Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
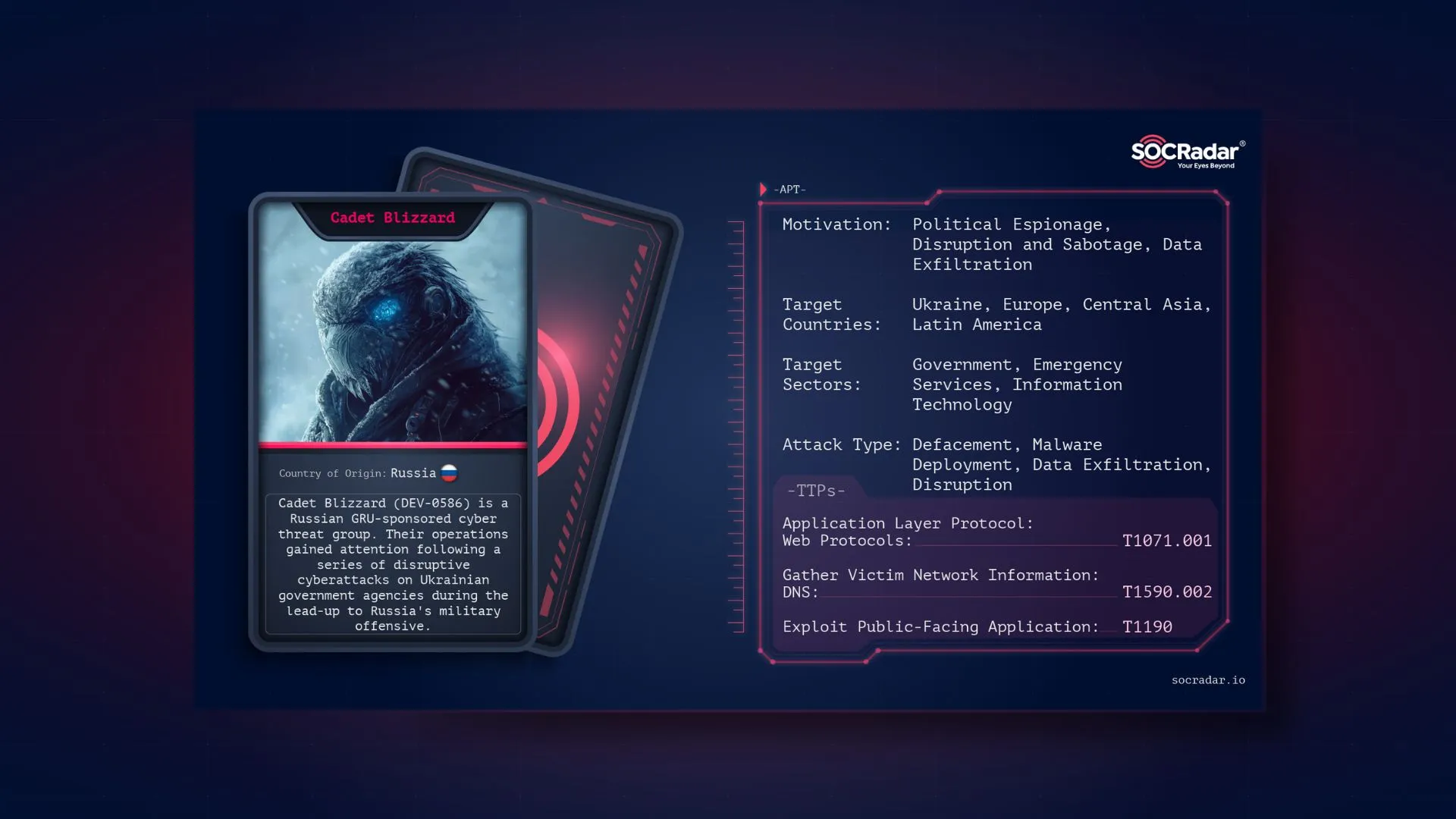
Cadet Blizzard (DEV-0586) is a Russian GRU-affiliated cyber threat group first tracked by Microsoft in early 2022, following a series of disruptive cyberattacks on Ukrainian government agencies amidst rising military tensions. These attacks, including website defacements and the deployment of the WhisperGate malware, foreshadowed further activity from the group, aligning with Russia’s military invasion of Ukraine.
While primarily targeting government and IT sectors in Ukraine, Cadet Blizzard has expanded its operations to include organizations in Europe and Latin America. The group has maintained a persistent presence since at least 2020, exfiltrating data before executing disruptive actions, with activity peaking between January and June 2022. After a period of reduced activity, Cadet Blizzard resumed operations in January 2023, launching further attacks against Ukrainian and European entities, including the re-emergence of their “Free Civilian” Telegram channel. This group remains active, with a focus on targeting NATO member states involved in aiding Ukraine, operating primarily during European off-business hours.
Cadet Blizzard, part of Unit 29155, is a highly secretive and sophisticated cyber warfare group with strong ties to the Russian military intelligence agency GRU. Formed as part of the GRU’s broader efforts to disrupt global systems, the group is primarily known for its cyber-espionage and sabotage campaigns, often targeting critical infrastructure across the world. Although its existence was initially veiled in secrecy, investigations have unveiled the group’s involvement in various state-sponsored cyberattacks and physical sabotage operations.
Threat Actor card for Cadet Blizzard
The name “Cadet Blizzard” is one of several associated cyber warfare groups of Unit 29155. Unit 29155 is believed to have been established around 2010, though it gained international attention in recent years due to its direct involvement in high-profile cyberattacks, including the 2016 U.S. presidential election interference and the cyberattacks during Russia’s 2022 invasion of Ukraine. The group’s activities span a wide range of malicious operations—from data exfiltration and credential theft to sophisticated manipulation of industrial and governmental systems.
For a more comprehensive understanding of Unit 29155, check CISA’s advisory.
According to Microsoft, Cadet Blizzard primarily targets government organizations and entities involved in critical infrastructure, with a special focus on military and defense sectors. The group’s operations are often politically motivated, aligning with Russia’s strategic goals. In addition to government agencies, Cadet Blizzard also targets sectors that support military operations, such as technology providers, supply chain partners, and other institutions critical to national security.
The group has been particularly active in Ukraine, where it has targeted Ukrainian government websites and critical services, using techniques such as website defacements and deploying custom malware like WhisperGate. This activity intensified alongside Russia’s military actions, indicating that the cyber operations are coordinated with broader geopolitical objectives.
Their targets are not limited to Ukraine alone; they have also extended their operations to Europe, particularly NATO member states involved in supporting Ukraine’s defense. The goal appears to be to disrupt, steal sensitive data, and create destabilizing effects on these nations’ infrastructure and security frameworks. The group’s activities are ongoing, with observed bursts of operations timed to cause maximum disruption, often during off-business hours of the targeted entities.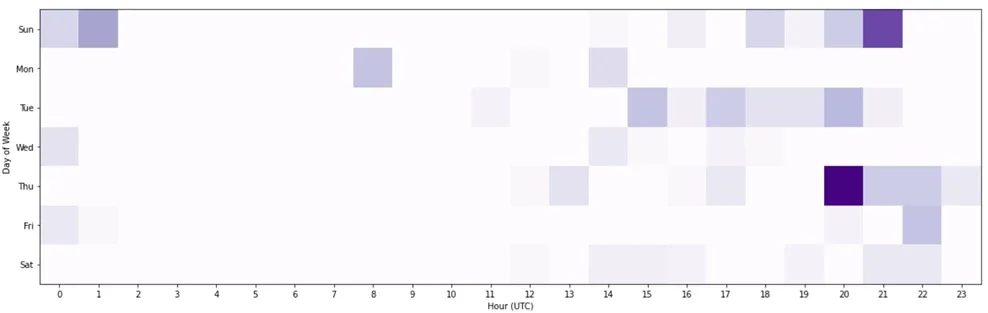
Cadet Blizzard’s operating hours according to Microsoft
Cadet Blizzard follows a complex and calculated cyber kill chain to conduct their operations. This multi-step process enables them to infiltrate, manipulate, and disrupt targeted systems effectively.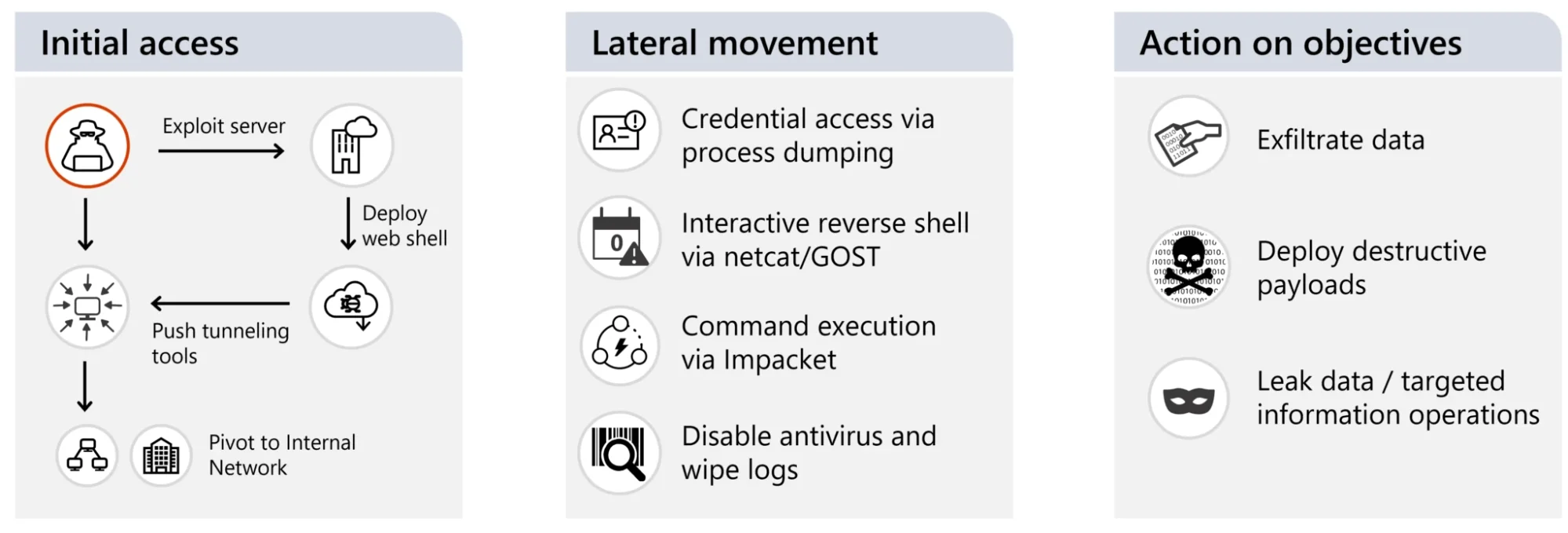
Cadet Blizzard’s normal operational lifecycle (Microsoft)
Cadet Blizzard frequently gains initial access by exploiting vulnerabilities in web servers situated on the network perimeter or in DMZs. Known vulnerabilities include CVE-2021-26084 (Confluence servers) and CVE-2022-41040 and ProxyShell (Exchange servers). The group is also known to exploit weaknesses in open-source platforms, such as content management systems, to gain entry.
After gaining access, Cadet Blizzard ensures long-term access to the network by deploying commodity web shells like P0wnyshell, reGeorg, PAS, and custom versions from publicly available exploit kits. These shells act as backdoors, allowing for tunneling or commanding, ensuring that the group can maintain persistent control over the compromised systems.
To escalate their access and control over the network, Cadet Blizzard utilizes living-off-the-land techniques, such as dumping credentials from the LSASS process with tools like procdump (which is often renamed, for example, as dump64.exe). Additionally, they extract registry hives to obtain critical credential information, further enabling their ability to move across the network undetected.
Once in possession of valid network credentials, Cadet Blizzard moves laterally through the network using tools like Impacket and PowerShell commands. For example, they use PowerShell’s get-volume command to enumerate device volumes and the DownloadFile command to retrieve malicious files from their infrastructure. Cadet Blizzard may also create scheduled tasks or reverse shells to facilitate command execution across the network.
To maintain control over compromised systems, Cadet Blizzard utilizes tunneling tools like NetCat and GOST (which are sometimes renamed to blend in with the system’s native tools). These utilities enable reverse shell connections, allowing the group to remotely execute commands. While their use of Meterpreter is limited, it has been deployed in some operations.
To obscure their activities and evade detection, Cadet Blizzard leverages tools like IVPN, SurfShark, and Tor, which anonymize their communications and make it more difficult to trace their actions back to them.
To cover their tracks and hinder forensic investigations, Cadet Blizzard extracts system logs using the Win32_NTEventlogFile command in PowerShell, then deletes them to erase traces of their activity. They also disable Microsoft Defender Antivirus by using tools like the NirSoft AdvancedRun utility and registry modifications to stop the WinDefend service.
Cadet Blizzard’s operations are designed not only for intelligence gathering but also for disruption. The group exfiltrates large volumes of data, including sensitive credentials and communication logs, and often leaks this data on platforms like Tor or Telegram. Their destructive actions, such as using WhisperGate malware to erase data and disrupt systems, demonstrate their broader objectives of creating chaos and signaling geopolitical messages. Through these tactics, Cadet Blizzard blends espionage and high-impact disruptions, ensuring that their operations leave a significant mark on targeted entities.
This approach reflects the group’s strategy of using existing tools and services to maintain access and execute high-profile, disruptive operations while minimizing their digital footprint.
Defending against Cadet Blizzard and similar APT groups requires a multi-layered, proactive defense strategy. Given the group’s sophisticated tactics and focus on both data exfiltration and disruption, organizations must ensure robust security measures across several key areas:
SOCRadar offers several key features to help organizations defend against APT groups like Cadet Blizzard by providing real-time visibility, monitoring, and proactive threat intelligence: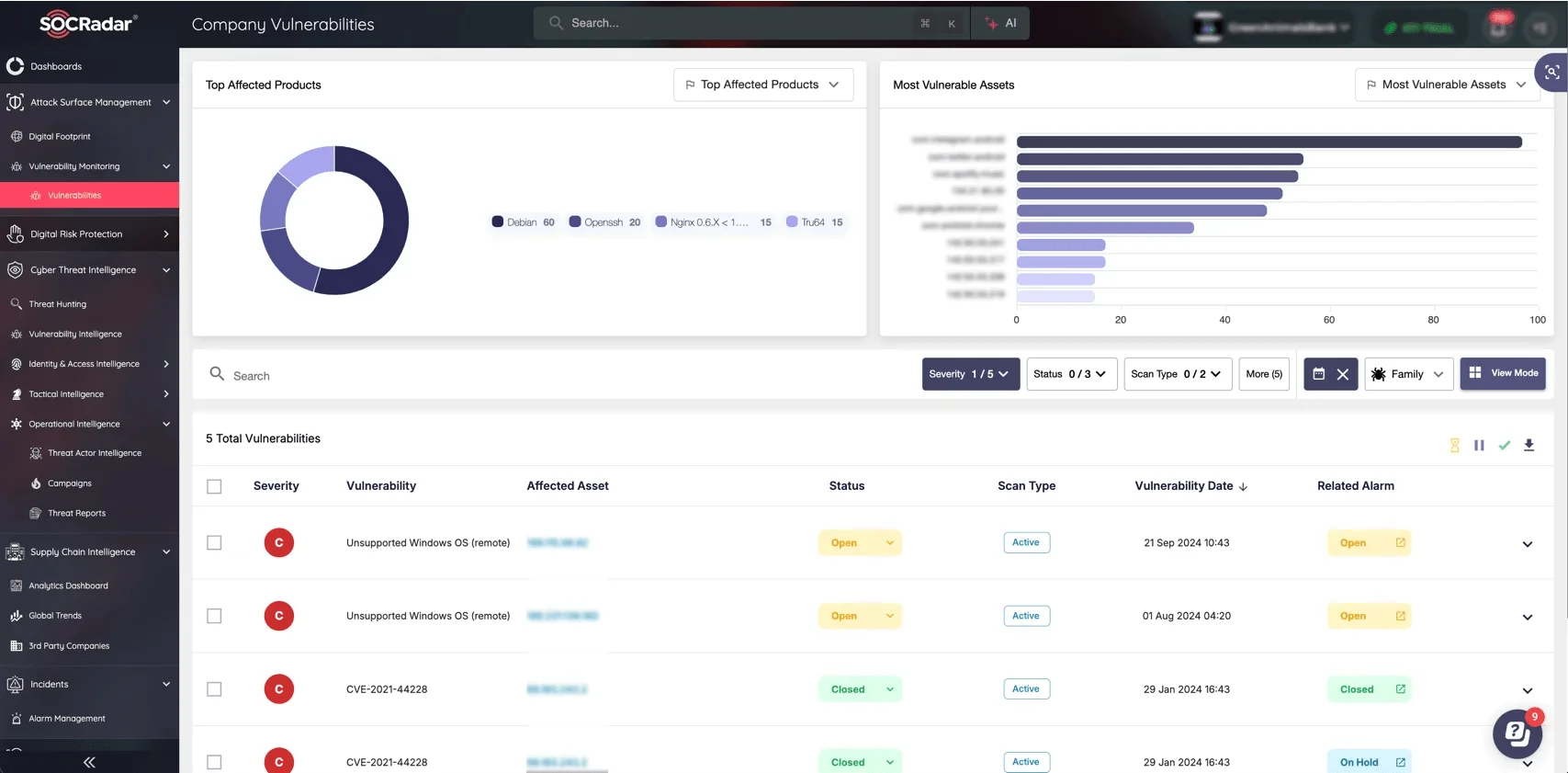
SOCRadar Attack Surface Management
By combining the insights provided by SOCRadar with the defense strategies outlined above, organizations can build a robust defense against Cadet Blizzard and similar APT groups. SOCRadar’s real-time threat intelligence and comprehensive monitoring tools ensure that security teams are always informed of the latest threats and can act swiftly to mitigate potential risks. Together, these measures help organizations stay one step ahead of adversaries and protect critical assets.
For further readings, please refer to the CISA’s advisory and Microsoft’s blog.
According to CISA’s advisory:
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
