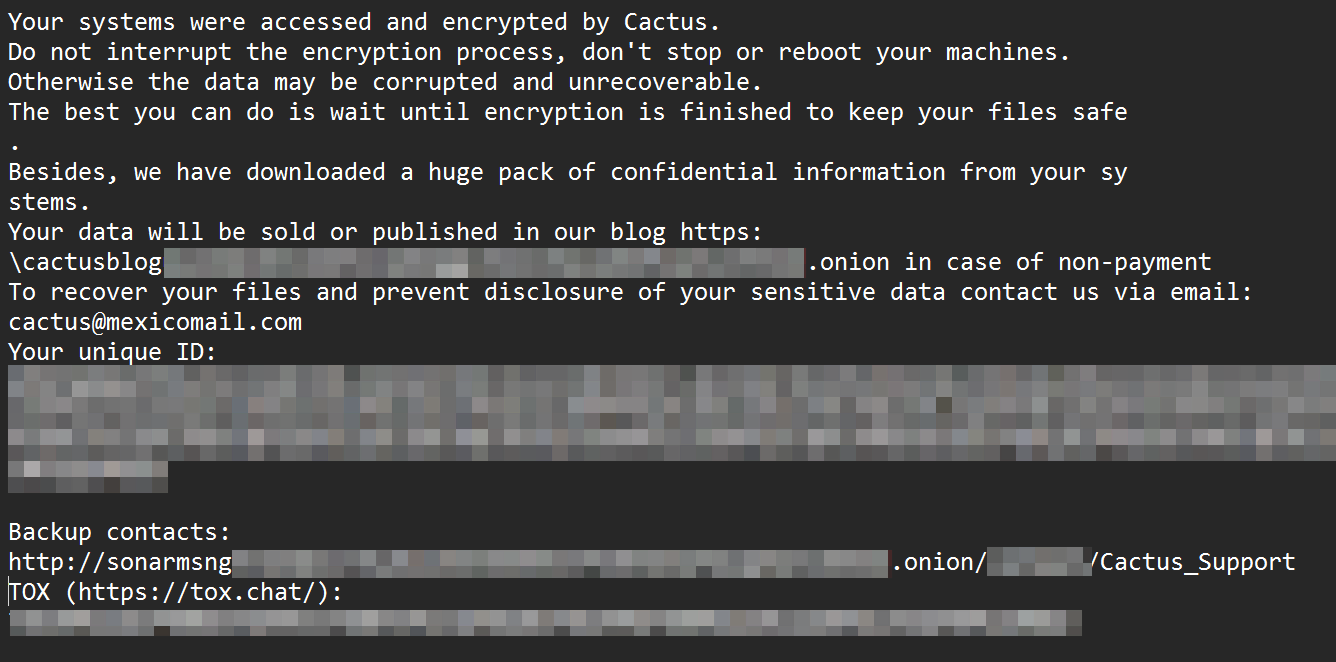
Fig. 2. Ransom note of Cactus Ransomware
Data Exfiltration and Leaks
Cactus does not merely stop at encryption. The threat actor ensures that its venomous spines reach far and wide, threatening to publish the victim’s data on its data leak portal if the ransom is not paid, which is called the double extortion method. The data leak portal, a dark web domain, becomes a threat to the victims, ensuring that the attack’s implications extend beyond encryption, permeating into data integrity and reputation damage.
Persistence
Cactus Ransomware ensures its persistent presence within the compromised system by creating a scheduled task named “Updates Check Task” that runs every 5 minutes, thereby running the ransomware as SYSTEM and ensuring that its malicious activities continue without a problem.
Structure of Cactus Ransomware
Now, if we move on to the structure of the Cactus:
The sample we can access from the internet is the GNU linker. Looking at the details, we can observe that the language it was developed in is C/C++.
Our sample’s hash is:
SHA256: 78c16de9fc07f1d0375a093903f86583a4e32037a7da8aa2f90ecb15c4862c17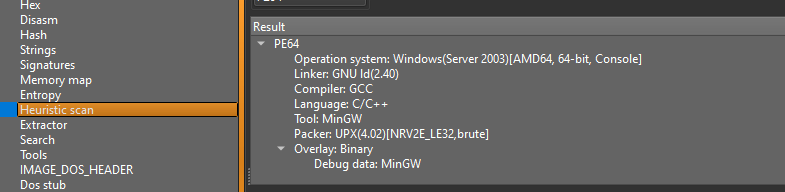
Fig. 3. Detect It Easy output showing that Cactus ransomware is developed in C/C++
When we access Cactus Ransomware’s TOR site, we are greeted by the main page listing victim shares.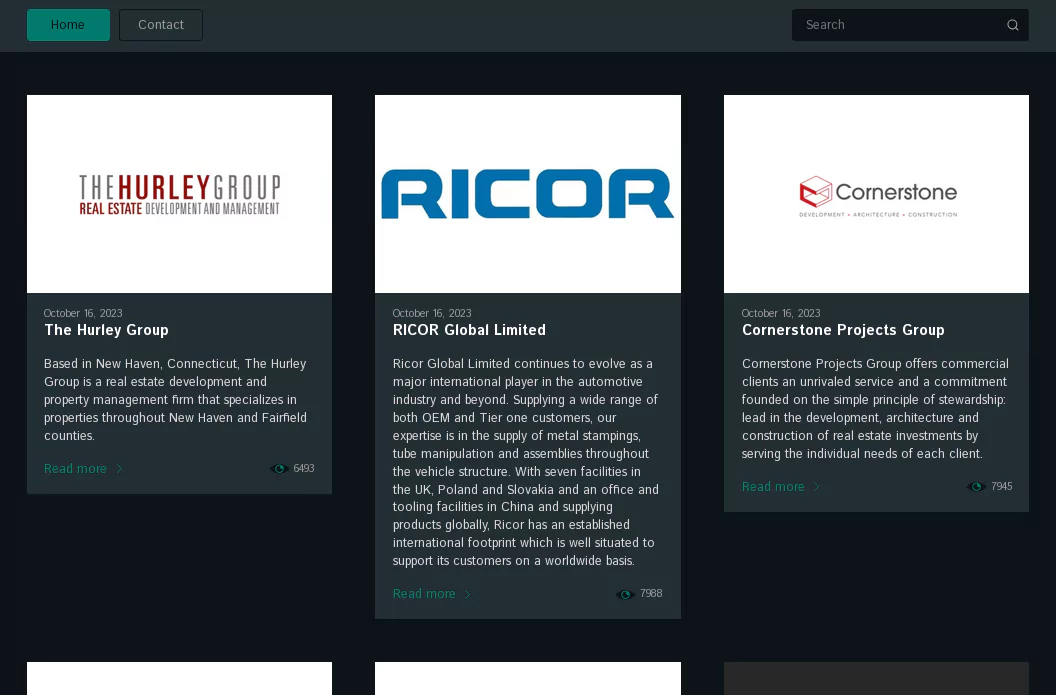
Fig. 4. Main page of Cactus Ransomware TOR site
When we access Cactus Ransomware’s TOR site, we are greeted by the main page listing victim shares. At the top, a search box and buttons take you to the “Home” and “Contact” sections.
Clicking on any victim on the main page opens the victim detail page, which includes information about Cactus’ victim, a download link to the data leaked by Cactus, and evidentiary images: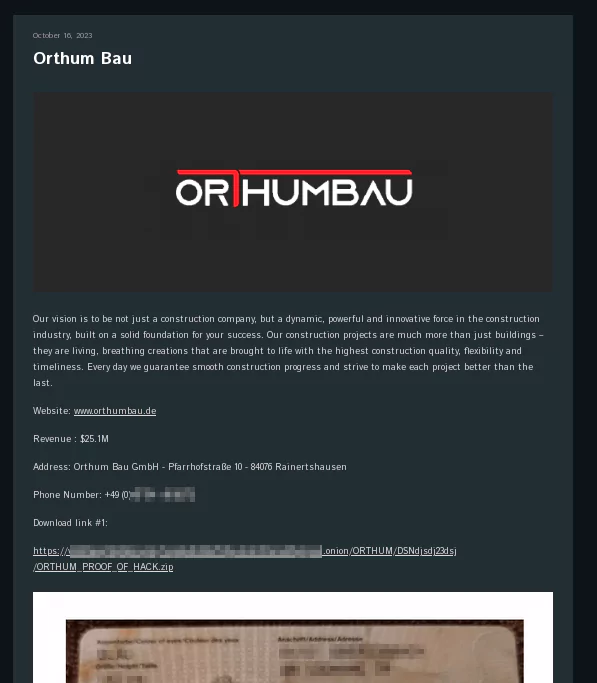
Fig. 5. Victim details page of one of the Cactus Ransomware’s victims
As we click on the Contact page above, we are greeted with a link to the sonar message platform to access “Cactus Support”.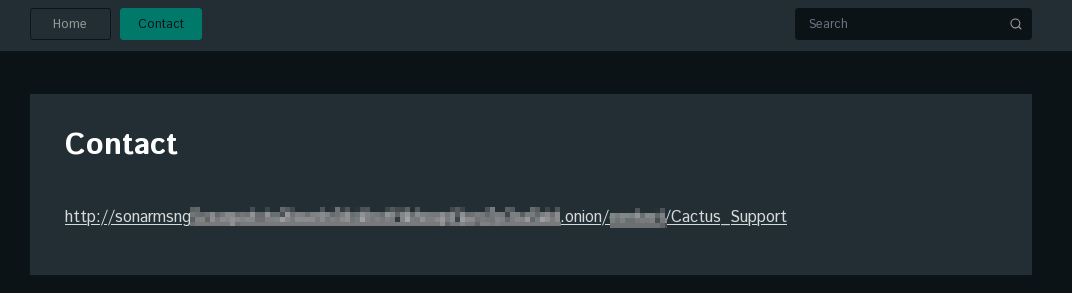
Fig. 6. Contact page of Cactus Ransomware TOR site
When we follow the Sonar message link, there are message boxes for us to reach Cactus: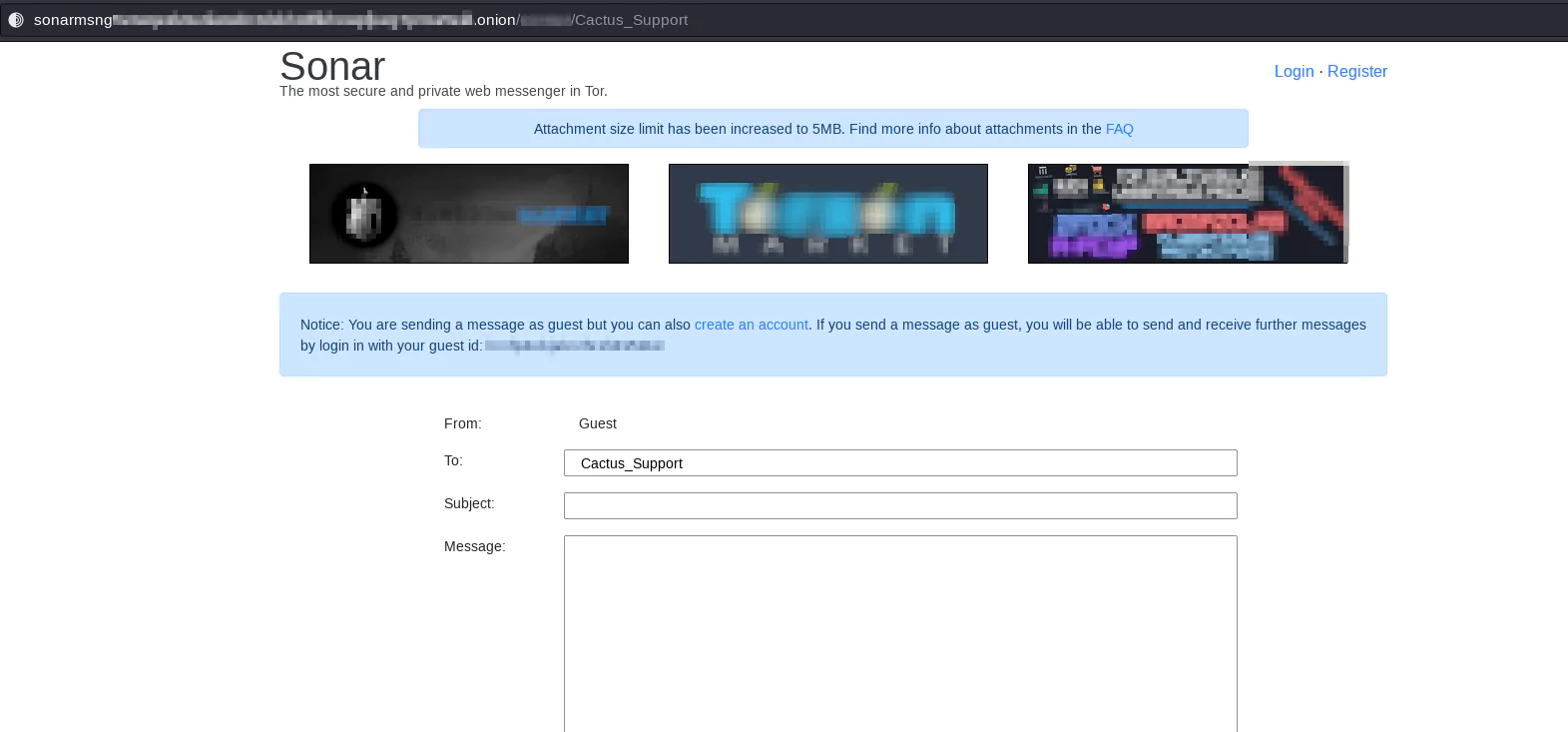
Fig. 7. Sonar Message TOR page set for Cactus Support
Navigating through the dry landscapes sculpted by the Cactus Ransomware Group, we encounter many targets. The targets paint a picture of a threat actor that is not bound by geographical or sectoral limitations but rather one that spreads its spines far and wide.
The sectors targeted by the Cactus Ransomware Group are as diverse as they are numerous. From financial entities to law firms, Cactus has ensured that its thorns prick through various sectors of our digital world. But mostly, the group targeted organizations that operate in Manufacturing and Professional Services.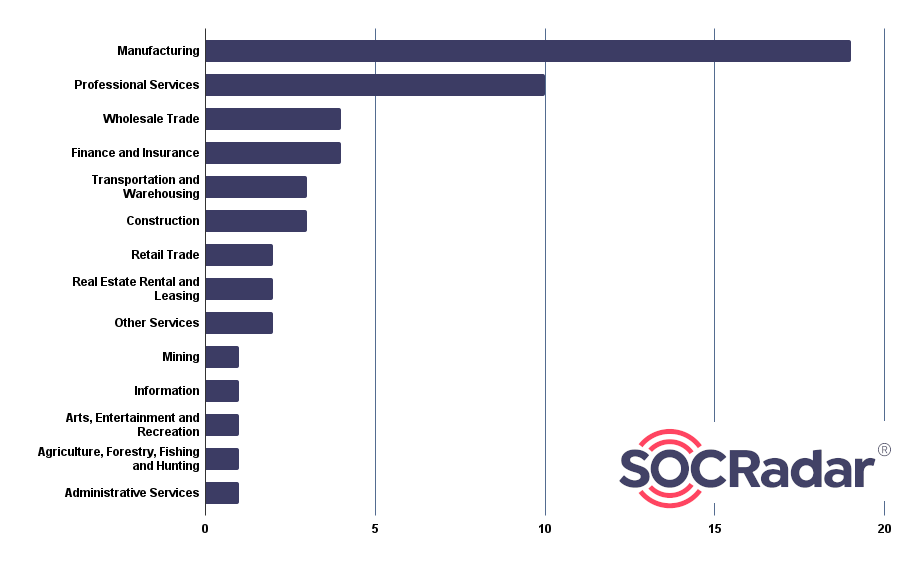
Fig. 8. Distribution of Industries Affected by Cactus Ransomware
With its global attribute, Cactus Ransomware does not confine its malicious endeavors to a specific geographical locale. Its spines have pierced through various countries.
Fig. 9. Countries Affected by Cactus Ransomware (Source: SOCRadar)
Looking at the distribution of the victim countries, the United States is targeted mostly (51.9%) by the Cactus Ransomware.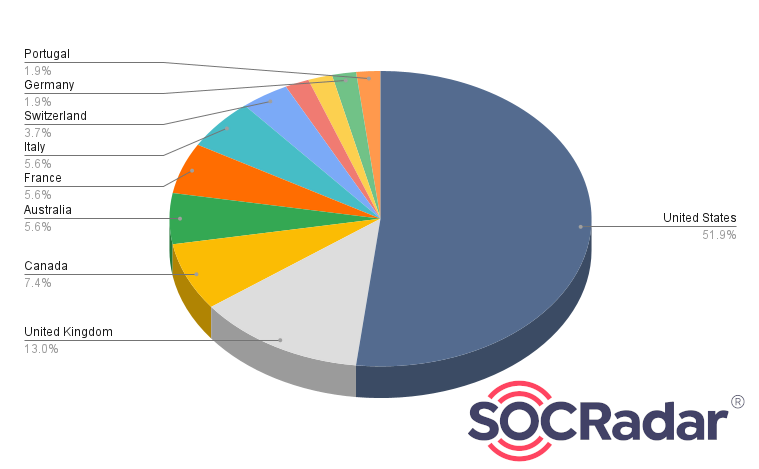
Fig. 10. Distribution of countries affected by Cactus Ransomware (Source: SOCRadar)
The Hurley Group: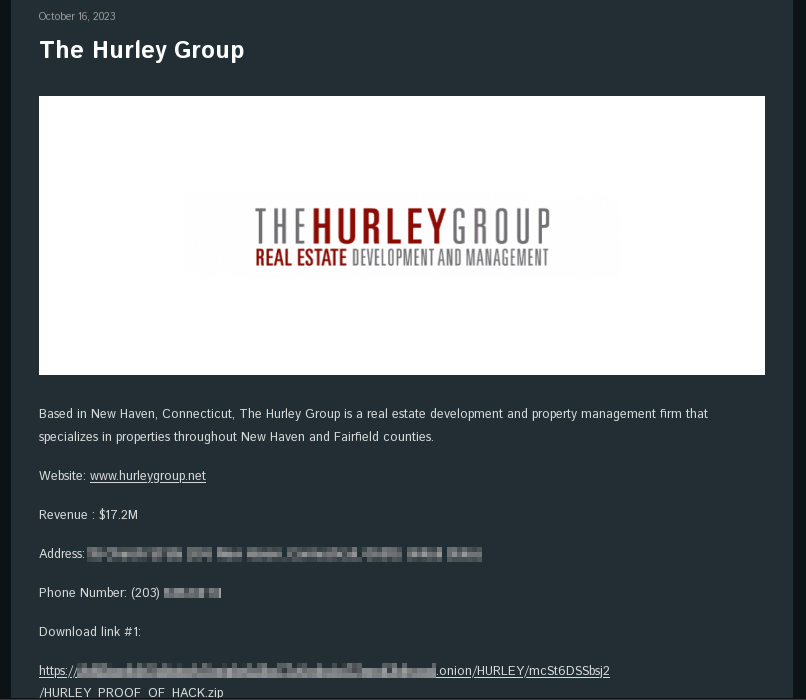
Fig. 11. The Hurley Group’s Victim post of Cactus Ransomware
RICOR Global Limited: 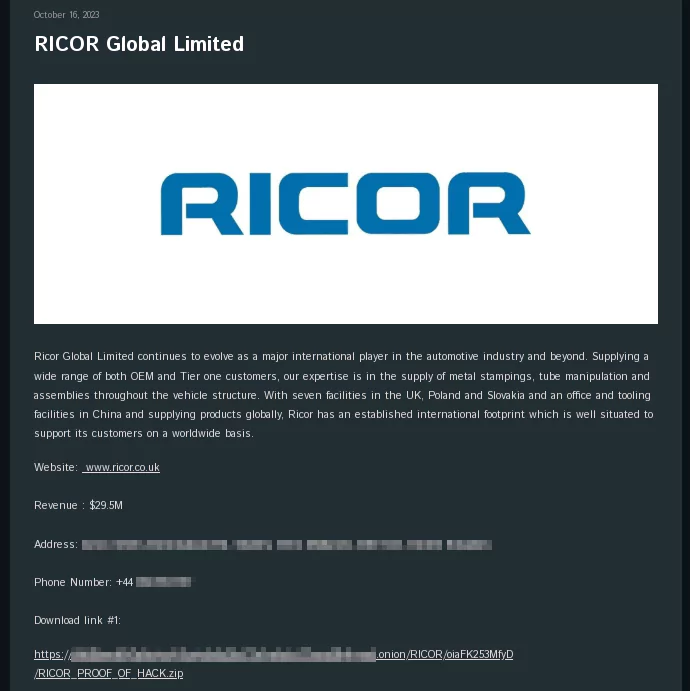
Fig. 12. RICOR’s victim post of Cactus Ransomware
The Cactus Ransomware Group poses a significant threat in the cyber landscape. They have established themselves as a major cyber adversary using advanced encryption techniques, evasion strategies, and diverse attack methods. They have successfully attacked various sectors globally, demonstrating their ability to penetrate and remain within systems, causing chaos and disruption. Victims face encryption challenges and the potential public exposure of their data on Cactus’s leak portal, jeopardizing data integrity, confidentiality, and organizational reputation. It is crucial to understand Cactus Ransomware’s tactics to combat this threat and equip ourselves with the necessary knowledge and tools to protect against it. The next section will provide security recommendations to defend against Cactus Ransomware’s malicious activities.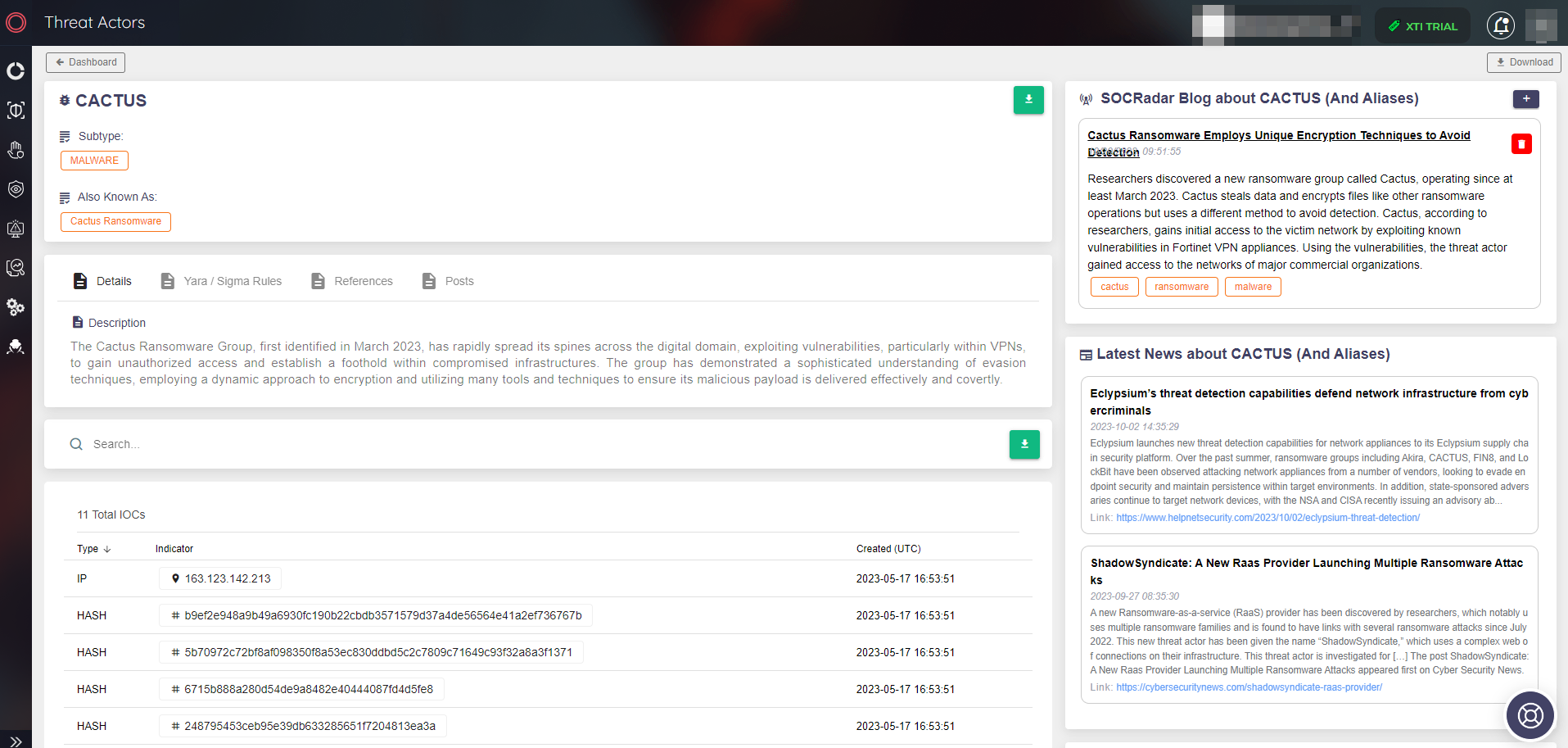
Fig. 13. Threat Actor/Malware page of Cactus Ransomware (Source: SOCRadar)
Navigating through the dangerous desert sculpted by the Cactus Ransomware Group necessitates not only an understanding of its prickly paths but also the armament of robust defenses to safeguard against its venomous spines. As we tread cautiously through the thorny terrains, let’s explore various security recommendations to shield against the multifaceted threats posed by Cactus Ransomware.
Patching and Updating: A Shield Against Vulnerabilities
Prioritize VPN Security: Ensure that all VPN softwares/devices are patched and updated to shield against vulnerabilities exploited by Cactus.
Regular Updates: Consistently update all software, systems, and applications to fortify defenses against potential breaches.
Antivirus Solutions: Employ robust antivirus and EDR/EPP solutions capable of detecting and mitigating threats posed by self-encrypting ransomware binaries.
Behavioral Analysis: Utilize tools, including EDR (Endpoint Detection and Response) and EPP (Endpoint Protection Platform), that perform behavioral analysis to detect anomalous activities indicative of a ransomware attack.
Regular Backups: Ensure that data is backed up regularly and that backup systems are isolated from the network to safeguard against encryption.
Data Encryption: Employ data encryption to protect sensitive information from potential leaks and unauthorized access.
Phishing Awareness: Conduct training sessions to enhance user awareness regarding phishing emails, which are often utilized by Cactus for initial access.
Safe Practices: Educate users on safe online practices to mitigate the risk of inadvertently facilitating a breach.
Network Segmentation: Employ network segmentation to contain the spread of ransomware in the event of a breach.
Secure Configurations: Ensure that systems and networks are securely configured to shield against potential infiltrations.
Develop and Test: Formulate an incident response plan and ensure that it is tested and updated regularly to effectively navigate through a crisis.
Communication Channels: Establish secure communication channels to coordinate response efforts in the event of a ransomware attack.
Data Breach Protocols: Ensure that data breach protocols are in place and comply with legal and regulatory requirements pertaining to data exposure and leaks.
Notification Procedures: Establish procedures to notify affected parties and relevant authorities in the event of a data breach.
Utilize Threat Intelligence: Leverage cyber threat intelligence to gain insights into the tactics, techniques, and procedures (TTPs) employed by Cactus Ransomware.
SOCRadar’s Insights: Utilize SOCRadar to stay abreast of the latest developments and threats posed by threat actors like the Cactus Ransomware Group, ensuring that defenses are continually updated and fortified against emerging threats.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
