
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
In recent months, the Malek Team, a hacker group with alleged links to Iran, has escalated its cyber offensive against key Israeli institutions, marking a significant uptick in digital threats within the region. The Malek Team, which has previously targeted a private college in Israel, claimed responsibility for a sophisticated cyberattack on Israel’s Ziv Medical Center. The breach at the medical center was particularly alarming due to the sensitive nature of the stolen data, which included a substantial volume of medical records. This attack was not an isolated incident; instead, it is part of a series of coordinated cyberattacks that have targeted various sectors in Israel.
Their logo on their website
The Malek Team is possibly an Iranian linked threat actor group that was spotted after the Israel-Hamas conflict had begun. The group also appears to recruit from anti-Israel hacktivists, often from South Asia and the Middle East.
Their activities became increasingly bold and sophisticated, their attacks extending beyond the healthcare sector with Ziv Medical Center to encompass educational institutions such as Ono Academic College. These incidents highlight a worrying trend of cyber espionage and data theft from Iranian threat actors, with the hackers obtaining and leaking sensitive information, including personal details of Israeli Defense Force (IDF) soldiers and private student records.
As the Malek Team continues its cyber operations, the implications of these breaches extend far beyond the immediate impact on the targeted institutions. They represent a broader challenge to cybersecurity in a region already marked by complex geopolitical tensions.
Ziv Hospital
The Malek Team claimed responsibility for a significant cyberattack on Ziv Medical Center in December 2023, a major healthcare facility in Safed, Israel. This attack allegedly resulted in the exfiltration of a staggering 500GB of data, including over 700,000 documents containing highly sensitive personal and medical information of patients. Notably, some of these records are said to belong to members of the Israeli Defense Forces (IDF), adding a layer of national security concern to the breach.
Malek’s Team website, latest victim listed as ZIV Hospital
The cyberattack on Ziv Medical Center didn’t just compromise patient records. It also underscored the vulnerability of critical healthcare infrastructure to sophisticated cyber threats. Following the breach, the Israeli National Cyber Directorate took immediate action, issuing warnings and initiating an investigation to assess the full extent of the impact. In response to the incident, the hospital took precautionary measures, such as temporarily disconnecting its email server and other critical computer systems to contain the breach.
This incident at Ziv Medical Center was not an isolated event but part of a troubling pattern. It marks the third time in four months that the hospital has fallen victim to a cyberattack. The repercussions of this attack raised significant concerns about privacy, trust in healthcare institutions, and the broader implications for national security, given the involvement of IDF personnel’s records.
Ono Academic College Data Breach
The Malek Team’s cyber activities came to the forefront with a significant breach reported at Ono Academic College, a private educational institution in Israel. In this incident, the hacker group claimed to have infiltrated the college’s network, accessing a substantial volume of sensitive data. Approximately 250,000 records containing private student information were compromised, including personal details and academic records.
The leaked information not only included basic personal details but also extended to more sensitive data, such as academic records and internal communications. The hackers reportedly released evidence of their infiltration online, including videos and documents, further exacerbating the breach’s impact.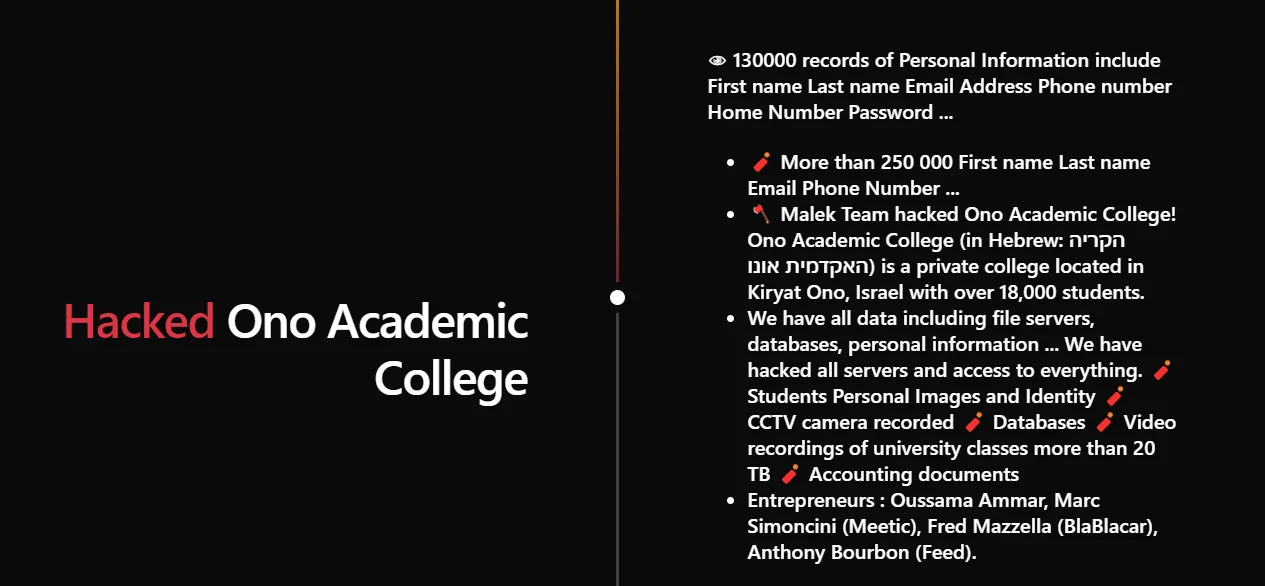
Malek’s Team website, Ono breach details with students and personnel pictures are shared on the website
The cyberattacks perpetrated by the Malek Team on Ziv Medical Center and Ono Academic College were not isolated incidents but part of a larger pattern of increased cyber threats in Israel. They also claimed other attacks in Israeli government bodies and the IDF but for now their attacks were limited just on Israel. These attacks highlight the growing sophistication of cybercriminals and the escalating cyber warfare in a region already marked by complex geopolitical dynamics.
Further claimed leaks about Israel
The targeting of diverse sectors, from healthcare to education, by groups such as the Malek Team, points to a broader strategy of exploiting any vulnerable point in the digital infrastructure of key institutions. This approach by cybercriminals underscores the reality that no sector is immune to digital threats. The sensitive nature of the data involved in these breaches, especially concerning IDF personnel, adds a layer of national security implications to the cyberattacks.
These incidents also reflect a wider trend of state-affiliated or state-supported cyber activities, particularly in the context of the ongoing tensions between Israel and Iran. While the direct involvement of state actors is not definitively established in these specific attacks, the pattern of targeting and the nature of data sought align with broader geopolitical motivations.
Moreover, the increasing frequency and scale of these attacks emphasize the need for continuous vigilance and robust cybersecurity measures. Institutions housing sensitive data must prioritize their digital defense mechanisms to protect against such sophisticated threats. This includes not only technological solutions but also a heightened awareness of cyber hygiene practices among individuals.
The implications of the Malek Team’s attacks extend far beyond the immediate impact on the targeted organizations. They signify a broader challenge in cybersecurity, where the lines between geopolitical rivalries and cyber warfare increasingly blur. In the context of Israel’s complex regional dynamics, these cyberattacks serve as a reminder of the digital battleground that complements physical and diplomatic conflicts.
In conclusion, the large-scale breaches by the Malek Team demonstrate that no sector is immune to cyber threats. In an era where digital risks are constantly evolving, continuous awareness, caution, and a collaborative approach to cybersecurity are vital. It is imperative for both individuals and organizations to stay informed and prepared to navigate these complex cyber landscapes effectively.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
