Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
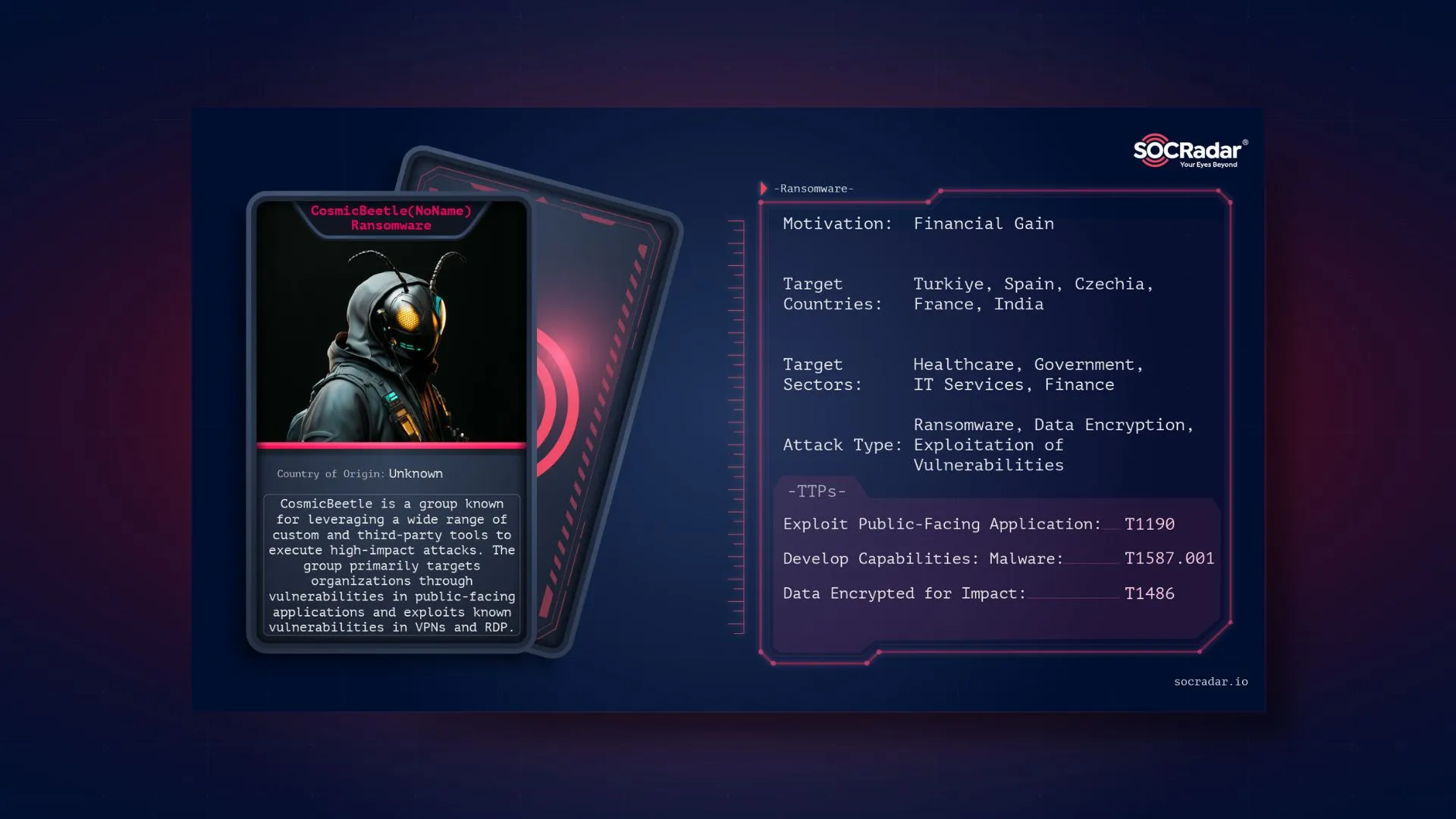
CosmicBeetle, also known as NoName, is a ransomware group that has targeted small to medium enterprises globally with its customized ransomware tools. Notably active since 2020 and gaining traction in 2023, the group has worked to establish a foothold in the cybercrime landscape by deploying unique encryption software like ScRansom. Known for attempting to mimic the infamous LockBit ransomware group, CosmicBeetle has adopted similar strategies, including a DLS (Data Leak Site) designed to pressure victims into paying ransoms.
Illustration of CosmicBeetle (Bing AI)
The ransomware group CosmicBeetle, tracked by cybersecurity firms as NoName, first appeared in 2020, but its activities have escalated significantly in 2023. While the group should not be mistaken for a pro-Russian hacktivist group with the same moniker as NoName057(16), it has established itself as a prominent cyber threat with a distinct operational profile. CosmicBeetle primarily targets small to medium-sized enterprises worldwide, often breaching networks using brute-force attacks and exploiting known vulnerabilities, such as EternalBlue (CVE-2017-0144) and Zerologon (CVE-2020-1472).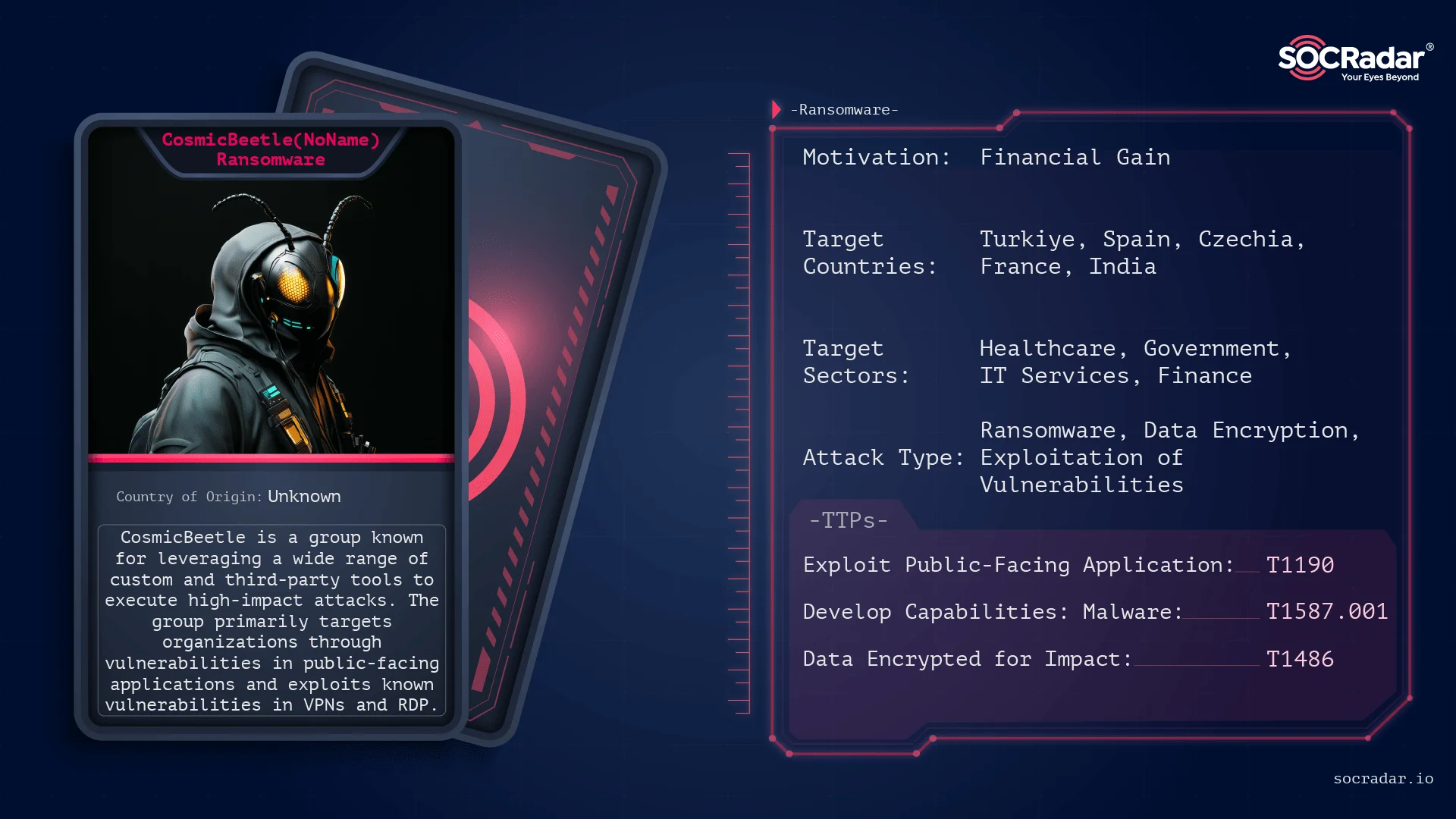
Threat actor card for CosmicBeetle(NoName)
CosmicBeetle has experimented with different malware families over the years, including Spacecolon, Scara, and ScRansom, an encryption tool based on Delphi. ScRansom is known for its partial encryption capability, offering operators multiple encryption speeds and an “ERASE” mode that permanently destroys file content, rendering it irretrievable. This ransomware can encrypt files across multiple storage media, including networked and removable drives, and can be configured to target specific file extensions, enhancing its versatility in attacks.
In their quest for notoriety, CosmicBeetle once mimicked LockBit’s data leak site (DLS), launching a site called “NONAME” that replicates LockBit‘s theme and ransom note style. While the group doesn’t exfiltrate data consistently, they employ this site to create a sense of urgency among victims, coercing them into compliance. Their attempts at replicating LockBit’s methods illustrate a strategy to leverage the reputation of established ransomware groups while bolstering their own visibility on the Dark Web and the media as well.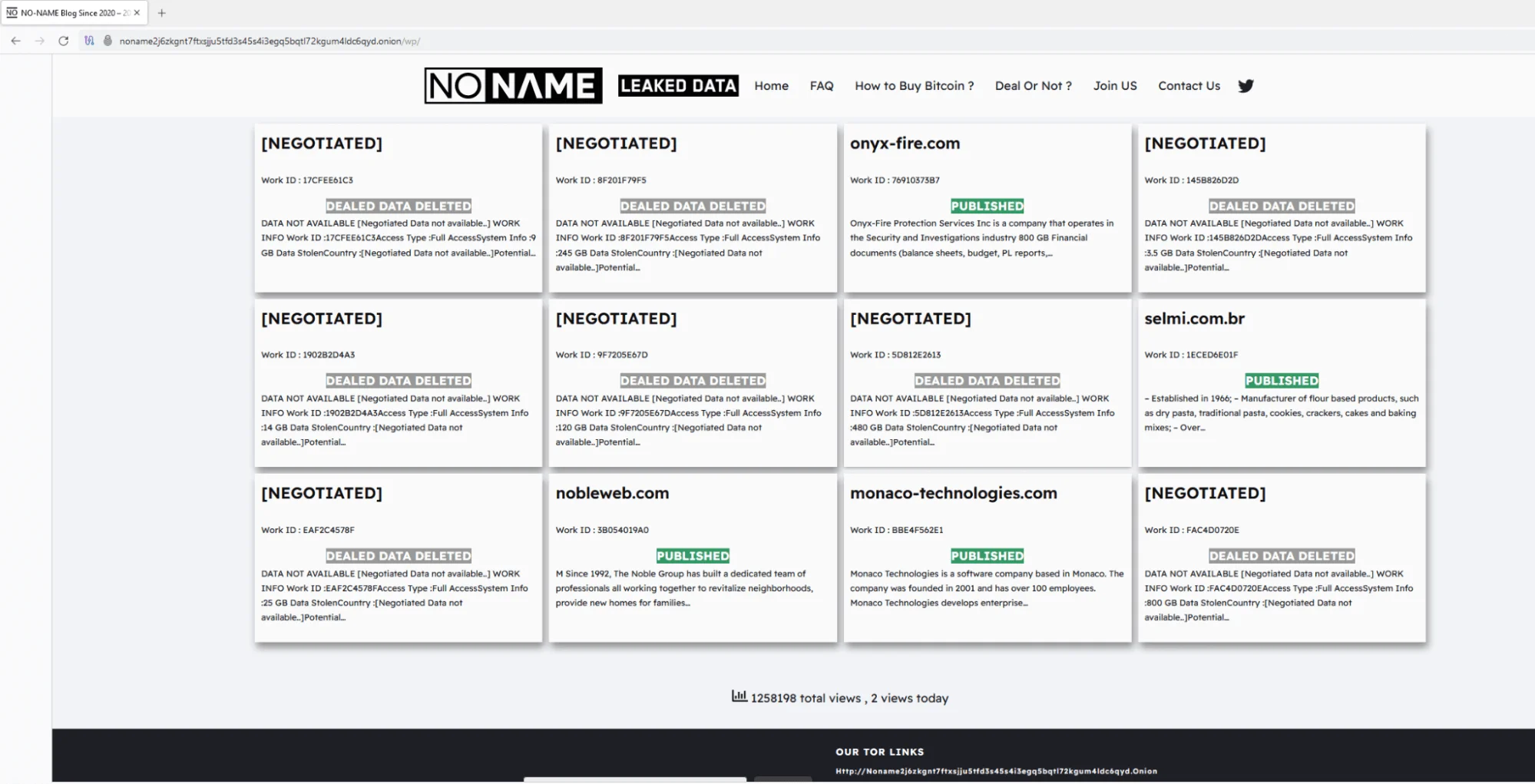
Overly similar DLS site design to LockBit’s DLS (ESET)
At the time of writing, all of CosmicBeetle’s DLS domains are inactive. However, with a rebrand, or even by adopting literally a no-name approach as an affiliate of RansomHub or another RaaS program, they are highly likely to remain active.
CosmicBeetle primarily targets small to medium-sized businesses (SMBs) in various sectors worldwide. According to ESET’s telemetry, this group has been highly active across different verticals, particularly focusing on regions in Europe and Asia. The most commonly affected industries include manufacturing, pharmaceuticals, healthcare, technology, legal, education, hospitality and leisure, financial services, and even regional government bodies. This broad array of targets reflects a strategic approach aimed at sectors where cybersecurity measures might be less mature or underfunded, making these businesses more susceptible to exploitation.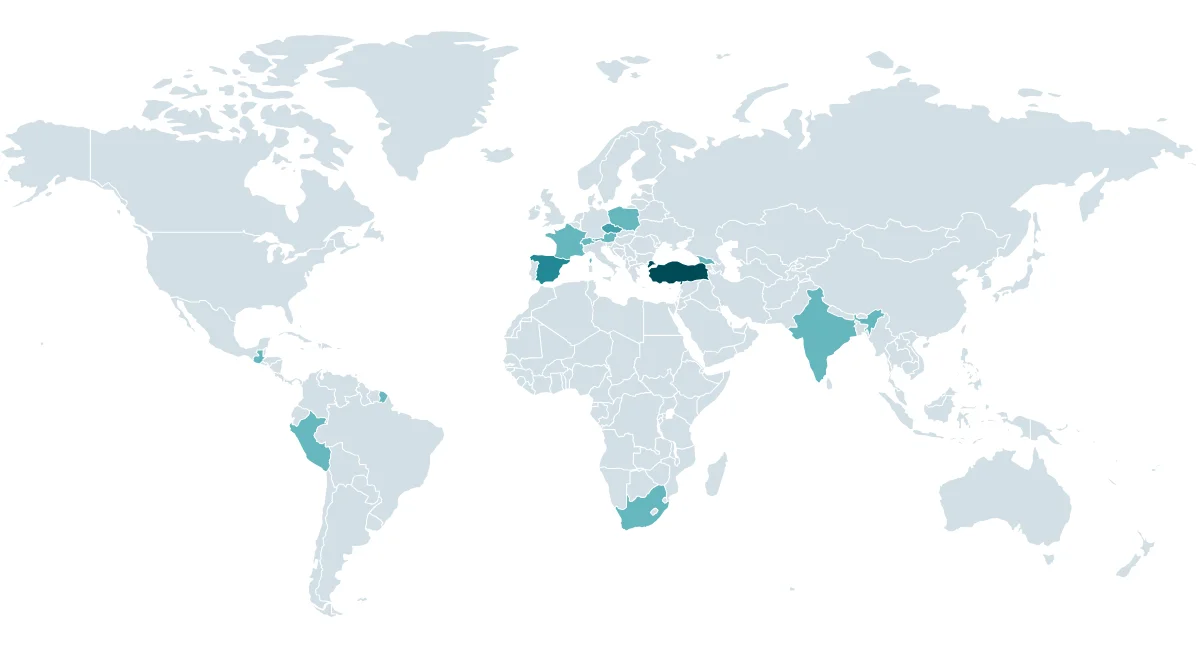
Heatmap of CosmicBeetle attacks since August 2023, according to ESET telemetry (ESET)
CosmicBeetle’s focus on SMBs is influenced by two key factors. Firstly, SMBs are often more likely to rely on vulnerable, outdated software and are less likely to have comprehensive patch management policies, which CosmicBeetle capitalizes on. Secondly, these organizations may not have the resources or expertise to counteract advanced threat actors, making them ideal targets for ransomware campaigns. CosmicBeetle’s consistent attack patterns reveal an intent to exploit vulnerabilities across a wide range of industries with a particular emphasis on sectors handling sensitive data or operationally critical infrastructure, where even temporary disruptions can lead to significant financial losses.
CosmicBeetle’s operational tactics are notably aggressive and persistent, leveraging both brute-force attacks and exploiting well-known vulnerabilities in widely-used systems. The group primarily uses brute-force techniques to gain unauthorized access to target networks, but they also rely heavily on exploiting a set of critical vulnerabilities. According to ESET’s report, these include:
CosmicBeetle has evolved its toolkit over time, with its main ransomware, ScRansom, becoming the centerpiece of its attacks. Originally deploying Scarab ransomware, the group shifted to ScRansom in 2023, which they continually refine. Though ScRansom is not the most sophisticated malware, it has proven to be effective against poorly-secured systems, enabling the group to cause substantial disruption. ScRansom’s design often results in significant data loss; victims attempting to pay for decryption may experience issues due to the ransomware’s need for multiple decryption keys, sometimes leading to irrecoverable data loss. CosmicBeetle’s attempts to impersonate other prominent groups, like LockBit, further add to the confusion for their victims.
NoName Ransomware’s victim posting from 2021
The group also made use of the leaked LockBit Black builder to craft ransomware samples, adopting the visual style and ransom notes of LockBit in an attempt to capitalize on the fear associated with the LockBit name. This tactic included establishing their own LockBit-inspired dedicated leak site (DLS) on the Tor network, named “NONAME,” where they posted victim data. This site mirrored LockBit’s leak site design, down to the Work ID strings in ransom notes, all of which contributed to the perception that these attacks were associated with LockBit. Additionally, CosmicBeetle went as far as registering a domain, lockbitblog[.]info, which closely mimicked LockBit’s official site. This website featured LockBit’s logo and provided ransom notes in Turkish, strengthening the illusion of a connection to the infamous gang. These impersonation tactics highlight CosmicBeetle’s resourceful approach to enhancing the perceived legitimacy and threat level of their operations.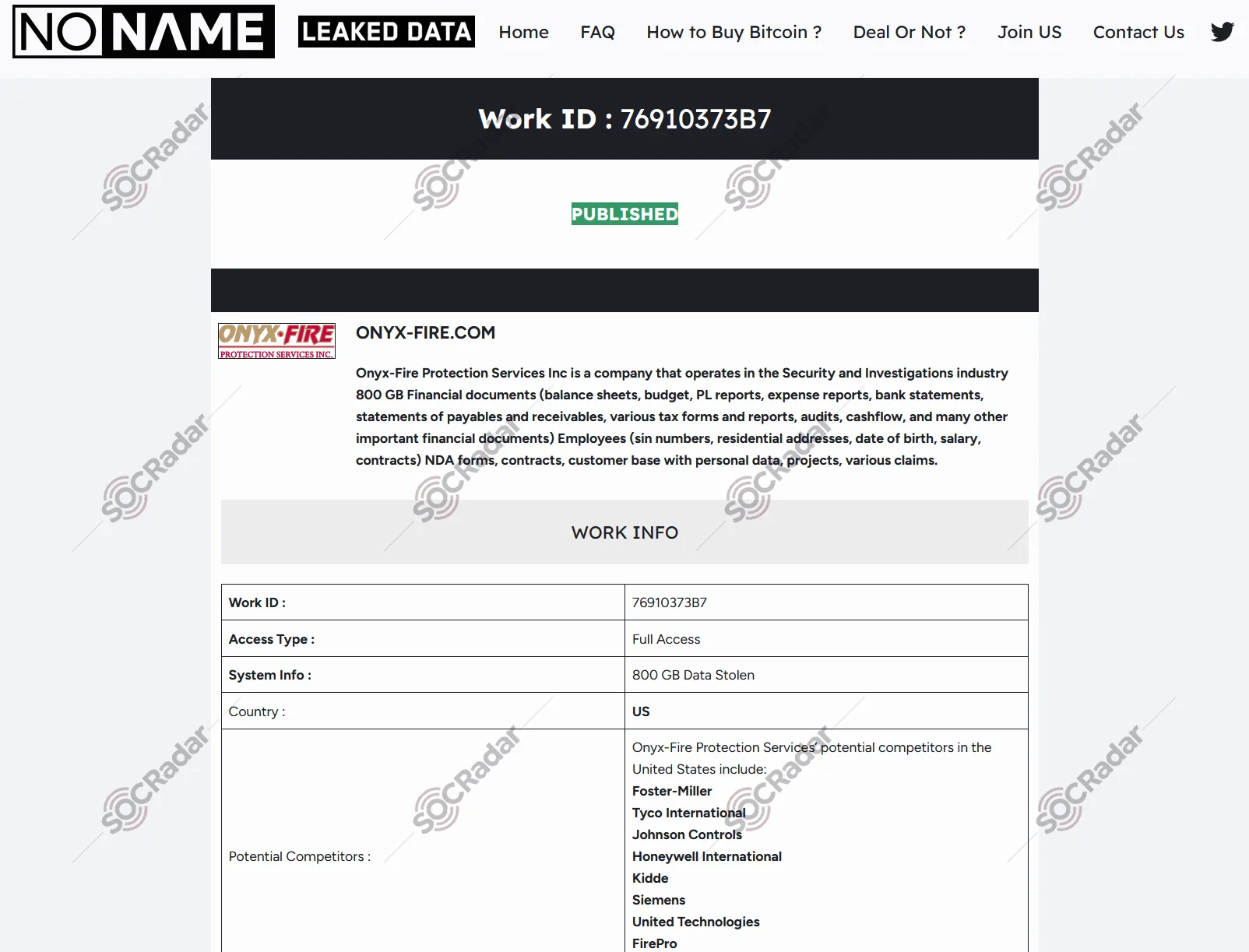
Before the inactivity, a victim’s data allegedly published
In their communications, CosmicBeetle relies on anonymous, peer-to-peer messaging applications, primarily qTox, which uses the encrypted Tox protocol. This protocol is popular among ransomware groups for its robust end-to-end encryption, ensuring secure communication with victims during ransom negotiations. Victims are often warned against seeking assistance from third parties, such as recovery firms, with threatening messages that claim recovery efforts will worsen the damage. This direct communication is designed to instill fear and coerce victims into paying ransom without exploring alternative recovery options.
CosmicBeetle has also recently taken a significant step in their operational structure by aligning themselves with RansomHub, a rapidly growing Ransomware-as-a-Service (RaaS) operation. As an affiliate, CosmicBeetle gains access to additional resources and operational support from RansomHub’s infrastructure. This move reflects their desire to solidify their position within the ransomware ecosystem and extend their reach further. This affiliation not only enhances CosmicBeetle’s operational capabilities but also aligns them with a larger, more experienced network of threat actors, providing additional opportunities to exploit victims on a wider scale.
The CosmicBeetle group, while still immature compared to other established actors, is continually adapting and refining its methods. Their technical shortcomings are often masked by their use of deception, branding, and psychological tactics to extract ransoms from victims. CosmicBeetle’s strategy of mimicking other ransomware groups and aligning with RansomHub suggests a group determined to grow and become a more formidable player in the ransomware space.
To defend against ransomware attacks like those executed by CosmicBeetle, organizations must adopt a multi-layered defense strategy that covers all attack stages, from initial access to impact. Below are critical measures to minimize exposure and reduce the risk of ransomware infections:
SOCRadar’s advanced cybersecurity tools provide critical capabilities to detect, mitigate, and defend against ransomware attacks like CosmicBeetle. Here’s how SOCRadar helps organizations strengthen their defenses:
CosmicBeetle is an evolving ransomware group that has established itself in the cybercrime ecosystem. While their methods and techniques are still developing, the group’s growing capabilities—especially their use of Ransomware-as-a-Service (RaaS) through affiliations with networks like RansomHub—suggest that they will continue to expand their operations. They tend to focus on SMBs that are more vulnerable to ransomware attacks, using a combination of exploits, brute-force methods, and psychological tactics to extort victims.
Their shift towards more complex, multi-stage attacks that combine encryption with data theft indicates that they are aware of the value in both quick payouts and long-term reputational damage. The group’s success in mimicking more established ransomware actors like LockBit highlights their desire to appear as a high-level threat, despite still being a relatively lesser-known player.
CosmicBeetle’s future actions will likely depend on how quickly they can refine their tactics and grow their capabilities. With continued exploitation of vulnerabilities and evolving ransom tactics, CosmicBeetle may well become a significant threat to businesses worldwide. By understanding their patterns and TTPs, organizations can better prepare for and defend against the potential impact of this and other similar threat actors.
MITRE ATT&CK techniques by ESET:
For the latest IoCs, remember to visit SOCRadar platform.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
