Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
In Russian Народная CyberАрмияa (People’s CyberArmy) is a prominent hacktivist group involved in disruptive attacks on critical infrastructure and financial systems, demonstrating significant DDoS capabilities and strategic motivations. However, is the group a hacktivist movement or a Russian state-sponsored threat actor, we shall see.
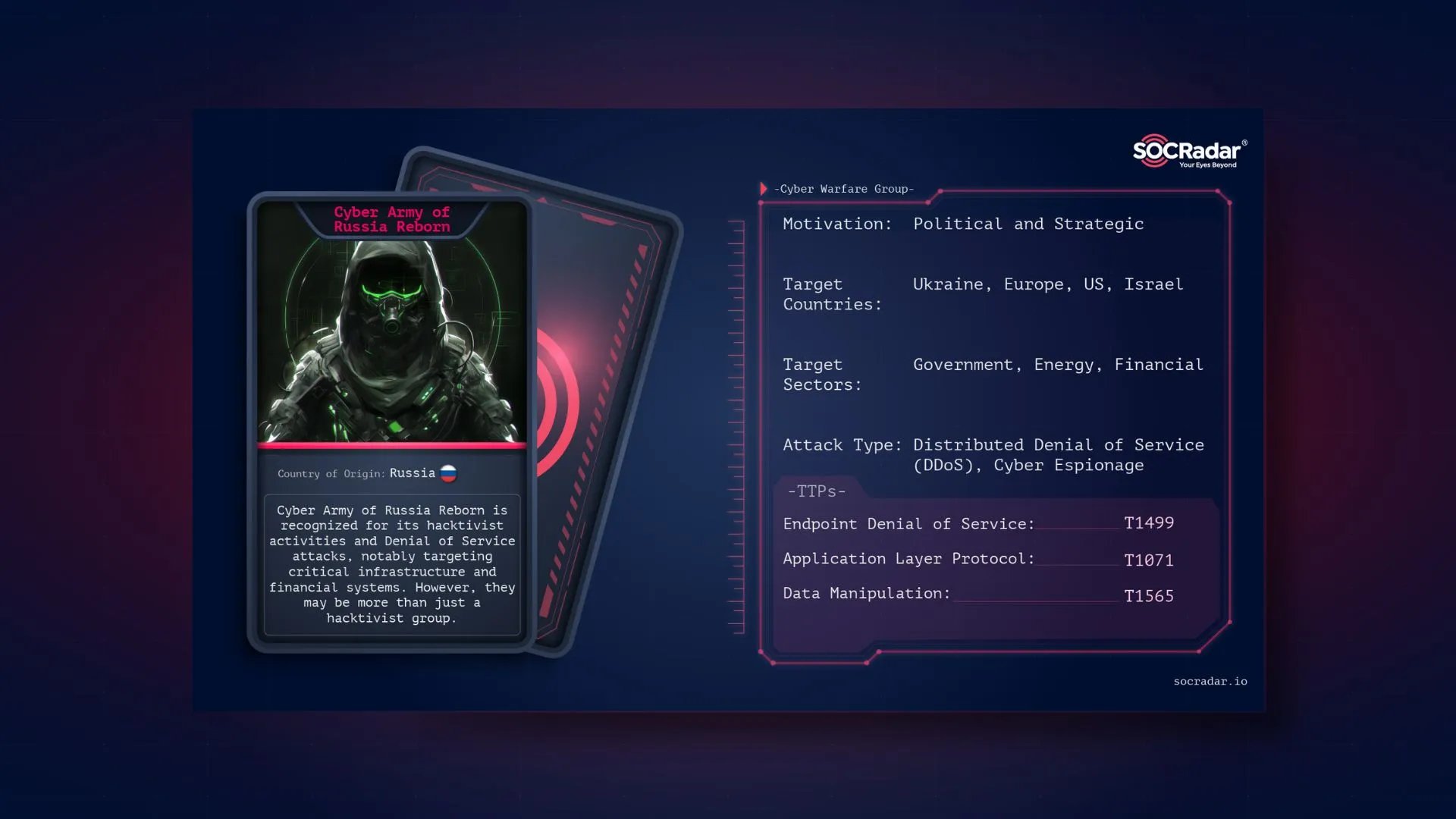
Threat actor card for Cyber Army of Russia
The People’s Cyber Army of Russia or Cyber Army of Russia Reborn is a player in Russia’s hacktivist landscape, conducting cyber threat activities against many countries. This group has been implicated in several significant cyberattacks, including many attacks on Ukraine’s critical infrastructure. Their operations are characterized by the use of Distributed Denial of Service (DDoS) attacks, among other tactics, to disrupt and damage their targets.
However, the Cyber Army of Russia reportedly has its roots in the broader landscape of Russian cyber warfare. This includes activities such as denial of service attacks, dissemination of disinformation, and disruptive activities.
Cyber Army of Russia Reborn’s logo on Telegram
It’s not that surprising, not directly related to the Cyber Army of Russia but Russian cyber actors are frequently reported to be attacking the foreign countries. Early notable operations include the large-scale cyberattacks on Estonia in 2007 and during Russia’s conflict with Georgia in 2008. The GRU, Russia’s military intelligence agency, has been a significant player in these operations, known for its aggressive and high-risk approach.
In this context, it is even claimed that hacktivist groups are involved in Russia’s cyber warfare strategy. For further information check out our blog post about hacktivism.
As reported by Mandiant in April, the origins of the Cyber Army of Russia could be traced back to Sandworm, a notorious cyber unit within Russia’s GRU military intelligence agency. For over a decade, Sandworm has been the Kremlin’s most aggressive cyber warfare force, responsible for some of the most devastating cyberattacks in history. Notable operations include triggering blackouts across Ukraine and unleashing the NotPetya malware, which caused widespread damage globally.
Dark Web Profile: Sandworm APT
The Cyber Army of Russia Reborn has distinguished itself with a series of brazen cyberattacks targeting critical infrastructure in the United States and Europe. Unlike its predecessor, which often prepared for attacks in secret or indirectly impacted victims, the Cyber Army of Russia Reborn has openly targeted water utilities and hydroelectric facilities. Their attacks have involved the manipulation of human-machine interfaces, and software that controls physical equipment, leading to attempts to sabotage essential services.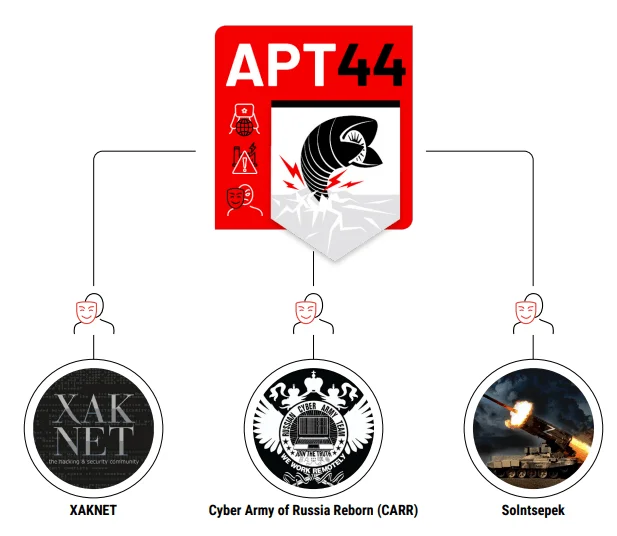
Hacktivist Telegram personas associated with Sandworm/APT44 (Mandiant)
Mandiant has reported that the Cyber Army of Russia Reborn may have been created or supported by Sandworm, noting instances where data stolen by Sandworm was later leaked by this new group. However, it remains unclear whether the Cyber Army of Russia Reborn is simply another cover for Sandworm’s activities or a distinct group that has branched out with its own operations.
Thus, the rise of the Cyber Army of Russia Reborn signals an evolution in Russia’s cyber warfare strategy, and that’s not it, the hacktivist threat landscape grows ever larger, and not only the Russian groups are involved.
The “High Society” hacker alliance has emerged as a vast coalition within the cybercriminal world, bringing together several well-known pro-Russian hacker groups, including the Cyber Army of Russia, UserSec, and NoName. This alliance has gained attention due to its coordinated cyberattacks, particularly against Western targets, reflecting a shared motivation rooted in political and ideological goals aligned with Russian interests.
The Cyber Army of Russia’s involvement in this alliance highlights its role in orchestrating and executing large-scale cyberattacks, often with the intent to disrupt or retaliate against entities perceived as antagonistic to Russian policies. The High Society collective has been expanding its reach, recently claiming responsibility for attacks on Italian companies, showcasing their growing capabilities and collaborative efforts.
This hacker coalition’s activities underline the increasing trend of politically motivated cyberattacks, where hacking is used as a tool to further nationalistic or ideological agendas. The collective’s operations are marked by their focus on targets that align with their pro-Russian stance, often leveraging tactics such as DDoS attacks and data breaches to achieve their objectives.
Holy League announcement in High Society’s Telegram channel
The Holy League is a broader coalition within the pro-Russian cyber landscape that encompasses various hacker groups, including the High Society alliance. Unlike the more focused High Society, which consists of groups like the Cyber Army of Russia, UserSec, and NoName, the Holy League brings together a wider array of hacktivist collectives with only one cause, common enemies. Therefore, even if their attacks are somewhat limited to more basic tactics like defacement attacks and DDoS, a large collective’s focused attack could cause significant damage.
As proof of their actions and the damage they may cause, the group’s members were sanctioned last month. The US Treasury Department announced sanctions on two members of the Russian hacktivist group Cyber Army of Russia Reborn (CARR) for cyberattacks on US critical infrastructure. Yuliya Pankratova, the group’s leader, and Denis Degtyarenko, a key hacker, were named.
The Cyber Army of Russia Reborn (CARR) has emerged as a significant threat in the realm of hacktivism, particularly focusing on entities that oppose Russian interests, including those associated with NATO and countries that support Ukraine. Their attacks are multifaceted, often combining technical disruption with psychological and informational warfare. CARR employs large-scale Distributed Denial of Service (DDoS) attacks, using botnets to overwhelm the networks of their targets, rendering them inaccessible. These attacks are designed to cripple the digital infrastructure of their enemies, causing disruption in critical services.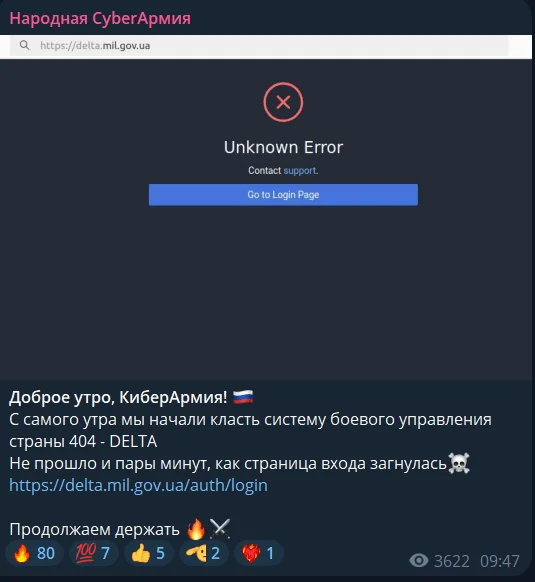
Recent DDoS attacks against Ukraine due to Kursk offensive
CARR’s targets include government agencies, financial institutions, media outlets, and critical infrastructure in Europe and the United States. Notably, in late 2023, the group expanded its operations to include more sophisticated attacks on Industrial Control Systems (ICS). These attacks have targeted sectors like water supply, energy, and wastewater management. For example, they claimed responsibility for the overflow of water storage tanks in Abernathy and Muleshoe, Texas, showcasing their ability to manipulate human-machine interfaces remotely.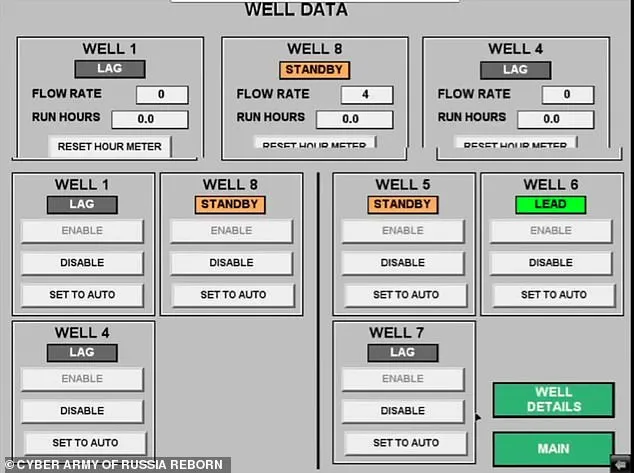
Alleged screenshots of hijacked ICS
The group is organized, utilizing platforms like Telegram to coordinate attacks, disseminate propaganda, and recruit supporters. Their Telegram channel serves as a hub for organizing DDoS attacks, sharing techniques, and amplifying their messages. Through these platforms, they engage in disinformation campaigns, spreading narratives that align with Russian state objectives, particularly concerning the ongoing conflict in Ukraine.
Thus, if we acknowledge the allegations about the hacktivism of Russian actors, CARR’s attacks are not just limited to technical disruptions; they are part of a broader strategy of hybrid warfare, combining cyberattacks with information operations to achieve strategic goals. By targeting critical infrastructure, government agencies, and key industries, they aim to sow chaos, disrupt operations, and undermine public confidence in the affected nations.
In summary, Cyber Army of Russia Reborn is a highly adaptive and dangerous hacktivist group, capable of both technical and psychological warfare, with a clear agenda aligned with Russian geopolitical interests. Their use of DDoS attacks, combined with more advanced ICS manipulation, makes them a significant threat to global cybersecurity.
Cyber Army of Russia Reborn (CARR) represents a significant and multifaceted threat in the realm of hacktivism. This group targets entities that oppose Russian interests, including those linked to NATO and countries supporting Ukraine. Their operations extend beyond mere Distributed Denial of Service (DDoS) attacks; they integrate technical disruption with psychological and informational warfare.
CARR employs large-scale DDoS attacks using botnets to overwhelm and incapacitate their targets’ networks, causing substantial disruptions in critical services. Their recent activities have expanded to more sophisticated attacks, including manipulations of Industrial Control Systems (ICS) affecting water supply, energy, and wastewater management. Notably, they have been linked to incidents such as the overflow of water storage tanks in Abernathy and Muleshoe, Texas, demonstrating their capability to remotely interfere with human-machine interfaces.
The group’s organization is evident through their use of platforms like Telegram for coordinating attacks, spreading propaganda, and recruiting supporters. Their Telegram channel is instrumental in organizing DDoS operations, sharing attack techniques, and promoting disinformation campaigns aligned with Russian state objectives.
Given CARR’s advanced and varied attack strategies, including both technical and psychological components, it is crucial for organizations in NATO member states and those supporting Ukraine to enhance their defenses. Key sectors like government, financial institutions, media, and critical infrastructure must prioritize robust DDoS protection and ICS security measures to safeguard against these threats.
Additional precautionary measures include:
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
