
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
[Update] July 22, 2024: “Play Ransomware Broadens Its Scope with New Linux Variant Targeting ESXi”
[Update] December 19, 2023: “Collaborative Advisory on Play Ransomware: 300 Entities Affected by October 2023.”
[Update] November 22, 2023: “Play Ransomware Shifts to RaaS Model.”
[Update] July 7, 2023: “Play Ransomware Lists 11 New Victims from Distinct Industries.”
While cyber-attacks are increasing nowadays, threat actors seek to implement different methods and techniques as well. Ransomware is one of the most common cyber-attacks that are not new but developing a cybercrime industry that threatens several sectors and governments. Today, we’ll introduce you to a new player: Play Ransomware.
On Jun 22, 2022, in the BleepingComputer forum, someone wrote that his files were encrypted with the extension “Play.” Afterward, Trend Micro published an analysis article about the new ransomware variant, Play Ransomware. The main target of Play Ransomware is the Latin American region, and Brazil is at the top of the list. Even though they seem like a new ransomware group, their identified TTPs look like Hive and Nokayawa ransomware families. One of the similar behaviors that make them look similar are they use AdFind, a command-line query tool capable of collecting information from Active Directory.
The Play Ransomware group uses a known valid account, exposed RDP servers, and FortiOS vulnerabilities CVE-2018-13379 and CVE-2020-12812 to gain initial access to an organization’s network. After getting access, they start using “lolbins” binaries like common ransomware group use as part of their attacks.
They distribute executables in the internal network via Group Policy Objects, then run scheduled tasks, PsExec or wmic. After they gain full access to the internal network, they encrypt files with the “.play” extension.
Double extortion is a popular technique in which cyber actors threaten to exfiltrate sensitive data. Play Ransomware also uses double extortion against its victims. They can archive the breached data with WinRAR and then upload it to file-sharing sites.
The researchers have found that the Play Ransomware group is the first threat actor resorting to intermittent encryption. This technique provides better evasion with partial encryption on the system that uses static analysis to detect ransomware infection.
Intermittent encryption is a new technique; based on the file size, it encrypts chunks of 0x100000 bytes.
For example:
The researchers observed that a sample encrypted every other 0x100000 byte chunk until the end of the file. The file consisted only of null characters, making the encrypted and non-encrypted chunks visually distinguishable.
Swiss authorities are investigating a cyber attack that targeted a Bernese IT firm, Xplain. The attack impacted several federal and cantonal government departments that worked with the same IT company, including the cantonal police, the Swiss army, customs, and the Federal Office of Police (Fedpol).
The Play Ransomware gang has claimed responsibility for the attack and published the stolen data from Fedpol and the Federal Office for Customs and Border Security (FOCBS) on a dark web forum.
Affected parties Fedpol and FOCBS downplayed the incident, Fedpol stating that only simulated and anonymous test data was accessed. However, the FOCBS acknowledged that exposed data included correspondence with clients.
Play Ransomware has recently added more companies to its leak site, claiming to have hacked them. After Xplain’s hack, these companies included other IT providers named Paragon Software Lanka, Soroc Technology, and a cloud hosting provider, Black Cat Networks.
Although the ransomware group did not disclose the size of data stolen from these organizations, they explained on leak posts that they stole private and confidential data, client and employee documents, as well as certain financial information from all the victims.
A major Spanish bank called Globalcaja has confirmed that it is facing a ransomware attack affecting multiple offices. The bank, located in Albacete, Spain, has over 300 branches nationwide and serves nearly 500,000 customers.
The Play ransomware group has claimed responsibility for the attack, stating that they have stolen private and confidential data, including client and employee documents, passports, and contracts.
The bank has stated that the attack has not affected customer transactions or electronic banking operations. They have activated security protocols, limited the performance of some operations, and are working to normalize the situation while prioritizing security. The bank has not commented on whether they will pay a ransom.
Another notable entry on the list is Poly (Polycom), a global communications firm based in the US. The ransomware operation posted Poly on the leak site on May 22, 2023, and claimed that they obtained 600GB of data, which included private and personal information, employee documents, social security numbers, IDs, passports, budget details, and financial information.
On Aug 13, 2022, Argentina’s Judiciary of Córdoba was targeted by Play Ransomware Group. They shut down Argentina’s Judiciary of Córdoba’s IT systems, databases, and online portals. Then they encrypted their files with “.play” extensions. After that, they left a simple ReadMe.txt to contact them.
The Play ransomware group recently came up with an alarming update on their Dark Web leak site: they added 11 new victims to the list. The victim organizations operate in diverse industries, and while nine originate from the United States, the remaining two are from the United Kingdom and Italy.
The list includes the manufacturer Indiana Dimension, Star Island Resort and Club, towing firm Lazer Tow, traffic control company Safety Network, logistics firm Capacity LLC, retailers Betty Lou’s Inc and MUJI UK, Geneva Software, hardware manufacturer Uniquify Inc, NST Law firm in the legal field, and Lawer SpA operating in the industrial sector.
The Play ransomware group claims to have successfully hacked the systems of these organizations and threatens to expose their private and personal data if the ransom demand is not paid, including sensitive client and employee documents, contracts, as well as financial, HR, and passport information in certain cases.
Researchers have uncovered a significant development, as Play Ransomware transitions to a Ransomware-as-a-Service (RaaS) model. A recent in-depth analysis, based on various Play ransomware attacks, reveals a striking uniformity in tactics and procedures across different sectors, indicating the use of predefined playbooks or instructions, possibly supplied by a RaaS kit.
In recent months, researchers have seen Play attacks with nearly identical TTPs, such as the use of the public music folder (C:…publicmusic) to hide the malicious file, the same password to create high-privilege accounts, and the same commands.
The victims who were targeted all had a similar profile. The targeting of smaller organizations with a financial capacity for ransom payments of around $1 million is particularly concerning.
For a detailed list of Indicators of Compromise, refer to the full research.
Play Ransomware was distinct from other operations with the involvement of its developers in executing attacks. Play’s transformation into a RaaS marks a notable shift as developers are now separated from attackers, while Play also becomes an enticing option for other threat actors. Consequently, the cybersecurity landscape must anticipate a surge in incidents and strengthen defenses accordingly.
CISA, FBI, and ASD’s ACSC have issued a collaborative advisory, #StopRansomware: Play Ransomware, to share indicators of compromise, detection methods, and TTPs used by Play ransomware with the public.
Since June 2022, the Play ransomware group, also known as Playcrypt, has impacted a diverse range of businesses and critical infrastructure across North America, South America, and Europe.
The CSA underscores that this ransomware group operates as a closed entity, aiming to ensure the confidentiality of its transactions. Unlike typical ransomware groups, instead of presenting an initial ransom demand or payment instructions, Play’s ransom notes instruct victims to reach out to the threat actors via email.
Most importantly, as of October 2023, the FBI is aware of approximately 300 entities that were exploited by the Play ransomware actors, showcasing their widespread impact.
The advisory further provides a list of tools and commands utilized by the threat actor, details characteristics, and methods employed for encryption and extortion. In addition to IoCs and TTPs, the advisory includes an extensive list of mitigation strategies.
Explore the joint cybersecurity advisory here.
A new variant of Play Ransomware has emerged, targeting VMware ESXi virtual machines. According to researchers, this is the first time Play Ransomware has targeted ESXi environments, marking a notable shift in their attack strategy to include the Linux platform.
Researchers at Trend Micro discovered this development, noting that the new variant can verify if it is executing on an ESXi environment and avoid detection on Linux systems. After successful deployment, the Linux variant scans the affected environment, shuts down all virtual machines, and encrypts files such as VM disks, configuration, and metadata.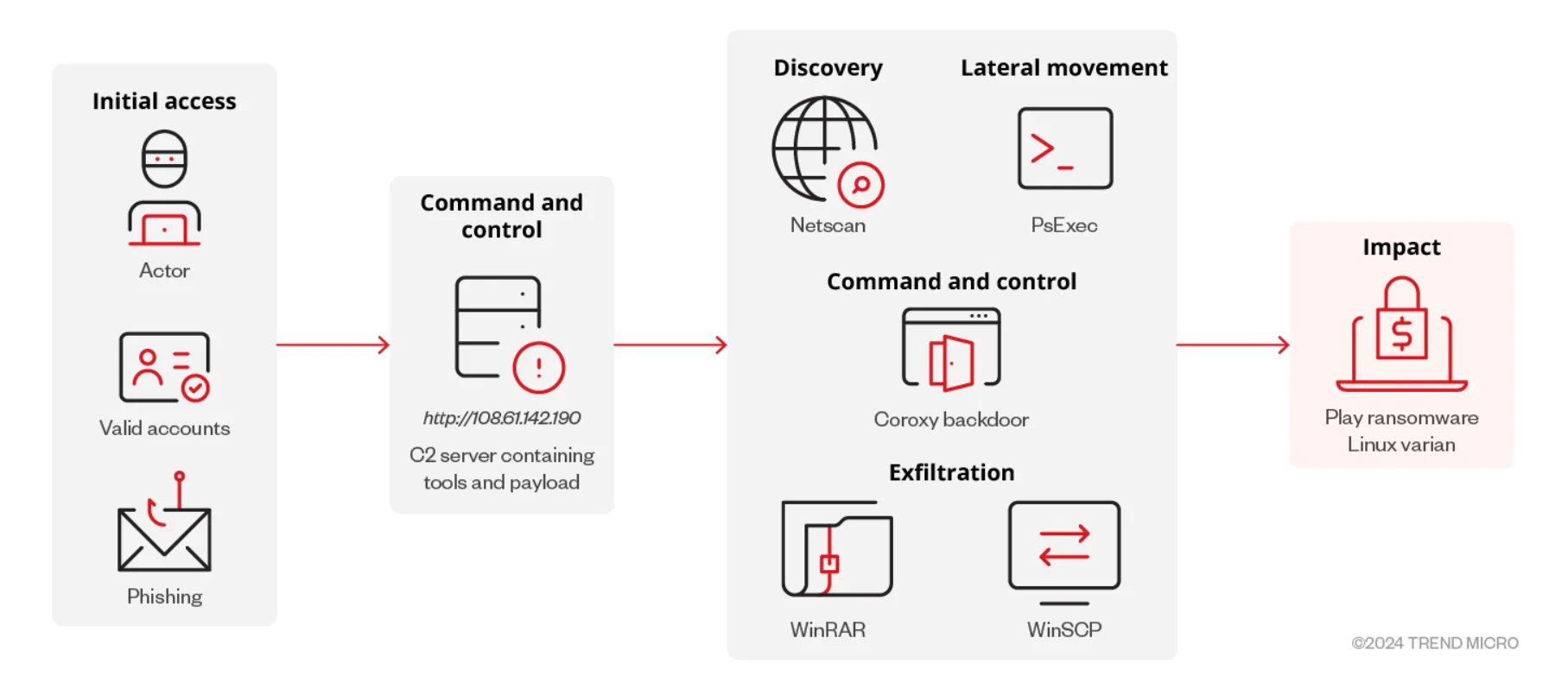
The full infection chain of Play Ransomware’s Linux variant (Trend Micro)
Encrypted files are appended with a ‘.PLAY’ extension, and a ransom note is left in the root directory of the VM, which appears in the ESXi client’s login portal and on the console post-reboot.
Among their findings, researchers have also noted that Play Ransomware uses URL-shortening services from a threat actor known as “Prolific Puma.” This threat actor, or group, is known to be active since at least January 2020.
Play Ransomware attacks emphasize the evolution of cyber threats. Recently, threat actors implement advanced evasion techniques to avoid detection by security tools. Therefore, you should deploy more security components like CTI platforms to get in intelligence about new threats from the dark web and learn about a specific threat against your company. Additionally, some curated mitigation steps are below.
Stay up to date with the latest happenings in the dark web, including the notorious Play Ransomware, through the comprehensive Dark Web News module offered by SOCRadar.
Dive into a wealth of information and stay informed about the latest updates, including Play Ransomware.
Hashes
URLs
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
