Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
[June 21, 2024] “Qilin Started Leaking Synnovis Data”
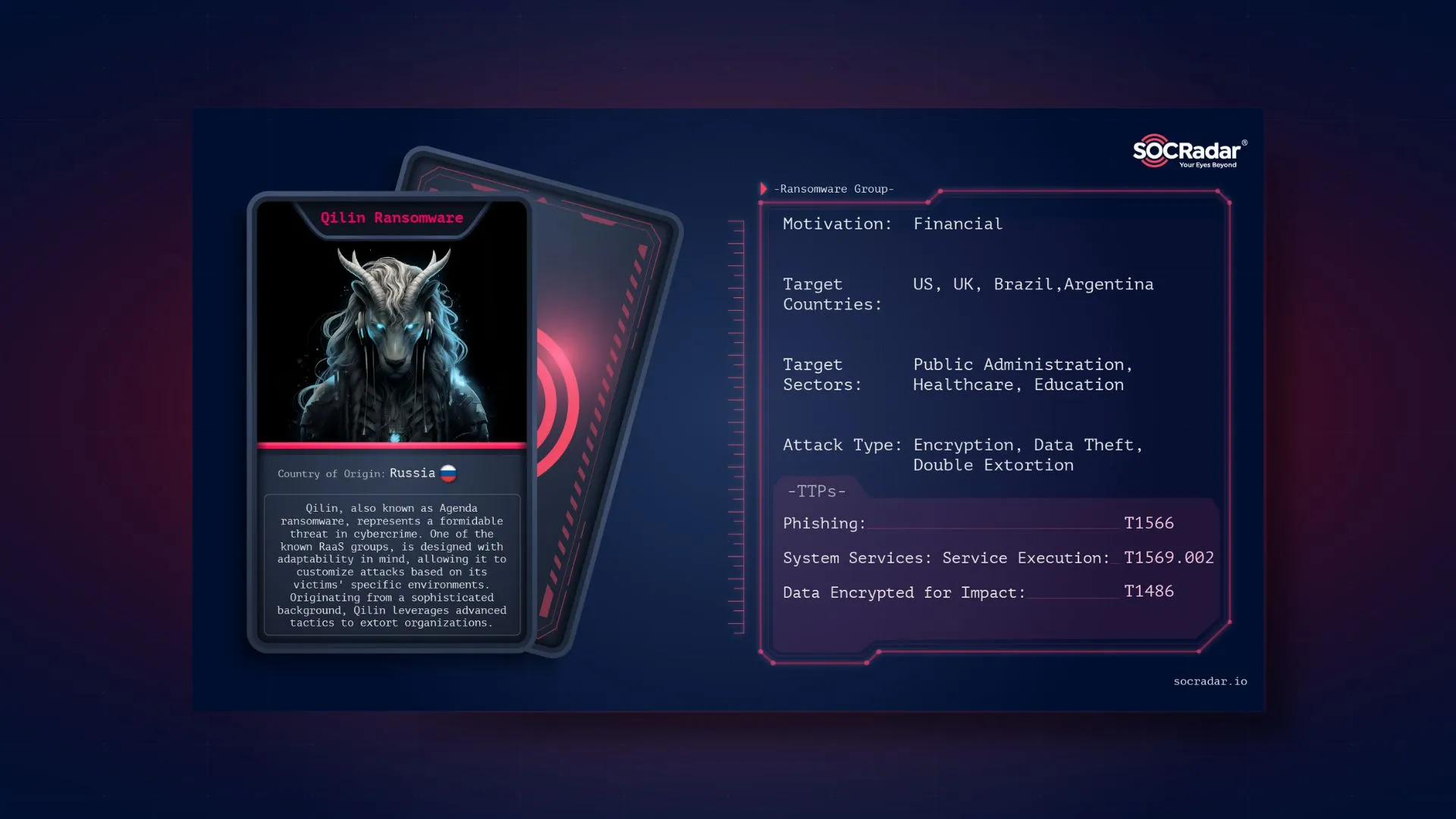
Qilin, also known as Agenda ransomware, represents a formidable threat in cybercrime. This ransomware, one of the known Ransomware-as-a-Service (RaaS) groups, is designed with adaptability in mind, allowing it to customize attacks based on its victims’ specific environments. Originating from a sophisticated background, Qilin leverages advanced tactics to extort organizations. Recently, they have been on the news with their devastating ransomware attacks on Healthcare.
Threat Actor Card for Qilin Ransomware
Qilin ransomware is a sophisticated cyber threat group that has emerged as a significant player in the ransomware landscape. Its name might be derived from the mythical Chinese creature Qilin, which symbolizes its strong and adaptable nature. However, the group is believed to be of Russian origin. This ransomware is distinguished by its advanced techniques, cross-platform capabilities, and targeted attacks, making it a formidable adversary for organizations worldwide.
Depiction of Qilin, Image created by Bing AI
Qilin ransomware first appeared on the cybercrime scene with a distinct approach and high level of sophistication. It has samples written in Go (Golang) and Rust, which are programming languages known for their efficiency and cross-platform compatibility. This allows Qilin to be easily compiled for various operating systems, including Windows and Linux, enhancing its versatility and reach.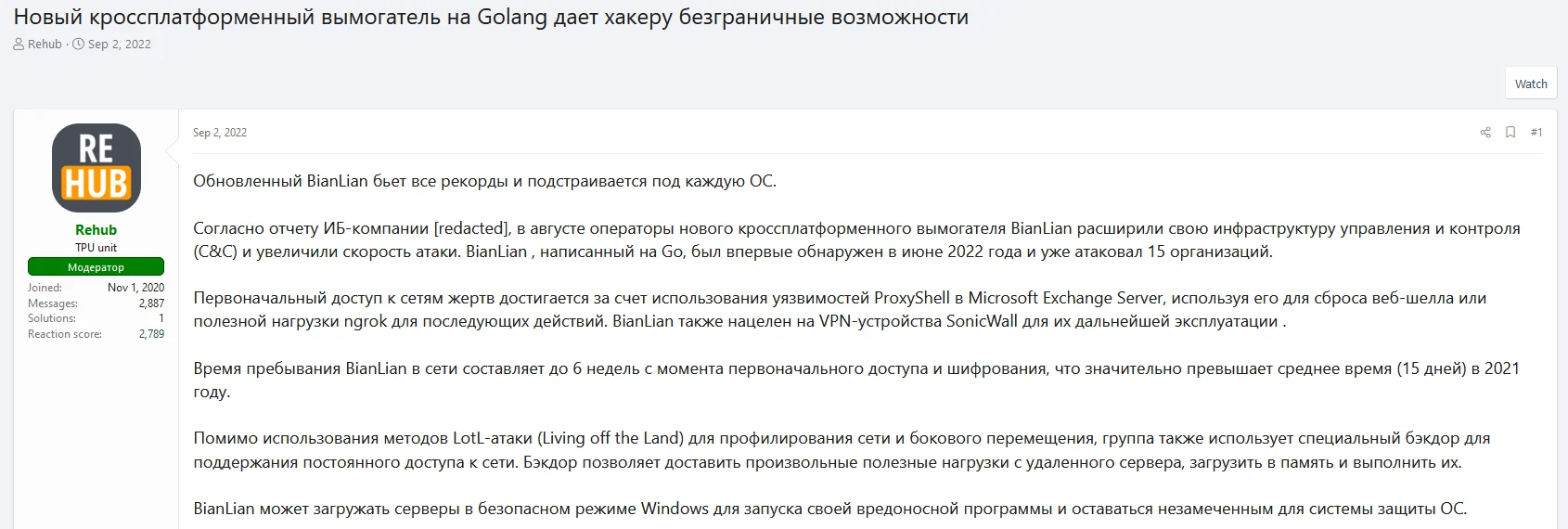
In 2022, ransomware variants written in Golang began to stand out in hacker forums. In addition to BianLian, Qilin (Agenda) Ransomware is one of the mentioned variants. As translated from Google Translate: “New cross-platform ransomware on Golang gives hackers unlimited possibilities”
The primary objective of Qilin ransomware is financial gain through extortion. It targets organizations across various sectors, with a particular focus on healthcare and education. These sectors are often chosen due to their reliance on critical data and the generally lower levels of cybersecurity compared to more financially-focused industries. By encrypting essential files and demanding a ransom for their decryption, Qilin aims to create significant operational disruptions, compelling victims to pay the demanded ransom to restore their systems.
Qilin ransomware has samples written in Go (Golang) and Rust, as we mentioned before these programming languages are known for their cross-platform capabilities and efficiency. This choice of language allows Qilin to be easily compiled for various operating systems, including Windows and Linux. The ransomware’s ability to customize attacks to individual victims’ environments makes it particularly dangerous.
Check out our blog post, “Why Ransomware Groups Switch to Rust Programming Language?”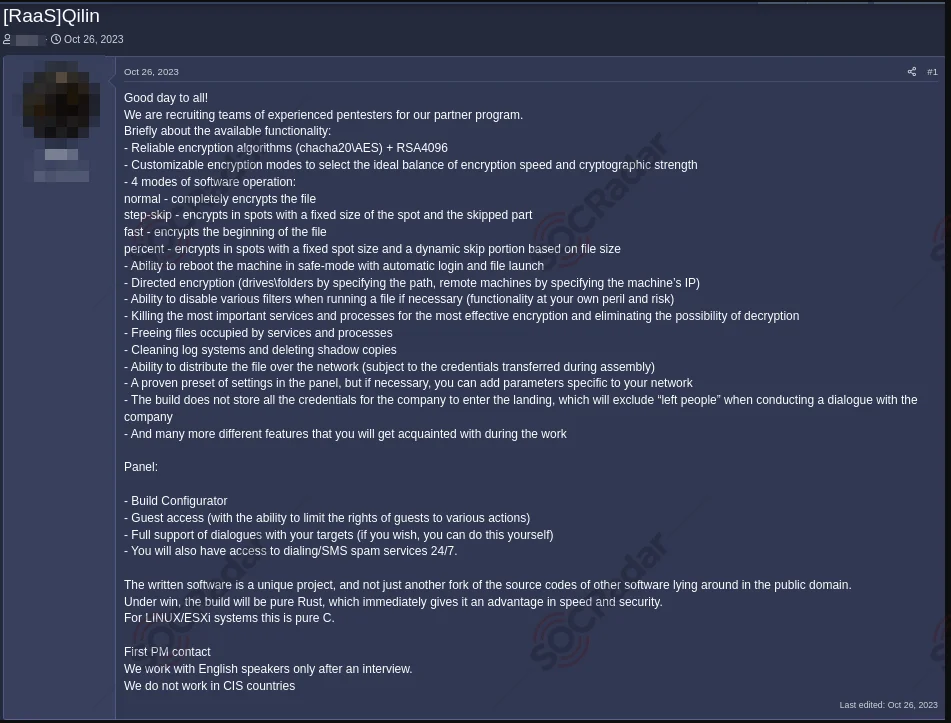
A recruitment post for Qilin in October 2023
The group showed that it was working like a classic Russian ransomware operator by excluding CIS countries from its targets and shared recruitment posts on hacker forums for affiliates.
Qilin ransomware typically initiates its attack through several primary vectors. One of the most common methods is via phishing emails, which often contain malicious attachments or links. When these are opened by unsuspecting users, they download and execute the ransomware payload. Additionally, Qilin exploits known vulnerabilities in software or operating systems to gain entry. Remote Desktop Protocol (RDP) attacks are another favored tactic, targeting weak or exposed RDP configurations to infiltrate systems.
Once Qilin has gained initial access, it employs advanced obfuscation techniques to evade detection. The ransomware code is packed, disguising its true nature to avoid static analysis. Further, Qilin uses various code obfuscation methods, such as renaming functions, altering control flows, and encrypting strings, to complicate reverse engineering efforts. This also makes Qilin difficult to detect with IoCs located lower on the pyramid of pain.
Qilin incorporates anti-analysis techniques, such as detecting and disabling debugging and sandbox environments, making it difficult for security researchers to analyze its behavior. This includes checks for virtual machines and other common sandbox artifacts to prevent dynamic analysis. So, we are actually faced with a typical ransomware attack chain, but they are successful in putting it into practice.
Upon successful deployment, Qilin seeks to escalate its privileges to gain administrative control over the infected system. This can involve exploiting system vulnerabilities or using legitimate tools like PowerShell or PsExec to achieve higher-level access. With elevated privileges, Qilin then scans the network for additional targets. It uses network enumeration to identify other systems, shares, and services within the network and employs credential dumping to extract passwords and other authentication details. This enables the ransomware to move laterally across systems, using compromised credentials to infect other machines within the network.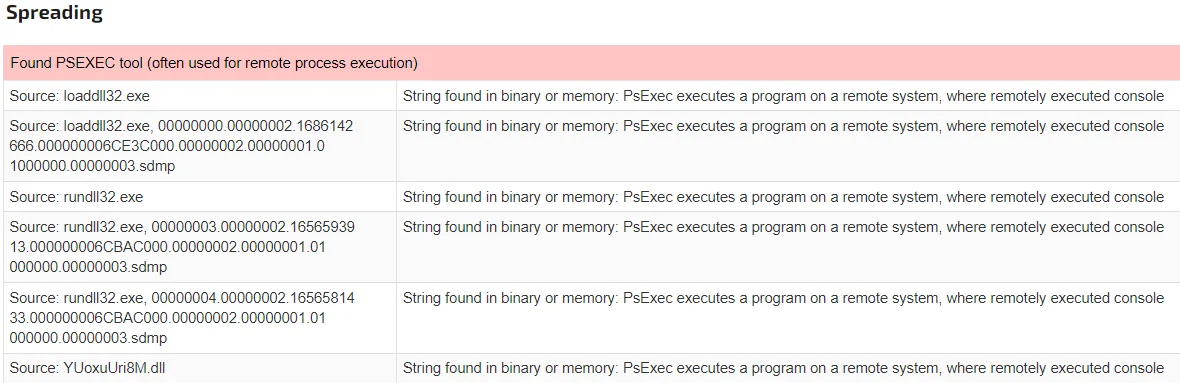
A sample written in Golang uses PsExec for remote execution (JoeSanbox)
Qilin ransomware employs a robust encryption mechanism that combines symmetric and asymmetric encryption to lock files. Initially, it uses symmetric encryption to encrypt files with a randomly generated key. This symmetric key is then encrypted with a public RSA key, ensuring that only the attackers, who hold the corresponding private RSA key, can decrypt it. Qilin targets a wide range of file types to maximize impact, including documents, databases, and backups, while avoiding critical system files to keep the system operational enough to display the ransom note.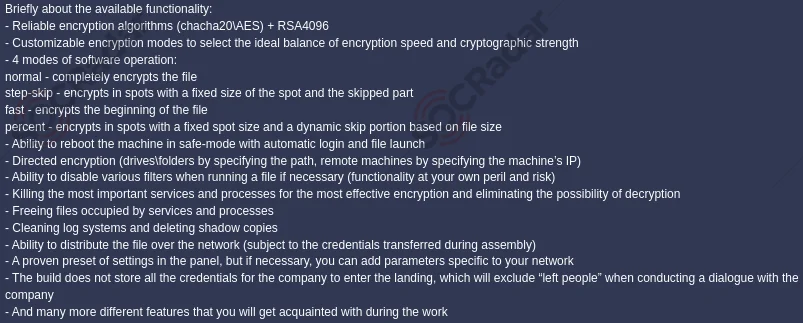
Qilin’s recruitment post includes details about its functionalities, the mentioned encryption algorithms are ChaCha20, AES, and RSA4096
After encryption, Qilin drops a customized ransom note on the infected systems. This note typically includes the demanded payment amount, usually in cryptocurrency, and instructions on how to contact the attackers for payment and decryption. The note often contains threats of data leakage or permanent data loss if the ransom is not paid within a specified timeframe.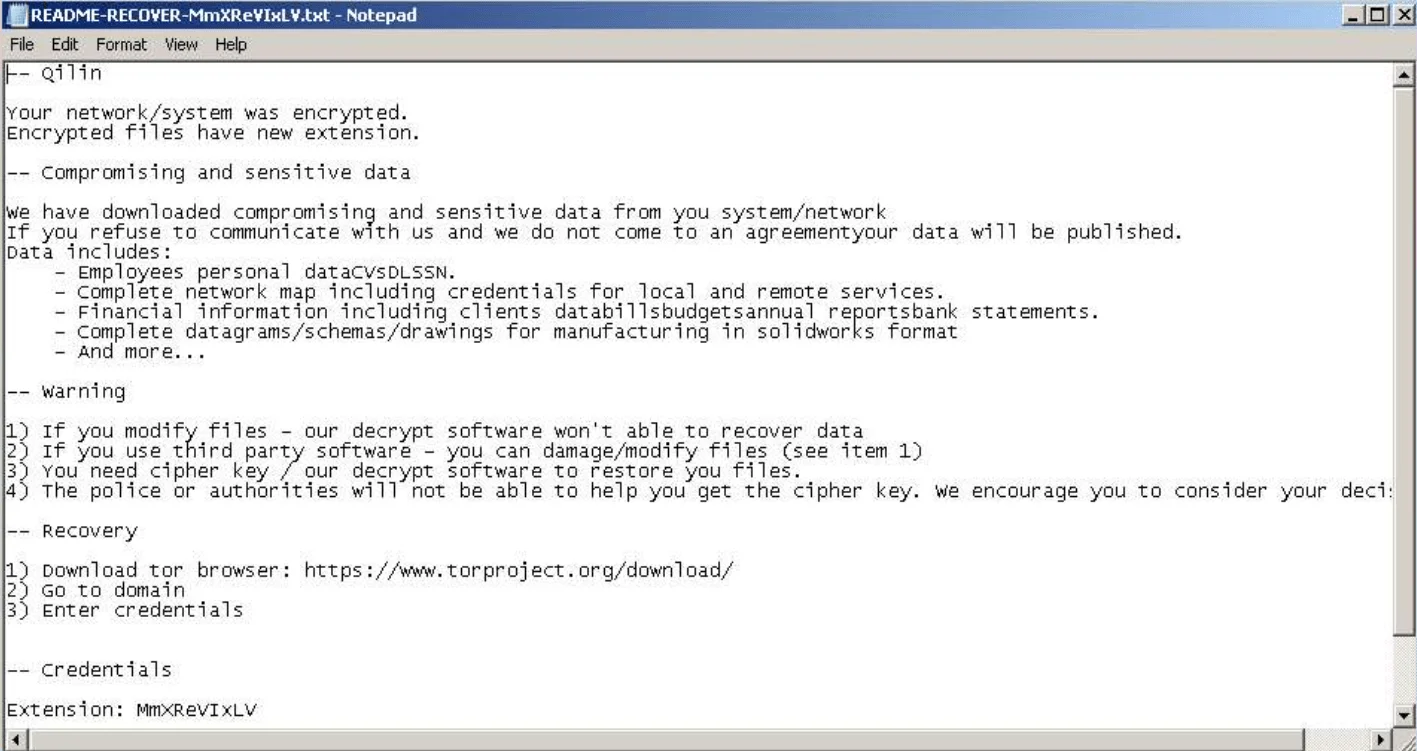
Ransomware note from a recently uploaded sample (Any.run)
Victims are directed to communicate with the attackers via Dark Web portals or encrypted messaging services, ensuring the attackers’ anonymity and complicating law enforcement efforts to track interactions. Payments are demanded in cryptocurrencies, such as Bitcoin or Monero, to maintain anonymity and complicate traceability. Even after payment, there is no guarantee that victims will receive the decryption tools required to recover their data.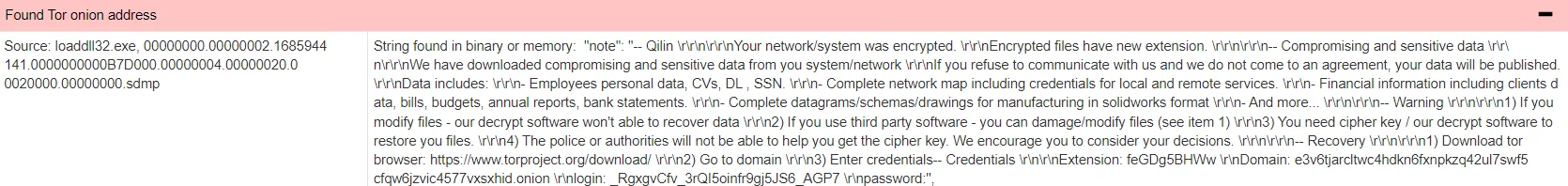
Victims are instructed to download the TOR Browser and redirected to their dark web portals (JoeSandbox)
To cover their tracks, Qilin ransomware deletes logs and other artifacts that could aid forensic investigations. This includes clearing event logs and removing any temporary files created during the attack. In some instances, Qilin may also include functionality to remove itself from the system after completing its objectives, further complicating post-incident analysis and response.
Qilin has shown a particular focus on the Healthcare, Education, and Public Administration industries, although it is not limited to these industries. These sectors are often targeted due to their reliance on critical data and their tendency to have weaker cybersecurity measures compared to financial or governmental institutions.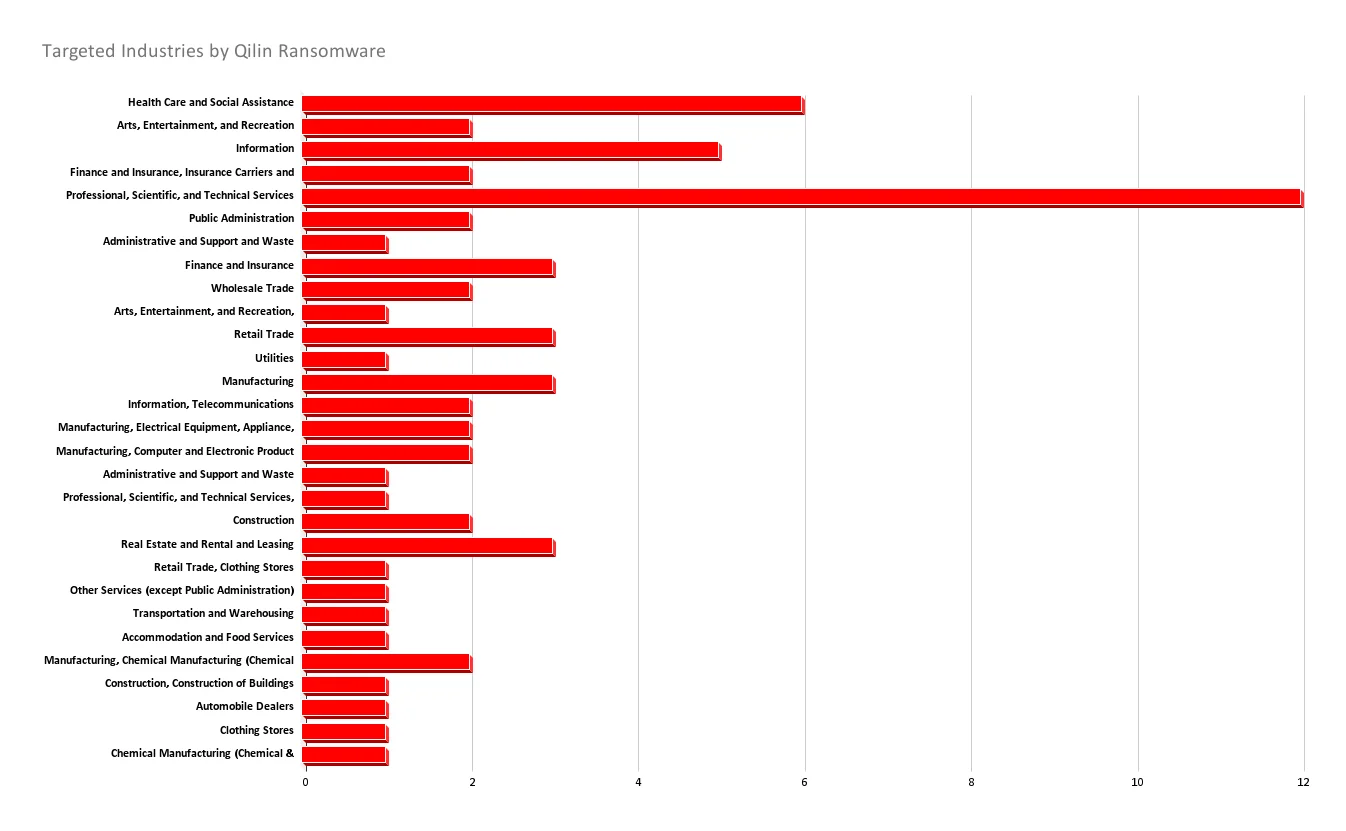
Most Targeted Industries by Qilin according to the SOCRadar data
When we look at the target countries chart, it seems that the US is the most targeted country as usual, followed by mostly EU countries. In Latin America and Asia, educational institutions are the main targets.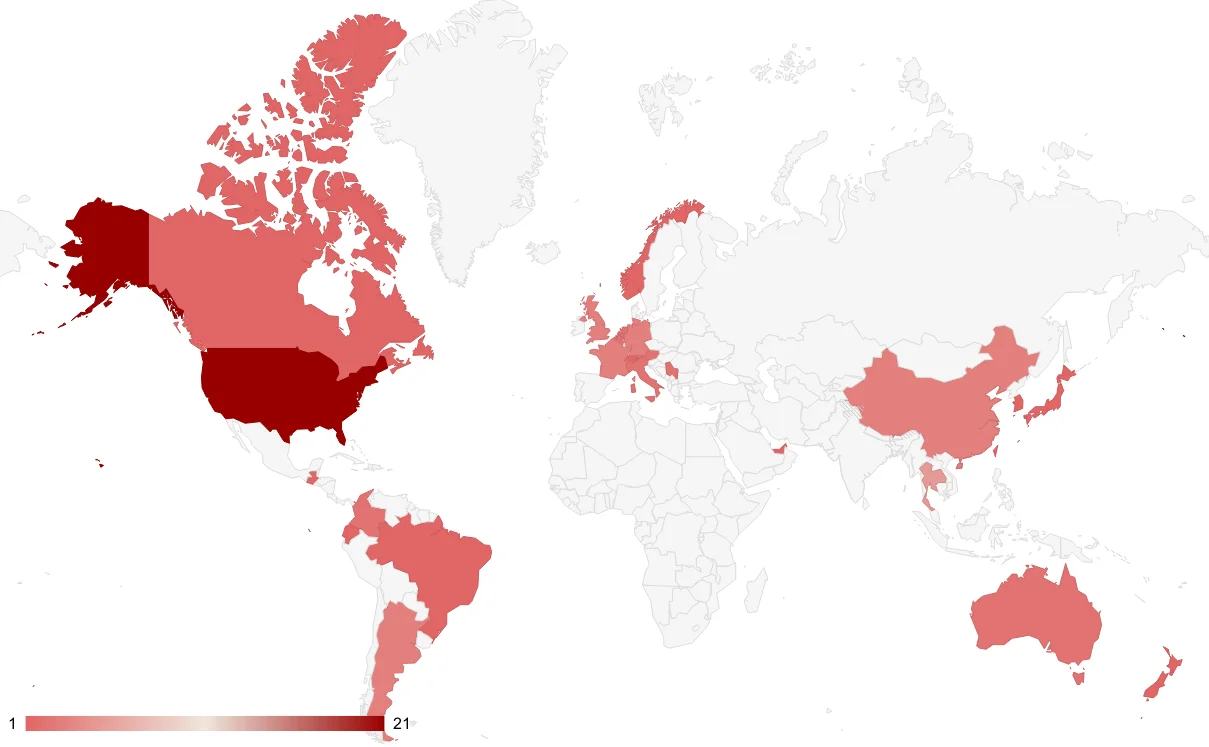
Most Targeted Countries by Qilin according to the SOCRadar data
In a recent incident, UK healthcare providers fell victim to Qilin, resulting in catastrophic following events. According to Ciaran Martin, the former chief executive of the National Cyber Security Centre, a Russian cyber hacking group is responsible for a ransomware attack that severely disrupted operations at three London hospitals. The attack targeted pathology services firm Synnovis, leading to a significant reduction in hospital capacity. Hospitals declared a critical incident, resulting in canceled operations, tests, and blood transfusions.
The group behind the attack was Qilin. The attack impacted various hospitals, including King’s College Hospital, Guy’s and St Thomas’, Royal Brompton, Evelina London Children’s Hospital, and primary care services in the capital. Thus, it should be noted that Qilin’s DLS website has not been accessible for a long time and there is no statement from the group.
This section will be updated as more information about the incident is revealed. A counter-operation move or an advisory can be expected from the security forces regarding this incident in the near future.
Qilin was aiming to extort a substantial ransom from the company. Reports indicate that Qilin is demanding a staggering $50 million from Synnovis for decryption tools and a promise not to publish the data. However, in a series of media interviews, the Qilin ransomware gang has claimed that their attack on the hospitals was not financially motivated but rather a protest against the British government’s involvement in an unspecified war.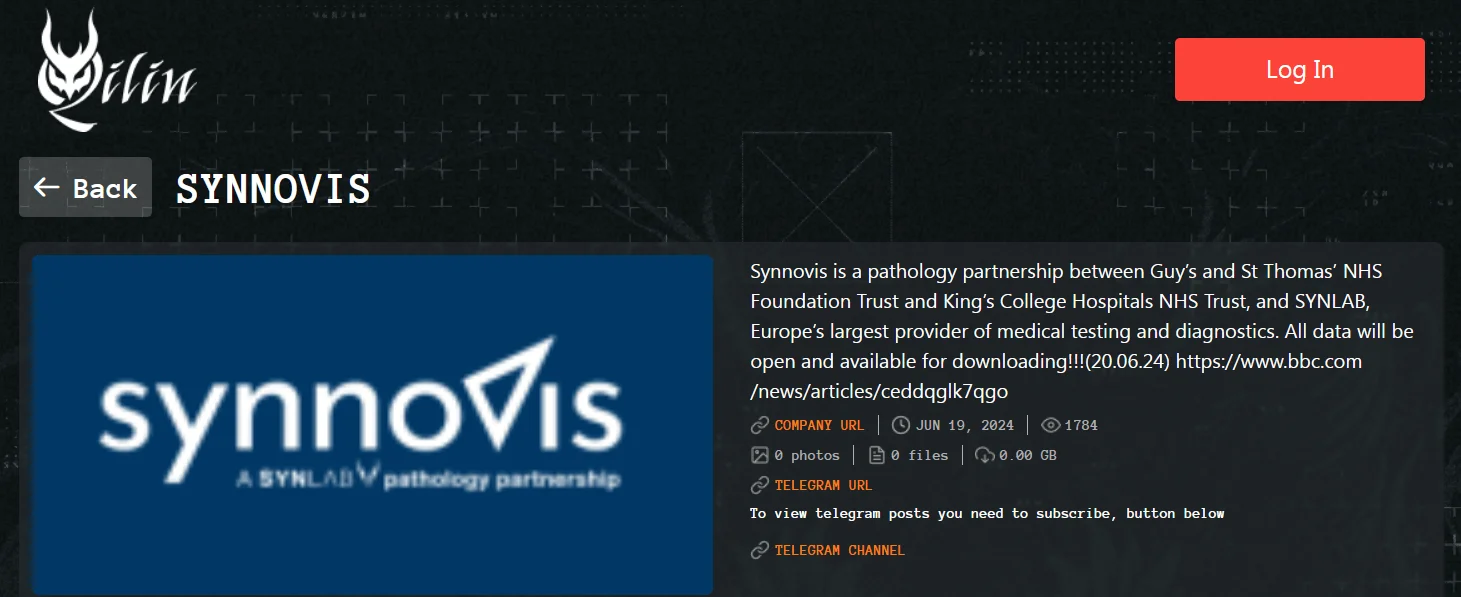
Qilin’s victim listing of Synnovis
Unable to reach an agreement, the Qilin group initiated a massive leak on their Telegram channels. After the June 20 deadline passed, Qilin began sharing nearly 400GB of purported Synnovis data, divided into more than 100 parts, on their Telegram channel.
104 parts of alleged Synnovis data has been shared on Qilin’s Telegram channel
As cyber threats continue to evolve, organizations must adopt a multifaceted approach to cybersecurity, especially in defending against ransomware attacks like Qilin. Leveraging advanced security tools and implementing proactive strategies are imperative in fortifying digital defenses.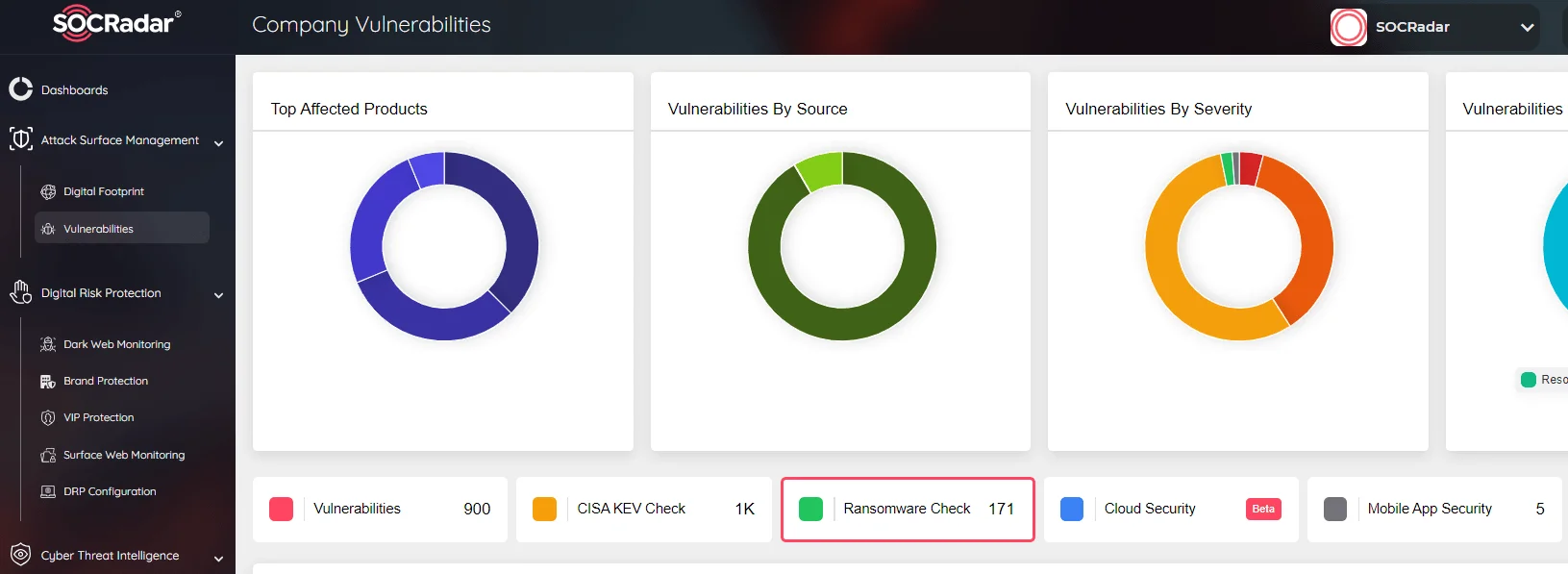
SOCRadar Attack Surface Management has Ransomware Check function
For further information about protection against ransomware also check out our blog post titled “How to Detect & Prevent Ransomware Attacks (2024 CISO Edition)”
By integrating these advanced security measures and proactive strategies into their cybersecurity framework, organizations can significantly enhance their resilience against ransomware threats and safeguard their sensitive data assets effectively. Adopting a proactive and holistic approach to cybersecurity is essential in mitigating the evolving threat landscape and maintaining a robust defense posture against ransomware attacks.
Qilin (Agenda) ransomware represents a significant threat due to its adaptability and sophisticated attack methods. Organizations must remain vigilant and proactive in their cybersecurity efforts to defend against such advanced threats. By understanding the tactics and techniques employed by Qilin, organizations can better prepare and protect themselves from this formidable ransomware.
T1021.004
Understanding the tactics and strategies of ransomware groups like Qilin is crucial for organizations looking to bolster their cybersecurity defenses. Implementing robust mitigation measures and staying vigilant are key steps in combating these threats effectively.
SOCRadar’s Attack Surface Management includes a specialized Ransomware Check function designed to help organizations protect against ransomware attacks, including those orchestrated by groups like Qilin. Our platform empowers you to proactively monitor potential attack vectors, detect suspicious activities, and take preemptive actions to safeguard your digital assets.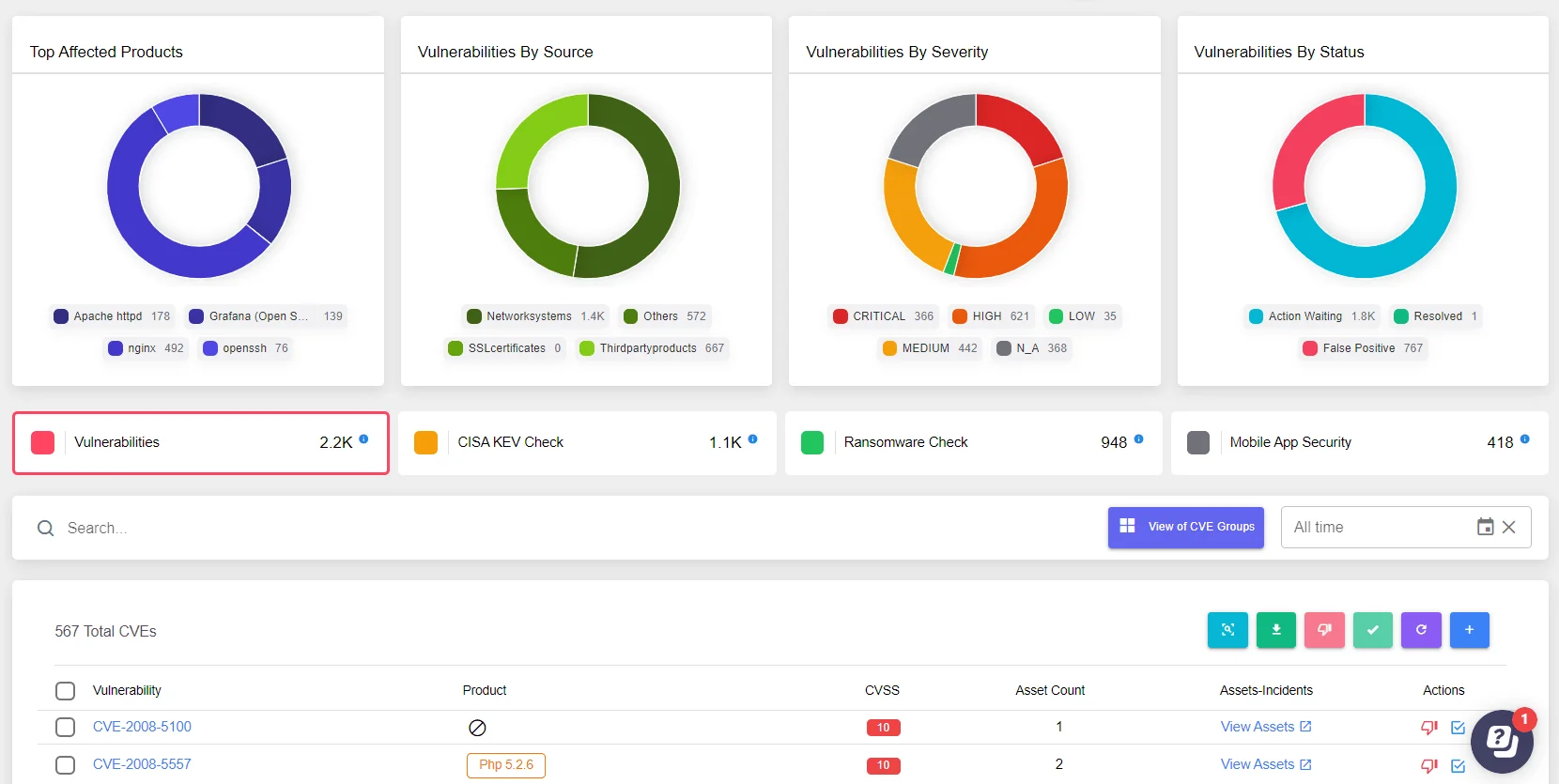
SOCRadar Attack Surface Management could give organizations an holistic overview
By leveraging SOCRadar’s intelligence-driven solutions, you can gain insights into threat actors’ methods and vulnerabilities, enabling you to fortify your cybersecurity posture. Our continuous monitoring and timely alerts ensure that you stay ahead of potential threats, allowing for swift responses and enhanced overall defense against ransomware and other cyber threats.
Integrating SOCRadar into your cybersecurity framework adds an additional layer of protection, helping you mitigate the risks posed by ransomware groups like Qilin and ensuring the resilience of your organization’s security defenses.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
