Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
Salt Typhoon, a Chinese state-sponsored Advanced Persistent Threat (APT), has been a formidable force in cyber espionage since its emergence in 2020. Known by various names such as GhostEmperor, FamousSparrow, and UNC2286, the group is linked to China’s Ministry of State Security and is believed to be a critical component of the country’s long-term cyber strategy. Salt Typhoon focuses on infiltrating critical communication networks and exfiltrating sensitive data, targeting entities across North America and Southeast Asia.
Employing sophisticated techniques, including the use of a Windows kernel-mode rootkit named Demodex, Salt Typhoon is adept at evading detection while conducting widespread data theft. Its campaigns have disrupted multiple sectors, exposing vulnerabilities in telecom infrastructure, broadband networks, and government systems. The group’s high-value targets include U.S. Internet Service Providers (ISPs), cloud service providers, and even political campaigns, reflecting its strategic emphasis on intelligence gathering and cyber warfare.
This profile delves into Salt Typhoon’s methods, notable campaigns, and the broader implications of its operations on global cybersecurity and national security frameworks.
Salt Typhoon, first identified as a state-sponsored actor linked to Chinese intelligence, targets critical communication infrastructure, including broadband networks and telecom providers. First revealed to the public in September 2024 by the Wall Street Journal (WSJ), Salt Typhoon has rapidly become one of the most concerning cyber threats globally. Unlike many threat actors disclosed by private cybersecurity firms, Salt Typhoon’s activities were brought to light through investigative journalism, highlighting their significant geopolitical implications.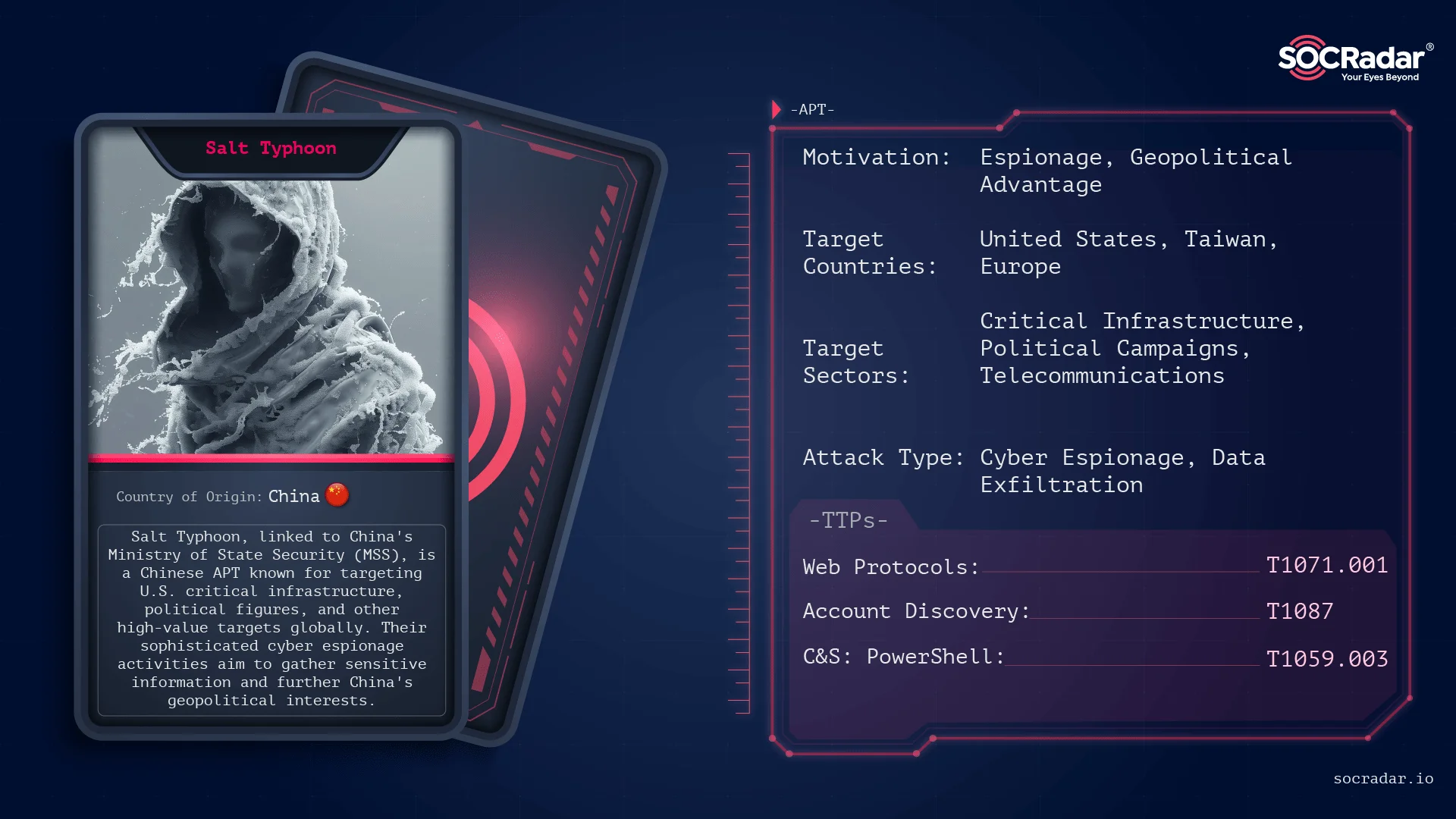
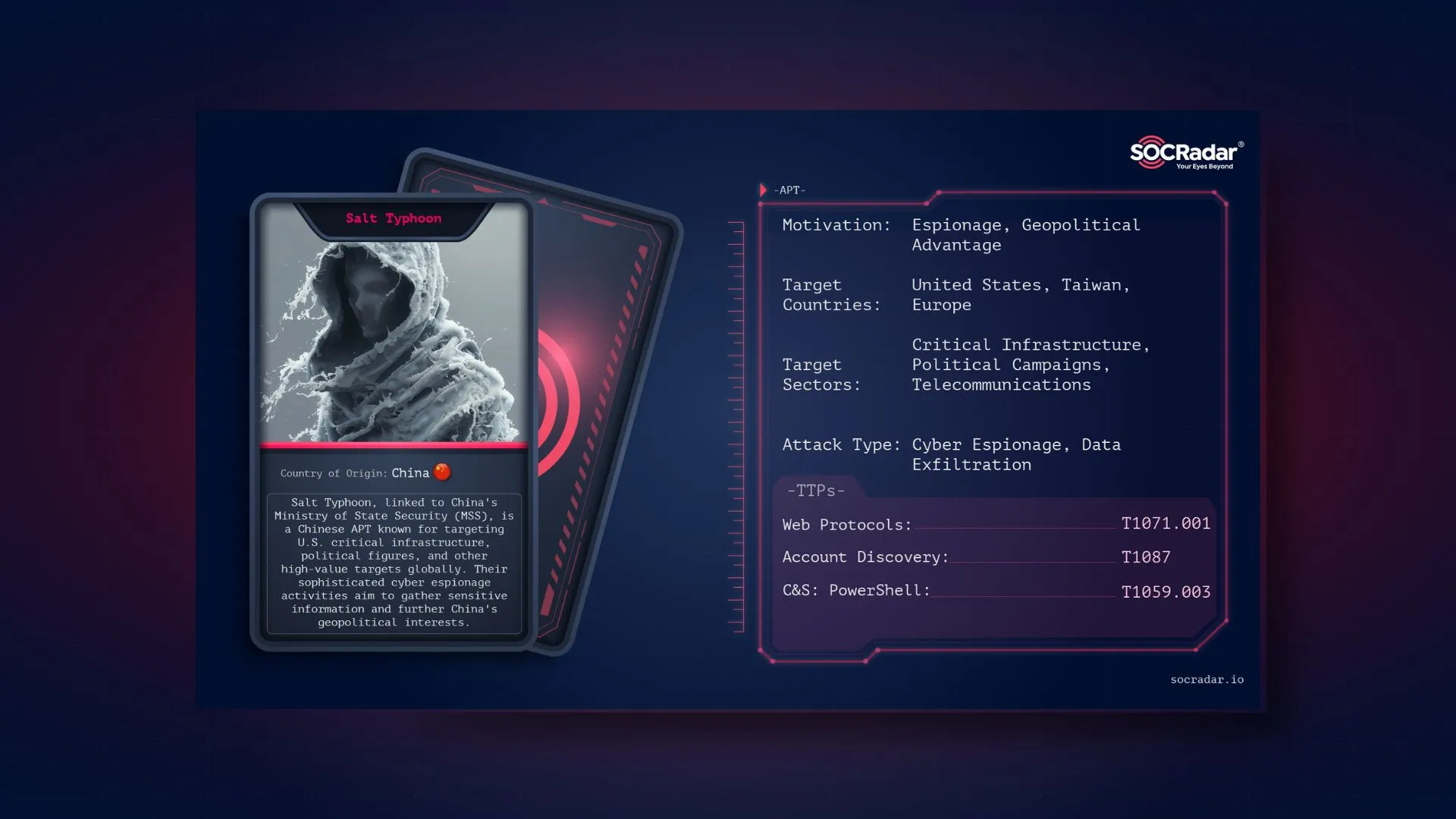
Threat actor card for Salt Typhoon
The group’s focus lies in intercepting call records, metadata, and sensitive communications. It has exploited vulnerabilities in systems associated with sensitive operations like court-authorized wiretaps, raising alarms about potential compromises in judicial and law enforcement networks. Experts speculate that Salt Typhoon is linked to high-profile Chinese APT groups, such as GhostEmperor and FamousSparrow, indicating shared methodologies and possibly a coordinated state-backed effort.
Salt Typhoon employs sophisticated tactics to infiltrate and maintain persistence within target environments. Key strategies include:
Salt Typhoon’s overlapping tactics with other Chinese APTs, such as UNC4841, suggest a shared operational pool of resources. Their methods focus on espionage, exfiltrating data for political, economic, and strategic advantage.
SOCRadar’s Threat Actor Intelligence provides detailed profiles and real-time insights into threat actors and APT groups such as Salt Typhoon, allowing organizations to identify adversaries’ TTPs and anticipate risks. This intelligence allows security teams to stay ahead of emerging threats to their sector.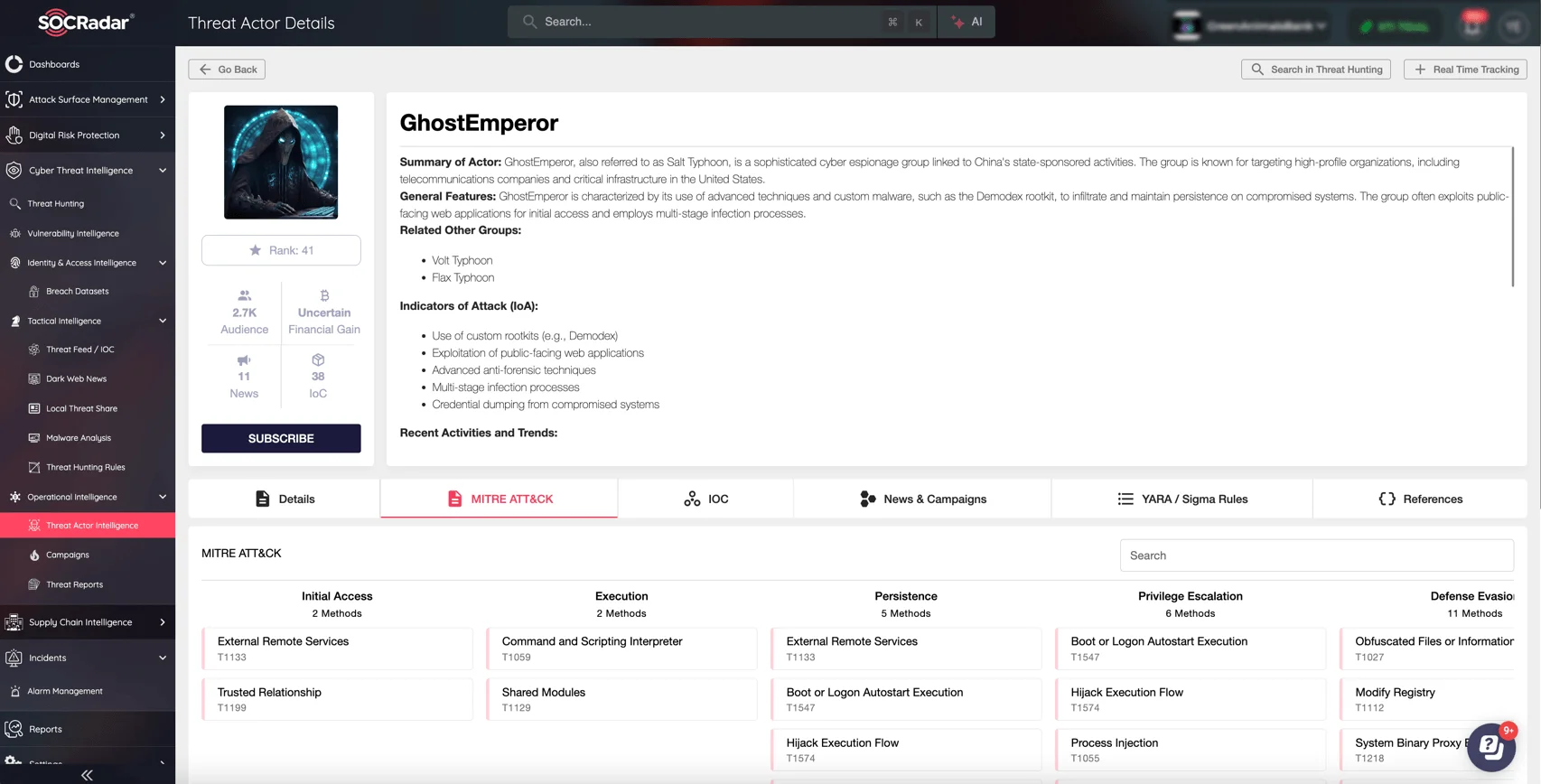
GhostEmperor (Salt Typhoon) details in SOCRadar’s Threat Actor Intelligence
Organizations can improve their defenses by monitoring campaigns and tracking the strategies of state-sponsored and criminal groups. Threat Actor Intelligence ensures a proactive response to evolving cyber threats, safeguarding critical infrastructure and sensitive information.
Salt Typhoon was linked to sophisticated operations using an advanced multi-stage malware toolkit. Salt Typhoon leveraged the Demodex rootkit, which operates at the Windows kernel level to bypass detection and maintain long-term persistence. This framework was first observed during attacks exploiting the ProxyLogon vulnerability in 2021 and has since been linked to activities targeting Southeast Asia, the Middle East, and North America.
The infection chain begins with exploiting public-facing servers, including Exchange and web servers, followed by deploying in-memory implants and malicious drivers. The group uses custom encryption and obfuscation techniques to evade forensic analysis, ensuring their operations remain undetected for extended periods. By employing these techniques, Salt Typhoon demonstrated a high level of technical expertise and a calculated approach to cyberespionage.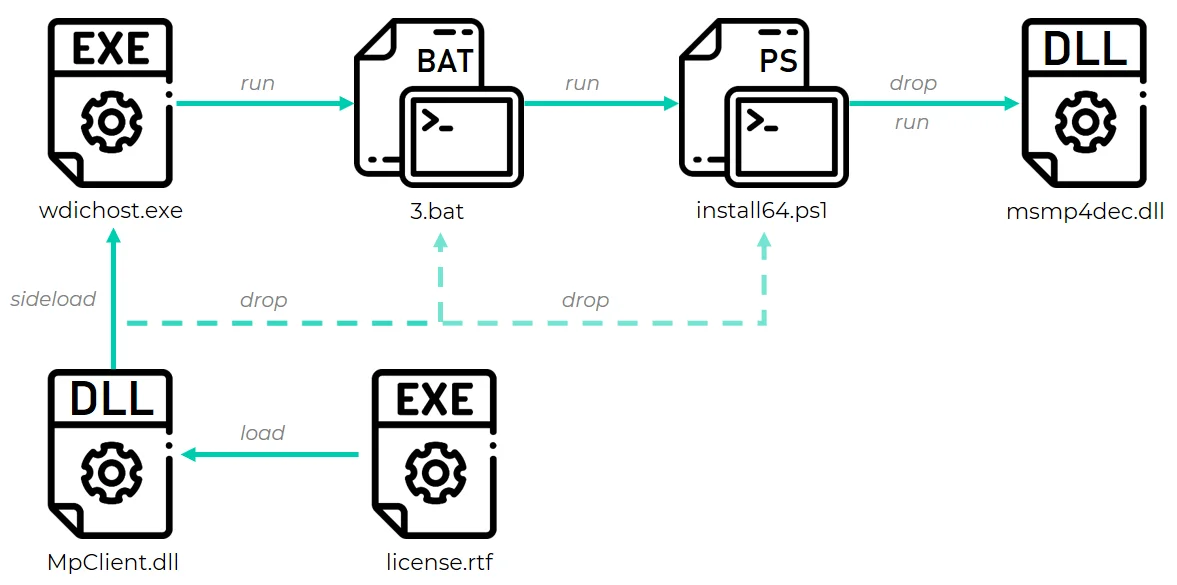
Illustration of a GhostEmperor infection chain initiated via a side-loaded DLL (Source: securelist)
Salt Typhoon’s campaign began with infiltrating major U.S. Internet Service Providers (ISPs), including AT&T, Verizon, and Lumen Technologies. Initially disclosed by the Wall Street Journal in September 2024, the breaches targeted systems managing court-authorized wiretaps, allowing unauthorized access to sensitive communications. This intrusion raised alarms about the misuse of surveillance backdoors, which are inherently vulnerable to exploitation.
The attack persisted for months, compromising core infrastructure and enabling the interception of call metadata and generic internet traffic. Researchers linked these breaches to advanced malware capable of harvesting passwords and spreading malicious code through ISP networks. The scale and sensitivity of the operation highlighted the vulnerabilities of critical U.S. infrastructure.
In November 2024, Salt Typhoon expanded its operations to target T-Mobile, exfiltrating customer call records and metadata. Metadata attacks further underscored the group’s focus on high-value data, revealing insights into the personal and professional networks of individuals of interest to Chinese intelligence. This campaign affected at least eight U.S. telecommunications companies and involved exploiting both broadband networks and backend telecom systems. Metadata, while lacking content details, provides critical context about call durations, recipient numbers, and locations, making it invaluable for espionage.
Salt Typhoon’s intrusion into telecom networks was labeled “historically significant” due to its potential to disrupt critical infrastructure and harvest sensitive government and political communications. By October 2024, reports emerged of their attempts to compromise the phones of U.S. political figures, including President-elect Donald Trump and Vice President Kamala Harris’s campaign staff. These brazen attacks, coinciding with the U.S. election period, suggest a deliberate psychological and strategic operation designed to undermine confidence in American cybersecurity and governance.
Salt Typhoon’s operational methods align with advanced threat actor profiles. Key TTPs include:
Public knowledge of Salt Typhoon’s activities has largely been driven by media reports rather than traditional cybersecurity firm disclosures. The Wall Street Journal first revealed the group’s existence in September 2024, followed by further details of compromised ISPs, telecom providers, and political entities. These revelations highlight not only the group’s technical sophistication but also its strategic intent to leverage stolen data for geopolitical gain.
The U.S. government responded by forming a unified coordination group, including the FBI, NSA, and CISA, to investigate and mitigate the breaches. Despite ongoing efforts, Salt Typhoon’s ability to re-enter patched systems and target prominent political figures underscores the need for enhanced vigilance.
Defending against Salt Typhoon requires a comprehensive, multi-layered strategy:
Isolating critical systems and continuously monitoring network activity is crucial to detect and mitigate threats early. Employing tools to analyze unusual behavior, such as changes in router configurations or unauthorized access attempts, can help in identifying potential compromises.
Timely updates are essential to protect against zero-day vulnerabilities exploited by advanced actors like Salt Typhoon. Critical infrastructure, particularly telecom and broadband systems, should prioritize securing known vulnerabilities.
Implementing strict access controls and regularly verifying the integrity of accounts and devices can minimize risks. Encrypting communications and enforcing least privilege policies are key components of a Zero Trust framework.
Using platforms like SOCRadar to gain actionable insights into Salt Typhoon’s TTPs can help organizations stay ahead of potential threats. Real-time threat intelligence enhances the ability to implement targeted defensive measures.
Salt Typhoon campaigns show how sophisticated threat actors use compromised infrastructure to target sensitive communications and data. While their activities are primarily focused on exploiting compromised systems, the fallout frequently appears on the dark web. Credentials, metadata, and even insider knowledge can make their way into underground forums, posing additional risks to organizations.
SOCRadar’s Dark Web Monitoring provides unparalleled visibility into the internet’s hidden corners. By constantly scanning dark web forums, marketplaces, and stealer logs, the platform assists organizations: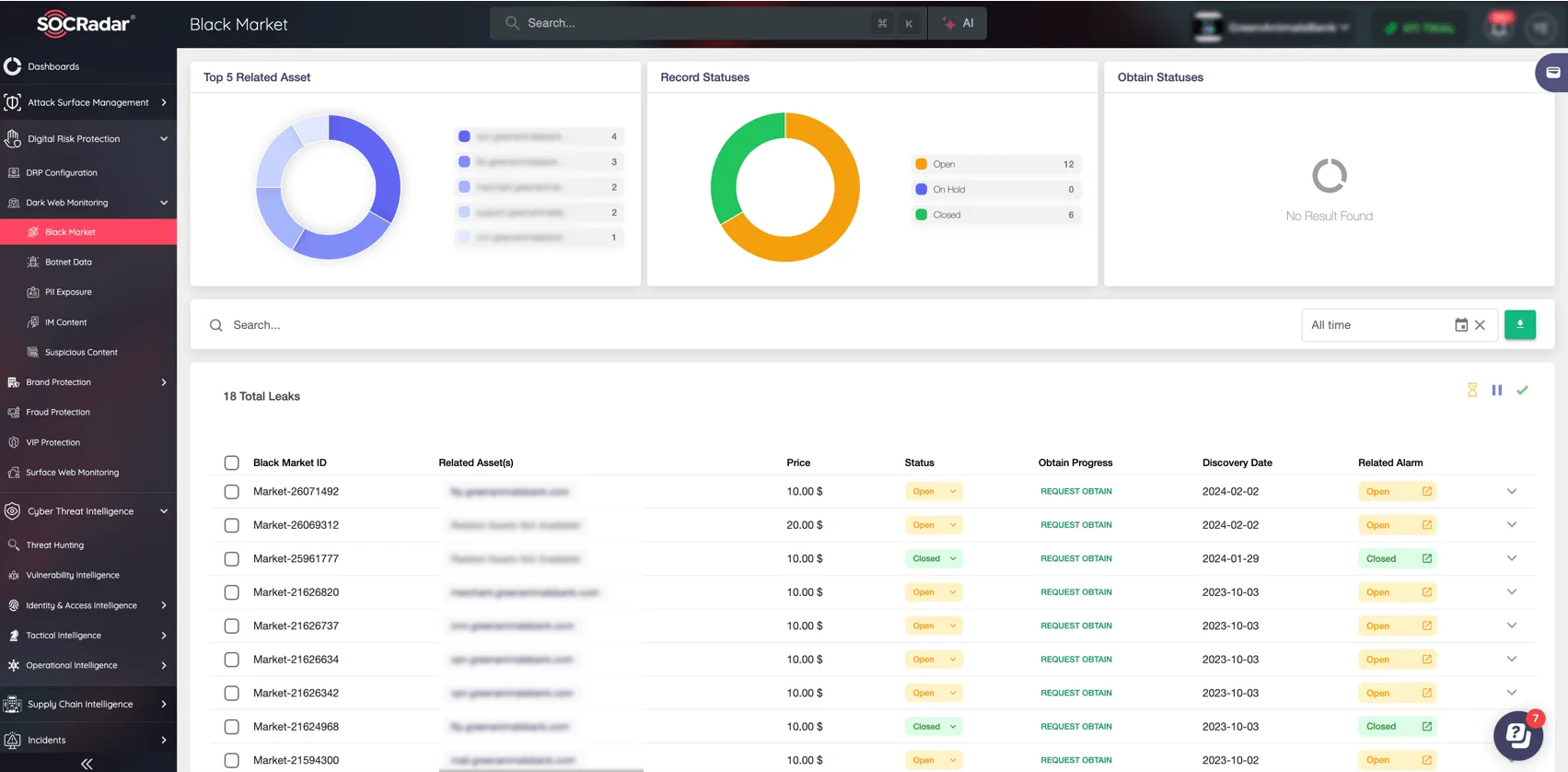
SOCRadar’s Dark Web Monitoring module
SOCRadar’s Dark Web Monitoring provides actionable insights, allowing your organization to stay ahead of cybercriminals’ activities and mitigate threats before they escalate. By implementing this proactive defense solution, you can protect your assets and ensure operational security.
In response to Salt Typhoon’s widespread attacks on U.S. telecom operators, the Cybersecurity and Infrastructure Security Agency (CISA), alongside the NSA, FBI, and international partners, issued updated security guidelines for Communications Service Providers (CSPs). These guidelines highlight the need for:
These recommendations also include specific measures for Cisco systems exploited by Salt Typhoon, emphasizing the application of hardening best practices to mitigate risks. Organizations, especially operators of critical national infrastructure, are urged to adopt these strategies to safeguard against future incursions.
By combining these tailored CISA recommendations with a proactive defense framework, organizations can better prepare for and mitigate the risks posed by advanced persistent threats like Salt Typhoon.
Salt Typhoon exemplifies the evolving threat landscape, where state-sponsored actors exploit critical infrastructure for espionage and strategic gain. Its campaigns, ranging from telecom breaches to metadata attacks, highlight the vulnerabilities in national infrastructure and the pressing need for robust defense measures.
To combat Salt Typhoon and similar APTs, organizations must invest in threat intelligence, adopt proactive defense strategies, and foster collaboration between private and public sectors. As this cyberstorm continues to churn, preparation and vigilance remain the best defense.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
