
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
GlorySec is a hacktivist group that has quickly gained notoriety for targeting governments and institutions it deems corrupt, particularly in Russia and Venezuela at the time of writing. Their attacks are often publicized on their Telegram channel, where they blend anti-authoritarian rhetoric with reports of their cyber activities.
GlorySec is still a relatively new but rapidly growing hacktivist group that aligns itself with, as in their statements, Anarcho-Capitalist ideals. By the definition of these ideas, the group possibly advocates for minimal government intervention, promoting individual freedoms through the non-aggression principle—a core tenet of their ideology. As in their actions, GlorySec claims to support Western political values, positioning themselves against what they view as authoritarian regimes and corrupt institutions, with a particular focus on countries like Russia, China, and their allies.
Their logos on GlorySec Telegram channel
Their operations are primarily conducted and publicized through Telegram, where they frequently share details about their cyberattacks, including data breaches and distributed Denial-of-Service (DDoS) attacks. GlorySec once collaborated with other hacktivist groups, such as ThreatSec and KromSec, to amplify their impact. The group’s rhetoric is allegedly deeply anti-authoritarian, framing their cyberattacks as a form of digital resistance against oppression and corruption. They have openly declared their mission to expose and dismantle corrupt systems, often encouraging others to join their cause or continue their efforts under the GlorySec banner, as in their sayings.
Again, similar to many hacktivist organizations, in addition to data leaks, there are also attack shares such as DDoS, Doxxing, Defacement, and access share in the main Telegram channels and backup channels where they share data leaks.
One of the group’s most interesting aspects is choosing their leaders through “democratic” voting for the supposed leadership role.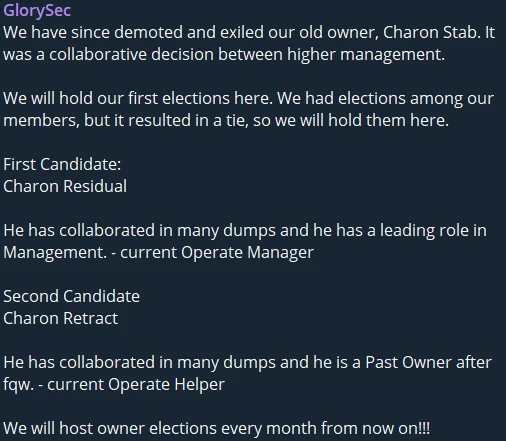
The post about their first leadership elections
While their methods of selecting a leader and openly participating in target selection reflect a democratic approach for the hacktivist group, the abrupt decisions to end operations on Telegram, the consistency of their attacks, and their reflective actions make it hard to take the group’s “threat” level seriously, despite fitting the hacktivist label.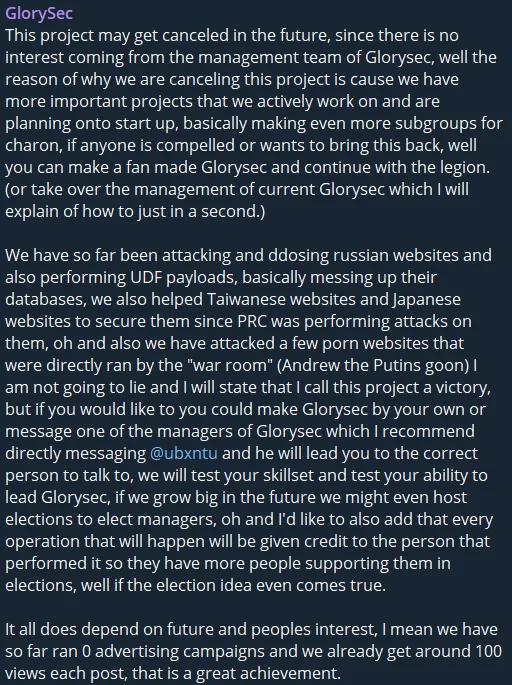
Project could have been canceled, GlorySec’s Telegram channel
GlorySec, while generally targeting entities in the Eastern Hemisphere, tends to follow a Western-aligned agenda, though not consistently. The table below ranks the downloadable leaks from the channel labeled GlorySec Storage.
Leak post numbers in their Telegram channel
In addition to leak posts, as we mentioned above, there are also DDoS, Defacement, and Doxxing attacks and targets such as Burkina Faso and Armenia.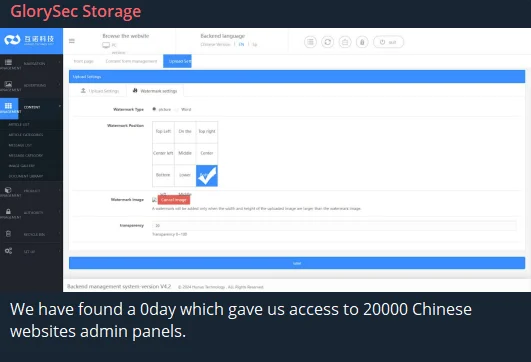
Alleged 0day access for 20.000 Chinese websites
It should be noted that even if they make more assertive claims, such as zero-day exploits, their accuracy is not sure. The group, which has recently shifted its primary focus to Venezuela, continues to launch various attacks, with a particular emphasis on defacement.
GlorySec has quickly gained attention with its anti-authoritarian campaigns, particularly targeting governments and institutions in Russia and Venezuela. While their attacks are frequently publicized and backed by hacktivist ideals, the group’s erratic actions and inconsistent agenda raise questions about their long-term threat. Nevertheless, staying vigilant and monitoring their movements through platforms like SOCRadar can provide crucial threat intelligence and help mitigate potential risks.
SOCRadar’s Operational Intelligence, Threat Actors Intelligence tab can provide valuable insights into hacktivist groups like GlorySec by monitoring their online activities, especially on platforms like Telegram where they announce their operations. With real-time alerts, organizations can stay informed about emerging threats, leaked data, and ongoing campaigns. The module’s comprehensive tracking of ransomware, DDoS, and other cyberattacks ensures a proactive defense by enabling timely response measures.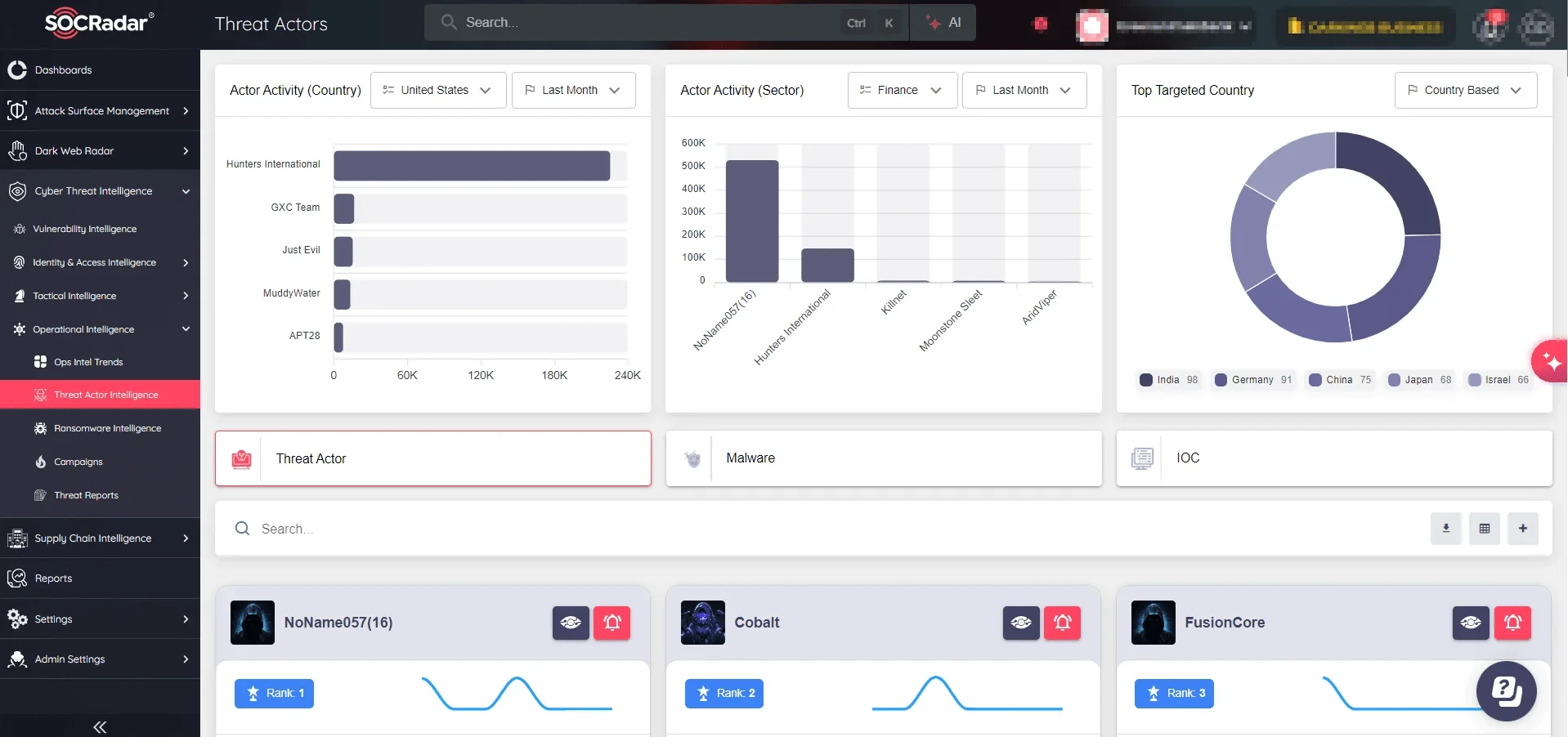
SOCRadar Operational Intelligence, Threat Actors Intelligence
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
